前面我已經介紹了haproxy結合keepalive做簡單的雙主高可用,如果不清楚的話,可以去我的上一
篇博客http://3381847248.blog.51cto.com/13408601/1977014看看,根據haproxy的性能和特點,我們可以對haproxy進行優化調整,體現出haproxy的價值。
假設一家公司有多臺後端web服務器(或者多臺圖片服務器),每一臺web服務器都有自己唯一的域
名,在還沒有做haproxy之前,我們需要把域名的對應關係給寫到hosts文件裏或者需要在DNS服務器上進
行配置,這樣的話,就會給我們後端的服務器帶來一定的風險;通過haproxy,我們可以把域名都解析到
haproxy服務器上,然後通過haproxy服務器進行轉發,當我需要訪問某個域名的時候,haproxy服務器就
會跳到那個域名所對應的後端服務器上,而我後端服務器只開放所需要的端口,這樣就大大減少了對後
端服務器的風險了。
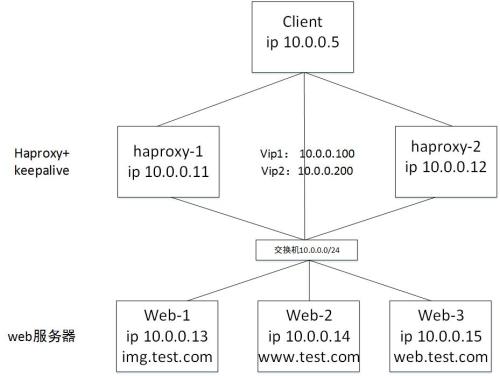
實驗環境
拓撲圖:
| 主機 | ip | 域名 | 角色 | |
| haproxy-1 | 10.0.0.11 | haproxy+keepalive | vip1:10.0.0.100 vip2:10.0.0.200 | |
| haproxy-2 | 10.0.0.12 | haproxy+keepalive | ||
| web-1 | 10.0.0.13 | img.test.com | web服務器 | |
| web-2 | 10.0.0.14 | www.test.com | web服務器 | |
| web-3 | 10.0.0.15 | web.test.com | web服務器 | |
| client | 10.0.0.5 | client |
開始配置
1、配置好各主機ip地址,關閉selinux和防火牆,修改hosts文件
##修改hosts文件
[root@haproxy-1 ~]# cat /etc/hosts 127.0.0.1 localhost localhost.localdomain localhost4 localhost4.localdomain4 ::1 localhost localhost.localdomain localhost6 localhost6.localdomain6 10.0.0.100 img.test.com www.test.com web.test.com 10.0.0.200 img.test.com www.test.com web.test.com [root@haproxy-2 ~]# cat /etc/hosts 127.0.0.1 localhost localhost.localdomain localhost4 localhost4.localdomain4 ::1 localhost localhost.localdomain localhost6 localhost6.localdomain6 10.0.0.100 img.test.com www.test.com web.test.com 10.0.0.200 img.test.com www.test.com web.test.com [root@web1 ~]# cat /etc/hosts 127.0.0.1 localhost localhost.localdomain localhost4 localhost4.localdomain4 ::1 localhost localhost.localdomain localhost6 localhost6.localdomain6 10.0.0.13 img.test.com [root@web2 ~]# cat /etc/hosts 127.0.0.1 localhost localhost.localdomain localhost4 localhost4.localdomain4 ::1 localhost localhost.localdomain localhost6 localhost6.localdomain6 10.0.0.14 www.test.com [root@web-3 ~]# cat /etc/hosts 127.0.0.1 localhost localhost.localdomain localhost4 localhost4.localdomain4 ::1 localhost localhost.localdomain localhost6 localhost6.localdomain6 10.0.0.15 web.test.com [root@client ~]# cat /etc/hosts 127.0.0.1 localhost localhost.localdomain localhost4 localhost4.localdomain4 ::1 localhost localhost.localdomain localhost6 localhost6.localdomain6 10.0.0.100 img.test.com www.test.com web.test.com 10.0.0.200 img.test.com www.test.com web.test.com
2、配置web服務器
##安裝Apache yum install -y httpd ##具體配置略 ##查看web網頁 [root@web1 ~]# curl 10.0.0.13 10.0.0.13 img.test.com [root@web2 ~]# curl 10.0.0.14 10.0.0.14 www.test.com [root@web-3 ~]# curl 10.0.0.15 10.0.0.15:80 web.test.com [root@web-3 ~]# curl 10.0.0.15:8080 10.0.0.15:8080
3、配置haproxy
3.1、安裝haproxy
yum install -y haproxy
##性能調優相關參數:
maxconn <number>: //設定單haproxy進程的最大併發連接數;
maxconnrate <number>: //設定單haproxy進程每秒接受的連接數;
maxsslconn <number>: //設定單haproxy進程的ssl連接最大併發連接數;
maxsslrate <number>: //單haproxy進程的ssl連接的創建速率上限;
spread-checks <0..50, in percent>
tune.rcvbuf.client <number> //接收客戶端請求的緩衝大小
tune.rcvbuf.server <number> //接收服務端響應的緩衝大小
tune.sndbuf.client <number> //向客戶端發送響應的緩衝大小
tune.sndbuf.server <number> //向服務端發送請求的緩衝大小
tune.ssl.cachesize <number> //ssl會話的緩存大小
tune.ssl.lifetime <timeout> //ssl會話緩存的有效時長
##配置參數:
bind:
作用:設定監聽的地址和端口;
語法:bind [<address>]:<port_range> [, ...]
使用位置:frontend,listen
mode { tcp|http|health }
作用:定義haproxy的工作模型:
tcp:基於layer4實現代理,可代理大多數基於tcp的應用層協議,例如ssh,mysql,pgsql等;
http:客戶端的http請求會被深度解析;
health:工作爲健康狀態檢查響應模式,當請求到達時僅迴應“OK”即斷開連接;
開啓統計頁面,相關信息:
maxconn <conns>:最大併發連接數,默認爲2000,使用位置:frontend、default、listen
stats enable:作用:啓用內建的統計頁,在缺少其它必要的參數時,會使用默認配置;
默認配置:
- stats uri : /haproxy?stats
- stats realm : "HAProxy Statistics"
- stats auth : no authentication
- stats scope : no restriction
說明:
stats uri <prefix>:自定義stats頁面的uri;
stats realm <realm>:啓用統計信息並設置身份認證域。
stats auth <user>:<passwd>:定義認證使用的賬號和密碼;
stats hide-version:隱藏版本信息
stats refresh <delay>:自動刷新相關頁面的時間間隔;
stats admin { if | unless } <cond>:條件滿足時啓用stats內建的管理功能接口;不建議啓用,有安全隱患
##ACL匹配的如下所示:
1、ACL derivatives :
path : exact string match(字符竄精確匹配)
path_beg : prefix match(前綴匹配)
path_dir : subdir match(子目錄匹配)
path_dom : domain match(域匹配)
path_end : suffix match(後綴匹配)
path_len : length match(長度匹配)
path_reg : regex match(正則匹配)
path_sub : substring match(子串匹配)
例如:
acl test_path path -i /test.txt ##匹配具體路徑
acl test_path_beg path_beg -i /test. #匹配前綴包含
acl test_path_end path_end -i .html ##匹配.html結尾
2、可以基於字符串做檢測:
req.hdr([<name>[,<occ>]]) : string
對請求報文中的內容做檢查
This extracts the last occurrence of header <name> in an HTTP request.
ACL derivatives :
hdr([<name>[,<occ>]]) : exact string match
hdr_beg([<name>[,<occ>]]) : prefix match
hdr_dir([<name>[,<occ>]]) : subdir match
hdr_dom([<name>[,<occ>]]) : domain match
hdr_end([<name>[,<occ>]]) : suffix match
hdr_len([<name>[,<occ>]]) : length match
hdr_reg([<name>[,<occ>]]) : regex match
hdr_sub([<name>[,<occ>]]) : substring match
res.hdr([<name>[,<occ>]]) : string
對響應報文中的內容做檢測
ACL derivatives :
shdr([<name>[,<occ>]]) : exact string match
shdr_beg([<name>[,<occ>]]) : prefix match
shdr_dir([<name>[,<occ>]]) : subdir match
shdr_dom([<name>[,<occ>]]) : domain match
shdr_end([<name>[,<occ>]]) : suffix match
shdr_len([<name>[,<occ>]]) : length match
shdr_reg([<name>[,<occ>]]) : regex match
shdr_sub([<name>[,<occ>]]) : substring match3.2、配置haproxy日誌文件
##添加日誌(haproxy.cfg): [root@haproxy-1 haproxy]# vim haproxy.cfg log 127.0.0.1 local2 ##修改syslog.conf: [root@haproxy-1 haproxy]# vim /etc/rsyslog.conf # Provides UDP syslog reception $ModLoad imudp $UDPServerRun 514 # Provides TCP syslog reception $ModLoad imtcp $InputTCPServerRun 514 local2.* /var/log/haproxy.log ##重啓兩個服務即可看到日誌文件: [root@haproxy-1 ~]# systemctl restart rsyslog [root@haproxy-1 ~]# systemctl restart haproxy [root@haproxy-1 ~]# cd /var/log/ [root@haproxy-1 log]# ls haproxy.log haproxy.log ##把日誌文件配置同步到主機haproxy-2上 [root@haproxy-1 ~]# scp /etc/haproxy/haproxy.cfg 10.0.0.12:/etc/haproxy/haproxy.cfg [root@haproxy-1 ~]# scp /etc/rsyslog.conf 10.0.0.12:/etc/rsyslog.conf [root@haproxy-2 ~]# systemctl restart rsyslog [root@haproxy-2 ~]# systemctl restart haproxy
3.3、配置haproxy(兩臺機的配置是一樣的)
[root@haproxy-1 ~]# cat /etc/haproxy/haproxy.cfg #--------------------------------------------------------------------- # Example configuration for a possible web application. See the # full configuration options online. # # http://haproxy.1wt.eu/download/1.4/doc/configuration.txt # #--------------------------------------------------------------------- #--------------------------------------------------------------------- # Global settings #--------------------------------------------------------------------- global # to have these messages end up in /var/log/haproxy.log you will # need to: # # 1) configure syslog to accept network log events. This is done # by adding the '-r' option to the SYSLOGD_OPTIONS in # /etc/sysconfig/syslog # # 2) configure local2 events to go to the /var/log/haproxy.log # file. A line like the following can be added to # /etc/sysconfig/syslog # # local2.* /var/log/haproxy.log # log 127.0.0.1 local2 chroot /var/lib/haproxy pidfile /var/run/haproxy.pid maxconn 4000 user haproxy group haproxy daemon # turn on stats unix socket stats socket /var/lib/haproxy/stats #--------------------------------------------------------------------- # common defaults that all the 'listen' and 'backend' sections will # use if not designated in their block #--------------------------------------------------------------------- defaults mode http log global option httplog option dontlognull option http-server-close option forwardfor except 127.0.0.0/8 option redispatch retries 3 timeout http-request 10s timeout queue 1m timeout connect 10s timeout client 1m timeout server 1m timeout http-keep-alive 10s timeout check 10s maxconn 3000 #--------------------------------------------------------------------- # main frontend which proxys to the backends #--------------------------------------------------------------------- frontend main *:80 stats enable ##添加監控頁面 stats uri /test?stats ##自定義URL stats realm Stats\ Page\ Area ##去掉空格轉譯 stats auth admin:admin ##配置賬號密碼 stats refresh 5s ##沒5s刷新一次 stats hide-version ##隱藏版本信息 stats admin if TRUE maxconn 10000 ##定義最大併發爲10000 acl url_static path_beg -i /static /images /javascript /stylesheets ##匹配目錄是如下的地址 acl url_static path_end -i .jpg .gif .png .css .js ##匹配結尾是.jpg.gif的地址 acl usr_www hdr(host) -i www.test.com acl usr_img hdr(host) -i img.test.com acl usr_web hdr_end(host) -i .test.com ##所有訪問test.com的二級域名的,都轉發到hdr_end這個位置 use_backend img if usr_img use_backend www if usr_www use_backend web if usr_web use_backend static if url_static default_backend web backend static balance roundrobin server static 127.0.0.1:4331 check backend img balance roundrobin server web-1 10.0.0.13:80 check inter 2000 rise 3 fall 3 weight 3 #check inter 2000 是檢測心跳頻率(check 默認 ); #rise 3 表示 3次正確認爲服務器可用; #fall 3 表示 3次失敗認爲服務器不可用; #weight 表示權重。 backend www balance roundrobin server web-2 10.0.0.14:80 check inter 2000 rise 3 fall 3 weight 3 backend web balance roundrobin server web-3 10.0.0.15:80 check inter 2000 rise 3 fall 3 weight 3 server web-3 10.0.0.15:8080 check inter 2000 rise 3 fall 3 weight 3
##啓動haproxy
[root@haproxy-1 haproxy]# systemctl restart haproxy [root@haproxy-2 ~]# systemctl restart haproxy
3.4、配置keepalive
##安裝keepalive [root@haproxy-1 ~]# yum install -y keepalived [root@haproxy-2 ~]# yum install -y keepalived
##haproxy-1的keepalive配置文件
[root@haproxy-1 ~]# cat /etc/keepalived/keepalived.conf
! Configuration File for keepalived
vrrp_script check_haproxy {
script "/etc/keepalived/check_haproxy.sh"
interval 2
weight 2
}
global_defs {
notification_email {
[email protected]
}
router_id LVS_DEVEL
}
vrrp_instance VI_1 {
state MASTER
interface ens33
virtual_router_id 50
nopreempt
priority 150
advert_int 1
authentication {
auth_type PASS
auth_pass 123456
}
virtual_ipaddress {
10.0.0.100
}
track_script {
check_haproxy
}
}
vrrp_instance VI_2 {
state BACKUP
interface ens33
virtual_router_id 51
nopreempt
priority 100
advert_int 1
authentication {
auth_type PASS
auth_pass 123456
}
virtual_ipaddress {
10.0.0.200
}
track_script {
check_haproxy
}
}##haproxy-2的keepalive配置文件
[root@haproxy-2 ~]# cat /etc/keepalived/keepalived.conf
! Configuration File for keepalived
vrrp_script check_haproxy {
script "/etc/keepalived/check_haproxy.sh"
interval 2
weight 2
}
global_defs {
notification_email {
[email protected]
}
router_id LVS_DEVEL
}
vrrp_instance VI_1 {
state BACKUP
interface ens33
virtual_router_id 50
nopreempt
priority 100
advert_int 1
authentication {
auth_type PASS
auth_pass 123456
}
virtual_ipaddress {
10.0.0.100
}
track_script {
check_haproxy
}
}
vrrp_instance VI_2 {
state MASTER
interface ens33
virtual_router_id 51
nopreempt
priority 150
advert_int 1
authentication {
auth_type PASS
auth_pass 123456
}
virtual_ipaddress {
10.0.0.200
}
track_script {
check_haproxy
}
}##haproxy檢測腳本
[root@haproxy-1 ~]# cat /etc/keepalived/check_haproxy.sh #!/bin/bash h=`ps -C haproxy --no-header |wc -l` if [ $h -eq 0 ];then systemctl stop keepalived fi [root@haproxy-1 ~]# chmod a+x /etc/keepalived/check_haproxy.sh [root@haproxy-2 ~]# cat /etc/keepalived/check_haproxy.sh #!/bin/bash h=`ps -C haproxy --no-header |wc -l` if [ $h -eq 0 ];then systemctl stop keepalived fi [root@haproxy-2 ~]# chmod a+x /etc/keepalived/check_haproxy.sh
##啓動keepalive
[root@haproxy-1 ~]# systemctl restart keepalived [root@haproxy-1 ~]# systemctl status keepalived ● keepalived.service - LVS and VRRP High Availability Monitor Loaded: loaded (/usr/lib/systemd/system/keepalived.service; disabled; vendor preset: disabled) Active: active (running) since Sat 2017-10-28 16:00:23 CST; 12s ago Process: 3806 ExecStart=/usr/sbin/keepalived $KEEPALIVED_OPTIONS (code=exited, status=0/SUCCESS) Main PID: 3807 (keepalived) CGroup: /system.slice/keepalived.service ├─3807 /usr/sbin/keepalived -D ├─3808 /usr/sbin/keepalived -D └─3809 /usr/sbin/keepalived -D Oct 28 16:00:28 haproxy-1 Keepalived_vrrp[3809]: Sending gratuitous ARP on ens33 for 10.0.0.200 Oct 28 16:00:29 haproxy-1 Keepalived_vrrp[3809]: VRRP_Instance(VI_2) Received advert with higher priori... 102 Oct 28 16:00:29 haproxy-1 Keepalived_vrrp[3809]: VRRP_Instance(VI_2) Entering BACKUP STATE Oct 28 16:00:29 haproxy-1 Keepalived_vrrp[3809]: VRRP_Instance(VI_2) removing protocol VIPs. Oct 28 16:00:30 haproxy-1 Keepalived_vrrp[3809]: Sending gratuitous ARP on ens33 for 10.0.0.100 Oct 28 16:00:30 haproxy-1 Keepalived_vrrp[3809]: VRRP_Instance(VI_1) Sending/queueing gratuitous ARPs o....100 Oct 28 16:00:30 haproxy-1 Keepalived_vrrp[3809]: Sending gratuitous ARP on ens33 for 10.0.0.100 Oct 28 16:00:30 haproxy-1 Keepalived_vrrp[3809]: Sending gratuitous ARP on ens33 for 10.0.0.100 Oct 28 16:00:30 haproxy-1 Keepalived_vrrp[3809]: Sending gratuitous ARP on ens33 for 10.0.0.100 Oct 28 16:00:30 haproxy-1 Keepalived_vrrp[3809]: Sending gratuitous ARP on ens33 for 10.0.0.100 Hint: Some lines were ellipsized, use -l to show in full. [root@haproxy-1 ~]# ip addr 1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN qlen 1 link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00 inet 127.0.0.1/8 scope host lo valid_lft forever preferred_lft forever inet6 ::1/128 scope host valid_lft forever preferred_lft forever 2: ens33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen 1000 link/ether 00:0c:29:1d:7a:63 brd ff:ff:ff:ff:ff:ff inet 10.0.0.11/24 brd 10.0.0.255 scope global ens33 valid_lft forever preferred_lft forever inet 10.0.0.100/32 scope global ens33 valid_lft forever preferred_lft forever inet6 fe80::8ec5:50ac:d71:20d7/64 scope link valid_lft forever preferred_lft forever inet6 fe80::f87c:449f:eb4a:ba03/64 scope link tentative dadfailed valid_lft forever preferred_lft forever
[root@haproxy-2 ~]# systemctl restart keepalived [root@haproxy-2 ~]# systemctl status keepalived ● keepalived.service - LVS and VRRP High Availability Monitor Loaded: loaded (/usr/lib/systemd/system/keepalived.service; disabled; vendor preset: disabled) Active: active (running) since Sat 2017-10-28 16:00:28 CST; 19s ago Process: 27168 ExecStart=/usr/sbin/keepalived $KEEPALIVED_OPTIONS (code=exited, status=0/SUCCESS) Main PID: 27169 (keepalived) CGroup: /system.slice/keepalived.service ├─27169 /usr/sbin/keepalived -D ├─27170 /usr/sbin/keepalived -D └─27171 /usr/sbin/keepalived -D Oct 28 16:00:29 haproxy-2 Keepalived_vrrp[27171]: Sending gratuitous ARP on ens33 for 10.0.0.200 Oct 28 16:00:29 haproxy-2 Keepalived_vrrp[27171]: Sending gratuitous ARP on ens33 for 10.0.0.200 Oct 28 16:00:29 haproxy-2 Keepalived_vrrp[27171]: Sending gratuitous ARP on ens33 for 10.0.0.200 Oct 28 16:00:29 haproxy-2 Keepalived_vrrp[27171]: Sending gratuitous ARP on ens33 for 10.0.0.200 Oct 28 16:00:34 haproxy-2 Keepalived_vrrp[27171]: Sending gratuitous ARP on ens33 for 10.0.0.200 Oct 28 16:00:34 haproxy-2 Keepalived_vrrp[27171]: VRRP_Instance(VI_2) Sending/queueing gratuitous ARPs o...200 Oct 28 16:00:34 haproxy-2 Keepalived_vrrp[27171]: Sending gratuitous ARP on ens33 for 10.0.0.200 Oct 28 16:00:34 haproxy-2 Keepalived_vrrp[27171]: Sending gratuitous ARP on ens33 for 10.0.0.200 Oct 28 16:00:34 haproxy-2 Keepalived_vrrp[27171]: Sending gratuitous ARP on ens33 for 10.0.0.200 Oct 28 16:00:34 haproxy-2 Keepalived_vrrp[27171]: Sending gratuitous ARP on ens33 for 10.0.0.200 Hint: Some lines were ellipsized, use -l to show in full. [root@haproxy-2 ~]# ip addr 1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN qlen 1 link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00 inet 127.0.0.1/8 scope host lo valid_lft forever preferred_lft forever inet6 ::1/128 scope host valid_lft forever preferred_lft forever 2: ens33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen 1000 link/ether 00:0c:29:76:bf:48 brd ff:ff:ff:ff:ff:ff inet 10.0.0.12/24 brd 10.0.0.255 scope global ens33 valid_lft forever preferred_lft forever inet 10.0.0.200/32 scope global ens33 valid_lft forever preferred_lft forever inet6 fe80::f87c:449f:eb4a:ba03/64 scope link valid_lft forever preferred_lft forever
##在client上訪問
[root@client ~]# curl img.test.com 10.0.0.13 img.test.com [root@client ~]# curl www.test.com 10.0.0.14 www.test.com [root@client ~]# curl web.test.com 10.0.0.15:80 web.test.com [root@client ~]# curl web.test.com 10.0.0.15:8080 [root@client ~]# curl web.test.com 10.0.0.15:80 web.test.com [root@client ~]# curl web.test.com 10.0.0.15:8080
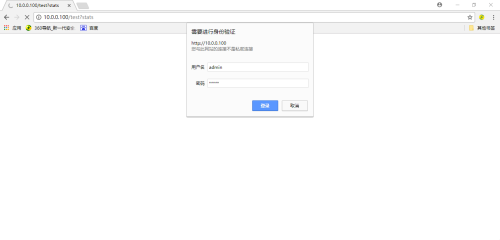
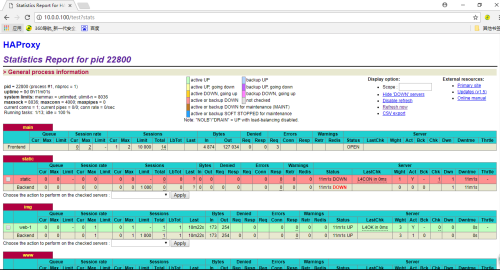
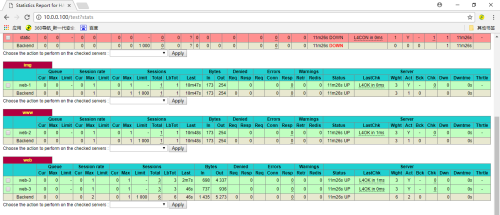
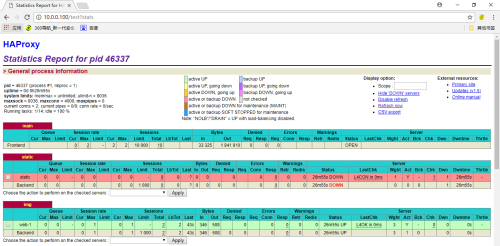
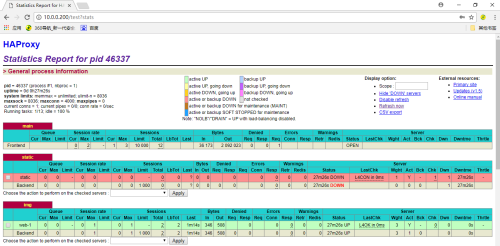
##查看監控界面,打開瀏覽器,輸入10.0.0.100/test?stats,輸入之前設置的賬號密碼(admin:admin),如圖1,之後就可以看到我們配置的haproxy的內容了,如圖2和圖3。
圖1
圖2
圖3
驗證
當haproxy-1上的haproxy服務宕掉了之後,vip1就會從haproxy-1上飄到haproxy-2上,也就是說haproxy-2上有兩個vip,而且還能正常訪問web服務
##在haproxy-1上查看keepalive和vip的狀態,可以看到vip已經不在了
[root@haproxy-1 ~]# systemctl stop haproxy [root@haproxy-1 ~]# systemctl status keepalived ● keepalived.service - LVS and VRRP High Availability Monitor Loaded: loaded (/usr/lib/systemd/system/keepalived.service; disabled; vendor preset: disabled) Active: inactive (dead) Oct 28 16:50:36 haproxy-1.test.com Keepalived_vrrp[11327]: Sending gratuitous ARP on ens33 for 10.0.0.200 Oct 28 16:50:36 haproxy-1.test.com Keepalived_vrrp[11327]: Sending gratuitous ARP on ens33 for 10.0.0.200 Oct 28 16:50:36 haproxy-1.test.com Keepalived_vrrp[11327]: VRRP_Instance(VI_2) Received advert with high...102 Oct 28 16:50:36 haproxy-1.test.com Keepalived_vrrp[11327]: VRRP_Instance(VI_2) Entering BACKUP STATE Oct 28 16:50:36 haproxy-1.test.com Keepalived_vrrp[11327]: VRRP_Instance(VI_2) removing protocol VIPs. Oct 28 18:28:11 haproxy-1 Keepalived[11325]: Stopping Oct 28 18:28:11 haproxy-1 systemd[1]: Stopping LVS and VRRP High Availability Monitor... Oct 28 18:28:11 haproxy-1 Keepalived_vrrp[11327]: VRRP_Instance(VI_1) sent 0 priority Oct 28 18:28:11 haproxy-1 Keepalived_vrrp[11327]: VRRP_Instance(VI_1) removing protocol VIPs. Oct 28 18:28:12 haproxy-1 systemd[1]: Stopped LVS and VRRP High Availability Monitor. Hint: Some lines were ellipsized, use -l to show in full. [root@haproxy-1 ~]# ip addr 1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN qlen 1 link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00 inet 127.0.0.1/8 scope host lo valid_lft forever preferred_lft forever inet6 ::1/128 scope host valid_lft forever preferred_lft forever 2: ens33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen 1000 link/ether 00:0c:29:1d:7a:63 brd ff:ff:ff:ff:ff:ff inet 10.0.0.11/24 brd 10.0.0.255 scope global ens33 valid_lft forever preferred_lft forever inet6 fe80::8ec5:50ac:d71:20d7/64 scope link valid_lft forever preferred_lft forever inet6 fe80::f87c:449f:eb4a:ba03/64 scope link tentative dadfailed valid_lft forever preferred_lft forever
##在haproxy-2上查看keepalive和vip的狀態,可以看到vip1已經從haproxy-1飄到haproxy-2上了
[root@haproxy-2 ~]# systemctl status keepalived ● keepalived.service - LVS and VRRP High Availability Monitor Loaded: loaded (/usr/lib/systemd/system/keepalived.service; disabled; vendor preset: disabled) Active: active (running) since Sat 2017-10-28 16:50:35 CST; 1h 41min ago Process: 34787 ExecStart=/usr/sbin/keepalived $KEEPALIVED_OPTIONS (code=exited, status=0/SUCCESS) Main PID: 34788 (keepalived) CGroup: /system.slice/keepalived.service ├─34788 /usr/sbin/keepalived -D ├─34789 /usr/sbin/keepalived -D └─34790 /usr/sbin/keepalived -D Oct 28 18:28:12 haproxy-2 Keepalived_vrrp[34790]: Sending gratuitous ARP on ens33 for 10.0.0.100 Oct 28 18:28:12 haproxy-2 Keepalived_vrrp[34790]: Sending gratuitous ARP on ens33 for 10.0.0.100 Oct 28 18:28:12 haproxy-2 Keepalived_vrrp[34790]: Sending gratuitous ARP on ens33 for 10.0.0.100 Oct 28 18:28:12 haproxy-2 Keepalived_vrrp[34790]: Sending gratuitous ARP on ens33 for 10.0.0.100 Oct 28 18:28:17 haproxy-2 Keepalived_vrrp[34790]: Sending gratuitous ARP on ens33 for 10.0.0.100 Oct 28 18:28:17 haproxy-2 Keepalived_vrrp[34790]: VRRP_Instance(VI_1) Sending/queueing gratuitous ARPs o...100 Oct 28 18:28:17 haproxy-2 Keepalived_vrrp[34790]: Sending gratuitous ARP on ens33 for 10.0.0.100 Oct 28 18:28:17 haproxy-2 Keepalived_vrrp[34790]: Sending gratuitous ARP on ens33 for 10.0.0.100 Oct 28 18:28:17 haproxy-2 Keepalived_vrrp[34790]: Sending gratuitous ARP on ens33 for 10.0.0.100 Oct 28 18:28:17 haproxy-2 Keepalived_vrrp[34790]: Sending gratuitous ARP on ens33 for 10.0.0.100 Hint: Some lines were ellipsized, use -l to show in full. [root@haproxy-2 ~]# ip addr 1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN qlen 1 link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00 inet 127.0.0.1/8 scope host lo valid_lft forever preferred_lft forever inet6 ::1/128 scope host valid_lft forever preferred_lft forever 2: ens33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen 1000 link/ether 00:0c:29:76:bf:48 brd ff:ff:ff:ff:ff:ff inet 10.0.0.12/24 brd 10.0.0.255 scope global ens33 valid_lft forever preferred_lft forever inet 10.0.0.200/32 scope global ens33 valid_lft forever preferred_lft forever inet 10.0.0.100/32 scope global ens33 valid_lft forever preferred_lft forever inet6 fe80::f87c:449f:eb4a:ba03/64 scope link valid_lft forever preferred_lft forever
##訪問web服務
[root@client ~]# curl img.test.com 10.0.0.13 img.test.com [root@client ~]# curl img.test.com 10.0.0.13 img.test.com [root@client ~]# curl www.test.com 10.0.0.14 www.test.com [root@client ~]# curl www.test.com 10.0.0.14 www.test.com [root@client ~]# curl web.test.com 10.0.0.15:80 web.test.com [root@client ~]# curl web.test.com 10.0.0.15:8080 [root@client ~]# curl web.test.com 10.0.0.15:80 web.test.com [root@client ~]# curl web.test.com 10.0.0.15:8080
##訪問監控頁面
這次的優化haproxy的實驗就已經到此結束了。如果有寫錯的地方,歡迎各位大神指出來,我會去改正的。如果有寫的不好的地方,請多多見諒!!!