之前的博文我介紹瞭如何搭建CHEF環境以及創建編寫cookbook,resipes用來批量將cookbook下發到客戶端執行相應的部署操作.
NOW,本篇文檔我們會詳細介紹如何利用CHEF獨有的框架語言來批量部署安裝APACHE,並加載其HTTPS模塊等功能.
相信如果你看了本篇文檔,利用CHEF實現一個批量自動化部署將不是什麼難事.
CHEF環境部署詳見: http://showerlee.blog.51cto.com/2047005/1408467
操作系統:CentOS-6.3-x86-64
CHEF: chef-server-11.0.12-1.el6.x86_64
Server : 10.107.91.251 (chef.example.com)
Workstation: 10.107.91.251 (chef.example.com)
node: 10.107.91.252 (node1.example.com)
一. 創建一個空的cookbook實例,並命名爲apache (chef.example.com)
# su -
# cd ~/chef-repo/cookbooks/
# knife cookbook create apache
# ls
------------------------------------------------------------------------------------------------
README.md apache quick_start
------------------------------------------------------------------------------------------------
# cd apache
# ls
------------------------------------------------------------------------------------------------
CHANGELOG.md attributes files metadata.rb recipes templates
README.md definitions libraries providers resources
------------------------------------------------------------------------------------------------
二. 創建SSL祕鑰證書並複製到apache的cookbook對應文件夾 (chef.example.com)
1.證書配置:
1).下載並解壓ssl證書生成壓縮包:
# cd ~/chef-repo/cookbooks/apache/files/default
# mkdir certificates
# cd certificates
# wget http://www.openssl.org/contrib/ssl.ca-0.1.tar.gz
# tar zxvf ssl.ca-0.1.tar.gz
# cd ssl.ca-0.1
2).利用ssl內腳本生成根證書:
# ./new-root-ca.sh
----------------------------------------------------------------------------------------------
No Root CA key round. Generating one
Generating RSA private key, 1024 bit long modulus
………………………++++++
….++++++
e is 65537 (0×10001)
Enter pass phrase for ca.key: (輸入一個密碼)
Verifying – Enter pass phrase for ca.key: (再輸入一次密碼)
……
Self-sign the root CA… (簽署根證書)
Enter pass phrase for ca.key: (輸入剛剛設置的密碼)
……..
…….. (下面開始簽署)
Country Name (2 letter code) [MY]:CN
State or Province Name (full name) [Perak]:JiangSu
Locality Name (eg, city) [Sitiawan]:NanJing
Organization Name (eg, company) [My Directory Sdn Bhd]:example Co.,Ltd
Organizational Unit Name (eg, section) [Certification Services Division]:example
Common Name (eg, MD Root CA) []:example
Email Address []:[email protected]
---------------------------------------------------------------------------------------------
這樣就生成了ca.key和ca.crt兩個文件
3).生成服務端證書:
# ./new-server-cert.sh server
注:證書名爲server
-----------------------------------------------------------------------------------------------
……
……
Country Name (2 letter code) [MY]:CN
State or Province Name (full name) [Perak]:JiangSu
Locality Name (eg, city) [Sitiawan]:NanJing
Organization Name (eg, company) [My Directory Sdn Bhd]:example Co.,Ltd
Organizational Unit Name (eg, section) [Secure Web Server]:example
Common Name (eg, www.domain.com) []:www.example.com
Email Address []:[email protected]
------------------------------------------------------------------------------------------------
這樣就生成了server.csr和server.key這兩個文件。
4).簽署服務端證書:
# ./sign-server-cert.sh server
--------------------------------------------------------------------------------------------
CA signing: server.csr -> server.crt:
Using configuration from ca.config
Enter pass phrase for ./ca.key: (輸入上面設置的根證書密碼)
Check that the request matches the signature
Signature ok
The Subject’s Distinguished Name is as follows
countryName RINTABLE:’CN’
stateOrProvinceName RINTABLE:’JiangSu’
localityName RINTABLE:’NanJing’
organizationName RINTABLE:’example Co.,Ltd’
organizationalUnitName:PRINTABLE:’example’
commonName RINTABLE:’www.example.com’
emailAddress :IA5STRING:’[email protected]’
Certificate is to be certified until Jul 16 12:55:34 2005 GMT (365 days)
Sign the certificate? [y/n]:y
1 out of 1 certificate requests certified, commit? [y/n]y
Write out database with 1 new entries
Data Base Updated
CA verifying: server.crt <-> CA cert
server.crt: OK
--------------------------------------------------------------------------------------
2.複製證書到cookbook相應位置
# pwd
--------------------------------------------------------------------------------------
/root/chef-repo/cookbooks/apache/files/default/certificates/ssl.ca-0.1
--------------------------------------------------------------------------------------
# cp server.crt server.key ca.crt ..
# cd ..
# ls
--------------------------------------------------------------------------------------
ca.crt server.crt server.key ssl.ca-0.1 ssl.ca-0.1.tar.gz
--------------------------------------------------------------------------------------
三. 定義cookbook變量屬性 (chef.example.com)
# cd ~/chef-repo/cookbooks/apache/attributes
# vi default.rb
--------------------------------------------------------------------------------------
default['apache']['dir'] = "/etc/httpd"
default['apache']['sslpath'] = "/etc/httpd/ssl"
default['apache']['servername'] = "node1.example.com"
--------------------------------------------------------------------------------------
四.編寫recipes(可按照實際部署需求修改) (chef.example.com)
# cd ~/chef-repo/cookbooks/apache/recipes
# vi default.rb
--------------------------------------------------------------------------------------
# Cookbook Name:: apache
# Recipe:: default
#
# Copyright 2013, YOUR_COMPANY_NAME
#
# All rights reserved - Do Not Redistribute
#
# Install httpd package but don't start it
package "httpd" do
action [:install]
end
# Install mod_ssl package to enable ssl module in apache
package "mod_ssl" do
action [:install]
end
# Stop iptables service permanently
service "iptables" do
action [:disable,:stop]
end
# Stop ip6tables service permanently
service "ip6tables" do
action [:disable,:stop]
end
# Create /etc/httpd/ssl directory on chef client
directory "#{node['apache']['dir']}/ssl" do
action :create
recursive true
mode 0755
end
# Copy ssl certificates from certificates folder to client's /etc/httpd/ssl folder
remote_directory "#{node['apache']['dir']}/ssl" do
source "certificates"
files_owner "root"
files_group "root"
files_mode 00644
owner "root"
group "root"
mode 0755
end
# This will make changes to ssl.conf
template "/etc/httpd/conf.d/ssl.conf" do
source "ssl.conf.erb"
mode 0644
owner "root"
group "root"
variables(
:sslcertificate => "#{node['apache']['sslpath']}/server.crt",
:sslkey => "#{node['apache']['sslpath']}/server.key",
:sslcacertificate => "#{node['apache']['sslpath']}/ca.crt",
:servername => "#{node['apache']['servername']}"
)
end
# start httpd service
service "httpd" do
action [:enable,:start]
end
--------------------------------------------------------------------------------------
五.定義templates (chef.example.com)
注:這裏實際上就是將apache原有的配置文件中需要修改的參數添加chef自有的變量屬性,部署到client端,實現apache的自定義配置.
此處僅僅更改了SSL證書的具體路徑,如果有其他需要可按此語法格式進行修改.
# cd ~/chef-repo/cookbooks/apache/templates/default
# vi ssl.conf.erb
--------------------------------------------------------------------------------------
#
# This is the Apache server configuration file providing SSL support.
# It contains the configuration directives to instruct the server how to
# serve pages over an https connection. For detailing information about these
# directives see <URL:http://httpd.apache.org/docs/2.2/mod/mod_ssl.html>
#
# Do NOT simply read the instructions in here without understanding
# what they do. They're here only as hints or reminders. If you are unsure
# consult the online docs. You have been warned.
#
LoadModule ssl_module modules/mod_ssl.so
#
# When we also provide SSL we have to listen to the
# the HTTPS port in addition.
#
Listen 443
##
## SSL Global Context
##
## All SSL configuration in this context applies both to
## the main server and all SSL-enabled virtual hosts.
##
# Pass Phrase Dialog:
# Configure the pass phrase gathering process.
# The filtering dialog program (`builtin' is a internal
# terminal dialog) has to provide the pass phrase on stdout.
SSLPassPhraseDialog builtin
# Inter-Process Session Cache:
# Configure the SSL Session Cache: First the mechanism
# to use and second the expiring timeout (in seconds).
SSLSessionCache shmcb:/var/cache/mod_ssl/scache(512000)
SSLSessionCacheTimeout 300
# Semaphore:
# Configure the path to the mutual exclusion semaphore the
# SSL engine uses internally for inter-process synchronization.
SSLMutex default
# Pseudo Random Number Generator (PRNG):
# Configure one or more sources to seed the PRNG of the
# SSL library. The seed data should be of good random quality.
# WARNING! On some platforms /dev/random blocks if not enough entropy
# is available. This means you then cannot use the /dev/random device
# because it would lead to very long connection times (as long as
# it requires to make more entropy available). But usually those
# platforms additionally provide a /dev/urandom device which doesn't
# block. So, if available, use this one instead. Read the mod_ssl User
# Manual for more details.
SSLRandomSeed startup file:/dev/urandom 256
SSLRandomSeed connect builtin
#SSLRandomSeed startup file:/dev/random 512
#SSLRandomSeed connect file:/dev/random 512
#SSLRandomSeed connect file:/dev/urandom 512
#
# Use "SSLCryptoDevice" to enable any supported hardware
# accelerators. Use "openssl engine -v" to list supported
# engine names. NOTE: If you enable an accelerator and the
# server does not start, consult the error logs and ensure
# your accelerator is functioning properly.
#
SSLCryptoDevice builtin
#SSLCryptoDevice ubsec
##
## SSL Virtual Host Context
##
<VirtualHost _default_:443>
# General setup for the virtual host, inherited from global configuration
#DocumentRoot "/var/www/html"
ServerName <%= @servername %>:443
# Use separate log files for the SSL virtual host; note that LogLevel
# is not inherited from httpd.conf.
ErrorLog logs/ssl_error_log
TransferLog logs/ssl_access_log
LogLevel warn
# SSL Engine Switch:
# Enable/Disable SSL for this virtual host.
SSLEngine on
# SSL Protocol support:
# List the enable protocol levels with which clients will be able to
# connect. Disable SSLv2 access by default:
SSLProtocol all -SSLv2
# SSL Cipher Suite:
# List the ciphers that the client is permitted to negotiate.
# See the mod_ssl documentation for a complete list.
SSLCipherSuite ALL:!ADH:!EXPORT:!SSLv2:RC4+RSA:+HIGH:+MEDIUM:+LOW
# Server Certificate:
# Point SSLCertificateFile at a PEM encoded certificate. If
# the certificate is encrypted, then you will be prompted for a
# pass phrase. Note that a kill -HUP will prompt again. A new
# certificate can be generated using the genkey(1) command.
SSLCertificateFile <%= @sslcertificate %>
# Server Private Key:
# If the key is not combined with the certificate, use this
# directive to point at the key file. Keep in mind that if
# you've both a RSA and a DSA private key you can configure
# both in parallel (to also allow the use of DSA ciphers, etc.)
SSLCertificateKeyFile <%= @sslkey %>
# Server Certificate Chain:
# Point SSLCertificateChainFile at a file containing the
# concatenation of PEM encoded CA certificates which form the
# certificate chain for the server certificate. Alternatively
# the referenced file can be the same as SSLCertificateFile
# when the CA certificates are directly appended to the server
# certificate for convinience.
#SSLCertificateChainFile /etc/pki/tls/certs/server-chain.crt
# Certificate Authority (CA):
# Set the CA certificate verification path where to find CA
# certificates for client authentication or alternatively one
# huge file containing all of them (file must be PEM encoded)
SSLCACertificateFile <%= @sslcacertificate %>
# Client Authentication (Type):
# Client certificate verification type and depth. Types are
# none, optional, require and optional_no_ca. Depth is a
# number which specifies how deeply to verify the certificate
# issuer chain before deciding the certificate is not valid.
#SSLVerifyClient require
#SSLVerifyDepth 10
# Access Control:
# With SSLRequire you can do per-directory access control based
# on arbitrary complex boolean expressions containing server
# variable checks and other lookup directives. The syntax is a
# mixture between C and Perl. See the mod_ssl documentation
# for more details.
#<Location />
#SSLRequire ( %{SSL_CIPHER} !~ m/^(EXP|NULL)/ \
# and %{SSL_CLIENT_S_DN_O} eq "Snake Oil, Ltd." \
# and %{SSL_CLIENT_S_DN_OU} in {"Staff", "CA", "Dev"} \
# and %{TIME_WDAY} >= 1 and %{TIME_WDAY} <= 5 \
# and %{TIME_HOUR} >= 8 and %{TIME_HOUR} <= 20 ) \
# or %{REMOTE_ADDR} =~ m/^192\.76\.162\.[0-9]+$/
#</Location>
# SSL Engine Options:
# Set various options for the SSL engine.
# o FakeBasicAuth:
# Translate the client X.509 into a Basic Authorisation. This means that
# the standard Auth/DBMAuth methods can be used for access control. The
# user name is the `one line' version of the client's X.509 certificate.
# Note that no password is obtained from the user. Every entry in the user
# file needs this password: `xxj31ZMTZzkVA'.
# o ExportCertData:
# This exports two additional environment variables: SSL_CLIENT_CERT and
# SSL_SERVER_CERT. These contain the PEM-encoded certificates of the
# server (always existing) and the client (only existing when client
# authentication is used). This can be used to import the certificates
# into CGI scripts.
# o StdEnvVars:
# This exports the standard SSL/TLS related `SSL_*' environment variables.
# Per default this exportation is switched off for performance reasons,
# because the extraction step is an expensive operation and is usually
# useless for serving static content. So one usually enables the
# exportation for CGI and SSI requests only.
# o StrictRequire:
# This denies access when "SSLRequireSSL" or "SSLRequire" applied even
# under a "Satisfy any" situation, i.e. when it applies access is denied
# and no other module can change it.
# o OptRenegotiate:
# This enables optimized SSL connection renegotiation handling when SSL
# directives are used in per-directory context.
#SSLOptions +FakeBasicAuth +ExportCertData +StrictRequire
<Files ~ "\.(cgi|shtml|phtml|php3?)$">
SSLOptions +StdEnvVars
</Files>
<Directory "/var/www/cgi-bin">
SSLOptions +StdEnvVars
</Directory>
# SSL Protocol Adjustments:
# The safe and default but still SSL/TLS standard compliant shutdown
# approach is that mod_ssl sends the close notify alert but doesn't wait for
# the close notify alert from client. When you need a different shutdown
# approach you can use one of the following variables:
# o ssl-unclean-shutdown:
# This forces an unclean shutdown when the connection is closed, i.e. no
# SSL close notify alert is send or allowed to received. This violates
# the SSL/TLS standard but is needed for some brain-dead browsers. Use
# this when you receive I/O errors because of the standard approach where
# mod_ssl sends the close notify alert.
# o ssl-accurate-shutdown:
# This forces an accurate shutdown when the connection is closed, i.e. a
# SSL close notify alert is send and mod_ssl waits for the close notify
# alert of the client. This is 100% SSL/TLS standard compliant, but in
# practice often causes hanging connections with brain-dead browsers. Use
# this only for browsers where you know that their SSL implementation
# works correctly.
# Notice: Most problems of broken clients are also related to the HTTP
# keep-alive facility, so you usually additionally want to disable
# keep-alive for those clients, too. Use variable "nokeepalive" for this.
# Similarly, one has to force some clients to use HTTP/1.0 to workaround
# their broken HTTP/1.1 implementation. Use variables "downgrade-1.0" and
# "force-response-1.0" for this.
SetEnvIf User-Agent ".*MSIE.*" \
nokeepalive ssl-unclean-shutdown \
downgrade-1.0 force-response-1.0
# Per-Server Logging:
# The home of a custom SSL log file. Use this when you want a
# compact non-error SSL logfile on a virtual host basis.
CustomLog logs/ssl_request_log \
"%t %h %{SSL_PROTOCOL}x %{SSL_CIPHER}x \"%r\" %b"
</VirtualHost>
--------------------------------------------------------------------------------------
六.上傳cookbook (chef.example.com)
# cd /root/chef-repo/cookbooks
# knife cookbook upload apache
--------------------------------------------------------------------------------------
Uploading apache [0.1.0]
Uploaded 1 cookbook.
--------------------------------------------------------------------------------------
七.創建Role (chef.example.com)
注:簡單來說Role就是實現一個能在Server端批量下發cookbook並自動開始對所有client的部署,此前的方法部署client端需要登錄其SHELL執行chef-client,方能開始部署,少量部署無所謂,但批量的話執行效率會大大降低.
1). 設置editor環境變量
# echo 'export EDITOR=$(which vi)' >> ~/.bashrc
# source ~/.bashrc
2). 編寫Role,將默認替換成如下內容.
# knife role create webserver
--------------------------------------------------------------------------------------
{
"run_list": [
"recipe[apache]"
],
"chef_type": "role",
"env_run_lists": {
},
"description": "apache webserver",
"override_attributes": {
},
"json_class": "Chef::Role",
"default_attributes": {
},
"name": "webserver"
}
--------------------------------------------------------------------------------------
八. Bootstrap客戶端.
注: bootstrap是一個將CHEF具體的cookbook實例部署到目標客戶端的程序,因此他可以在server端實現client本地執行最後部署命令chef-client的功能
1. 首先需要做一個CHEF的server端到client端的SSH祕鑰認證,實現server端無需輸入SSH密碼即可登錄client執行部署.
1) .在CHEF的Server端(SSH客戶端)創建祕鑰對:(chef.example.com)
# su - root
# ssh-keygen -t dsa
一路回車即可
----------------------
Generating public/private dsa key pair.
Enter file in which to save the key (/root/.ssh/id_dsa):
Created directory '/root/.ssh'.
Enter passphrase (empty for no passphrase):
Enter same passphrase again:
Your identification has been saved in /root/.ssh/id_dsa.
Your public key has been saved in /root/.ssh/id_dsa.pub.
The key fingerprint is:
e9:5e:4a:7f:79:64:c5:ae:f2:06:a7:26:e4:41:5c:0e [email protected]
The key's randomart image is:
+--[ DSA 1024]----+
| |
| E . |
| . + . |
| .o . o|
| S. o |
| . o . + .|
| oo.. B . |
| o +o * + |
| o .+ =. |
+-----------------+
----------------------
2). 查看生成的祕鑰對:(chef.example.com)
# ls -lda ~/.ssh
-----------------
drwx------ 2 root root 4096 6月 6 23:03 .ssh
-----------------
# cd .ssh
# ls -la
------------------
總用量 16
drwx------ 2 root root 4096 6月 6 23:03 .
dr-xr-x---. 26 root root 4096 6月 6 23:03 ..
-rw------- 1 root root 668 6月 6 23:03 id_dsa
-rw-r--r-- 1 root root 613 6月 6 23:03 id_dsa.pub
------------------
祕鑰生成完畢
3) .將公鑰(鎖)分發到SSH服務端(CHEF客戶端):(chef.example.com)
# ssh-copy-id -i .ssh/id_dsa.pub node1.example.com
注:若非root用戶,以及自定義SSH端口,則格式爲:
# ssh-copy-id -i .ssh/id_rsa.pub "-p 22 user@server"
輸入yes,然後密碼後回車:
----------------------------
The authenticity of host 'node1.example.com (10.107.91.252)' can't be established.
RSA key fingerprint is fc:9b:2e:38:3b:04:18:67:16:8f:dd:94:a8:bd:08:03.
Are you sure you want to continue connecting (yes/no)? yes
Warning: Permanently added 'node1.example.com' (RSA) to the list of known hosts.
Address node1.example.com maps to bogon, but this does not map back to the address - POSSIBLE BREAK-IN ATTEMPT!
[email protected]'s password: 輸入密碼
Now try logging into the machine, with "ssh 'node1.example.com'", and check in:
.ssh/authorized_keys
to make sure we haven't added extra keys that you weren't expecting.
-----------------------------
公鑰分發完畢
4) .SSH服務端(CHEF客戶端)查看收到的分發文件:(node1.example.com)
# ll /root/.ssh
-------------
總用量 4
-rw------- 1 root root 613 6月 6 23:29 authorized_keys
-------------
成功收到
2.執行bootstrap部署 (chef.example.com)
# knife bootstrap node1.example.com -x root --sudo -r "role[webserver]"
--------------------------------------------------------------------------------------------------------------
Connecting to node1.example.com
node1.example.com Starting first Chef Client run...
node1.example.com [2014-05-09T06:08:53+08:00] WARN:
node1.example.com * * * * * * * * * * * * * * * * * * * * * * * * * * * * * * * * * * * * * * * *
node1.example.com SSL validation of HTTPS requests is disabled. HTTPS connections are still
node1.example.com encrypted, but chef is not able to detect forged replies or man in the middle
node1.example.com attacks.
node1.example.com
node1.example.com To fix this issue add an entry like this to your configuration file:
node1.example.com
node1.example.com ```
node1.example.com # Verify all HTTPS connections (recommended)
node1.example.com ssl_verify_mode :verify_peer
node1.example.com
node1.example.com # OR, Verify only connections to chef-server
node1.example.com verify_api_cert true
node1.example.com ```
node1.example.com
node1.example.com To check your SSL configuration, or troubleshoot errors, you can use the
node1.example.com `knife ssl check` command like so:
node1.example.com
node1.example.com ```
node1.example.com knife ssl check -c /etc/chef/client.rb
node1.example.com ```
node1.example.com
node1.example.com * * * * * * * * * * * * * * * * * * * * * * * * * * * * * * * * * * * * * * * *
node1.example.com
node1.example.com Starting Chef Client, version 11.12.4
node1.example.com resolving cookbooks for run list: ["apache"]
node1.example.com Synchronizing Cookbooks:
node1.example.com - apache
node1.example.com Compiling Cookbooks...
node1.example.com Converging 8 resources
node1.example.com Recipe: apache::default
node1.example.com * package[httpd] action install (up to date)
node1.example.com * package[mod_ssl] action install (up to date)
node1.example.com * service[iptables] action disable (up to date)
node1.example.com * service[iptables] action stop (up to date)
node1.example.com * service[ip6tables] action disable (up to date)
node1.example.com * service[ip6tables] action stop (up to date)
node1.example.com * directory[/etc/httpd/ssl] action create (up to date)
node1.example.com * remote_directory[/etc/httpd/ssl] action createRecipe: <Dynamically Defined Resource>
node1.example.com * cookbook_file[/etc/httpd/ssl/ssl.ca-0.1/sign-user-cert.sh] action create (up to date)
node1.example.com * cookbook_file[/etc/httpd/ssl/ssl.ca-0.1/sign-server-cert.sh] action create (up to date)
node1.example.com * cookbook_file[/etc/httpd/ssl/ssl.ca-0.1/server.key] action create (up to date)
node1.example.com * cookbook_file[/etc/httpd/ssl/ssl.ca-0.1/server.csr] action create (up to date)
node1.example.com * cookbook_file[/etc/httpd/ssl/ssl.ca-0.1/server.crt] action create (up to date)
node1.example.com * cookbook_file[/etc/httpd/ssl/ssl.ca-0.1/random-bits] action create (up to date)
node1.example.com * cookbook_file[/etc/httpd/ssl/ssl.ca-0.1/p12.sh] action create (up to date)
node1.example.com * cookbook_file[/etc/httpd/ssl/ssl.ca-0.1/new-user-cert.sh] action create (up to date)
node1.example.com * cookbook_file[/etc/httpd/ssl/ssl.ca-0.1/new-server-cert.sh] action create (up to date)
node1.example.com * cookbook_file[/etc/httpd/ssl/ssl.ca-0.1/new-root-ca.sh] action create (up to date)
node1.example.com * cookbook_file[/etc/httpd/ssl/ssl.ca-0.1/ca.key] action create (up to date)
node1.example.com * cookbook_file[/etc/httpd/ssl/ssl.ca-0.1/ca.db.serial] action create (up to date)
node1.example.com * cookbook_file[/etc/httpd/ssl/ssl.ca-0.1/ca.db.index.attr] action create (up to date)
node1.example.com * cookbook_file[/etc/httpd/ssl/ssl.ca-0.1/ca.db.index] action create (up to date)
node1.example.com * cookbook_file[/etc/httpd/ssl/ssl.ca-0.1/ca.db.certs/01.pem] action create (up to date)
node1.example.com * cookbook_file[/etc/httpd/ssl/ssl.ca-0.1/ca.crt] action create (up to date)
node1.example.com * cookbook_file[/etc/httpd/ssl/ssl.ca-0.1/VERSION] action create (up to date)
node1.example.com * cookbook_file[/etc/httpd/ssl/ssl.ca-0.1/README] action create (up to date)
node1.example.com * cookbook_file[/etc/httpd/ssl/ssl.ca-0.1/COPYING] action create (up to date)
node1.example.com * cookbook_file[/etc/httpd/ssl/ssl.ca-0.1.tar.gz] action create (up to date)
node1.example.com * cookbook_file[/etc/httpd/ssl/server.key] action create (up to date)
node1.example.com * cookbook_file[/etc/httpd/ssl/server.crt] action create (up to date)
node1.example.com * cookbook_file[/etc/httpd/ssl/ca.crt] action create (up to date)
node1.example.com (up to date)
node1.example.com Recipe: apache::default
node1.example.com * template[/etc/httpd/conf.d/ssl.conf] action create (up to date)
node1.example.com * service[httpd] action enable (up to date)
node1.example.com * service[httpd] action start (up to date)
node1.example.com
node1.example.com Running handlers:
node1.example.com Running handlers complete
node1.example.com
node1.example.com Chef Client finished, 0/34 resources updated in 9.1690343 seconds
--------------------------------------------------------------------------------------------------------------
部署成功....
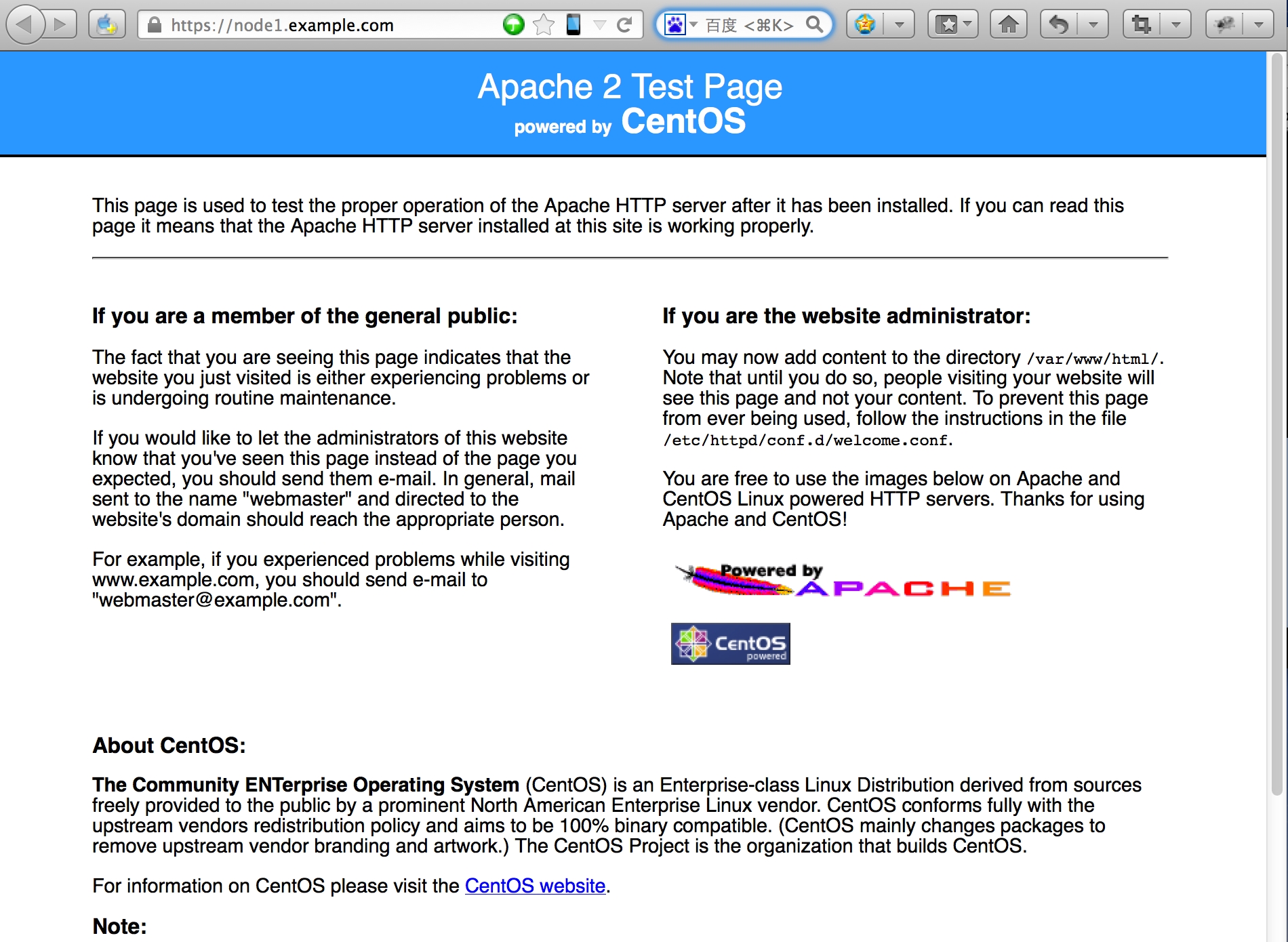
九.驗證 (node1.example.com)
# cd /etc/httpd/
# ls
--------------------------------------------------------------------------------------------------------------
conf conf.d logs modules run ssl
--------------------------------------------------------------------------------------------------------------
# service httpd status
--------------------------------------------------------------------------------------------------------------
httpd (pid 10492) is running...
--------------------------------------------------------------------------------------------------------------
# lsof -i:80
--------------------------------------------------------------------------------------------------------------
COMMAND PID USER FD TYPE DEVICE SIZE/OFF NODE NAME
httpd 10492 root 4u IPv6 48097 0t0 TCP *:http (LISTEN)
httpd 10494 apache 4u IPv6 48097 0t0 TCP *:http (LISTEN)
httpd 10495 apache 4u IPv6 48097 0t0 TCP *:http (LISTEN)
httpd 10496 apache 4u IPv6 48097 0t0 TCP *:http (LISTEN)
httpd 10497 apache 4u IPv6 48097 0t0 TCP *:http (LISTEN)
httpd 10498 apache 4u IPv6 48097 0t0 TCP *:http (LISTEN)
httpd 10499 apache 4u IPv6 48097 0t0 TCP *:http (LISTEN)
httpd 10500 apache 4u IPv6 48097 0t0 TCP *:http (LISTEN)
httpd 10501 apache 4u IPv6 48097 0t0 TCP *:http (LISTEN)
# lsof -i:443
--------------------------------------------------------------------------------------------------------------
COMMAND PID USER FD TYPE DEVICE SIZE/OFF NODE NAME
httpd 10492 root 6u IPv6 48101 0t0 TCP *:https (LISTEN)
httpd 10494 apache 6u IPv6 48101 0t0 TCP *:https (LISTEN)
httpd 10495 apache 6u IPv6 48101 0t0 TCP *:https (LISTEN)
httpd 10496 apache 6u IPv6 48101 0t0 TCP *:https (LISTEN)
httpd 10497 apache 6u IPv6 48101 0t0 TCP *:https (LISTEN)
httpd 10498 apache 6u IPv6 48101 0t0 TCP *:https (LISTEN)
httpd 10499 apache 6u IPv6 48101 0t0 TCP *:https (LISTEN)
httpd 10500 apache 6u IPv6 48101 0t0 TCP *:https (LISTEN)
httpd 10501 apache 6u IPv6 48101 0t0 TCP *:https (LISTEN)
--------------------------------------------------------------------------------------------------------------
大功告成。。。。