Tcpdump command acts as a packet analyzer on Linux/Unix platform. Tcpdump command will work for most of the Linux distributions. Tcpdump provides a facility to store all the captured packets which can later be used for further analysis. tcpdump command also lets us view the saved files. There are numerous open source softwares (like Wireshark) that are used to analyze tcpdump pcap files.
This article explains how the tcpdump command is used along with some examples.
1. Capturing on a particular interface
Whenever tcpdump command is run with no option, it will start capturing all packets observed by all the interfaces. -i option in this command will let you select any particular ethernet interface over which you wish to execute the capturing process.
sudo tcpdump -i eth1
In above command, tcpdump will capture all the packets flowing through the interface eth1.
2. Capturing selected number of packets
By default, when tcpdump is run, it will keep running until you cancel the process manually. The -c option in tcpdump lets us determine the number of packets to be captured.
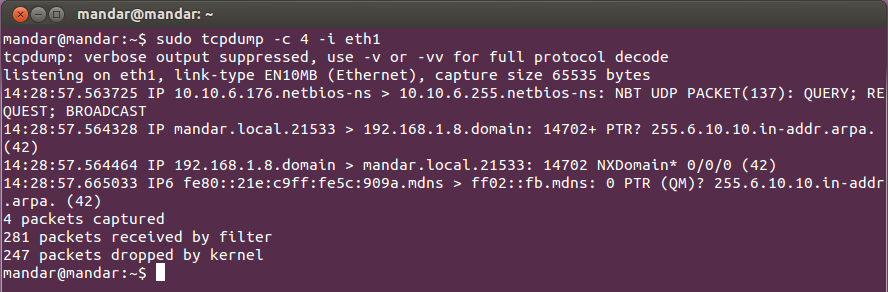
sudo tcpdump -c 4 -i eth1
This tcpdump command captures only 4 packets on ethernet interface eth1.
3. Capturing Packets in ASCII Format
Tcpdump along with -A command will print the packet contents in ASCII.sudo tcpdump -A -i eth1
4. Capturing Packets in HEX and ASCII
If anybody wants to analyze the hex values of the packets, tcpdump command -XX allows you to print both ASCII and HEX formats of the packets.
sudo tcpdump -XX -i eth1
5. Capture and Write
Tcpdump allows you to save the packets to a file, so that you can use the file for further analysis. The -w option in tcpdump will store the packets into a .pcap file in order to be read by any packet analyzer.
sudo tcpdump -w <file_name.pcap> -i <interface>
6. Reading a Saved File
To read the saved pcap file using tcpdump, use option -r as demonstrated below.
sudo tcpdump -tttt -r <file_name.pcap>
The option -tttt will display a timestamp followed by a date before each dumped packet
7. Capturing packets with IP address
Till now, we have seen tcpdump printing the dumped packets along with the DNS addresses only. Option -n in tcpdump will print IP addresses of the hosts involved instead of their DNS addresses.
8. Store Packets with Size more/less than N bytes
In tcpdump there is a provision where you can store only those packets having size greater/less than a threshold value which can be altered by the user.
sudo tcpdump -w grt.pcap greater 1024
sudo tcpdump -w less.pcap less 1024
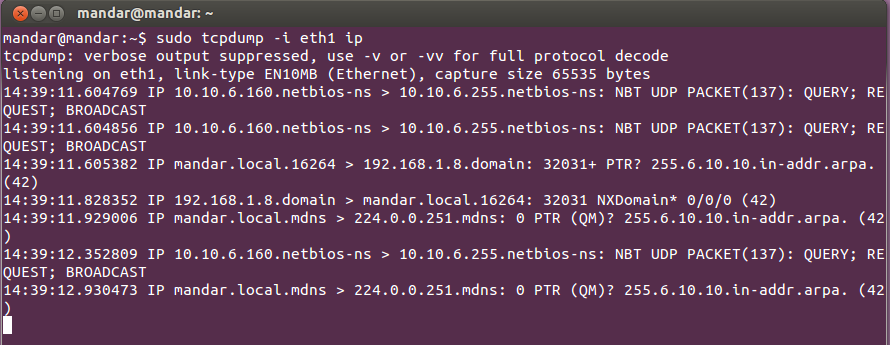
9. Capturing Packets belonging to Specific Protocol
In tcpdump, you can filter the packets on the basis of the protocols used by them. Protocol may be any one among the following- ip, ip6, tcp, udp arp, rarp, fddi, tr, wlan and decnet.
sudo tcpdump -i <interface> <protocol_name>
10. Capturing Packets for Particular Source/Destination IP and Port
We can add a filter in tcpdump on the basis of source/destination IP addresses and the port numbers carried by the packets.
sudo tcpdump -i <interface> src/dst <ip_address> and <port_number>
11. Capturing Packets with "and", "or" & "not"
Tcpdump command includes “and”, “or” and “not” operations in order to filter the packets.
sudo tcpdump -i eth1 not arp and not rarp
That's all about TCPDUMP..!
原文網址:
http://www.yourownlinux.com/2013/07/linux-command-tcpdump.html