源NAT 和 目的 NAT 的區別:
Source Nat 業務場景:內網地址訪問外部地址、資源時使用;源地址是轉換前的內網地址,目標地址是轉換後的公網地址。
方向【源/內網地址 ------轉換爲-------目的/公網地址】;
Destination Nat 業務場景:從公網訪問內部特定IP或特定IP的特定端口時使用;源地址是轉換前的公網地址,目的地址是轉換後的內網IP或IP:port.
方向【源/公網地址 ------轉換爲-------目的/內網地址】;
一、定義 目的 NAT
== 創建Dnat pool
set security nat destination pool DP_TRUST_MQI_8088 address 172.22.201.19/32
set security nat destination pool DP_TRUST_MQI_8088 address port 8088
==創建DNAT規則
set security nat destination rule-set DNAT_FROM_ISP6 rule ISP6_TO_LIMS_BY_Owenli match destination-address-name WAN3006_172
set security nat destination rule-set DNAT_FROM_ISP6 rule ISP6_TO_LIMS_BY_Owenli match destination-port 8089
set security nat destination rule-set DNAT_FROM_ISP6 rule ISP6_TO_LIMS_BY_Owenli then destination-nat pool DP_TRUST_MQI_8088
備註:WAN3006_172 是ISP提供的公網IP,或接口地址或做了ARP_proxy
set security address-book global address WAN3006_172 210.X.X.172/32
==創建區域間的控制策略
set security policies from-zone ISP6 to-zone trust policy ISP6_TO_TRUST_IMMQI_BY_KEVIN match source-address any
set security policies from-zone ISP6 to-zone trust policy ISP6_TO_TRUST_IMMQI_BY_KEVIN match destination-address QI_PRIVATE
set security policies from-zone ISP6 to-zone trust policy ISP6_TO_TRUST_IMMQI_BY_KEVIN match application tcp-80
set security policies from-zone ISP6 to-zone trust policy ISP6_TO_TRUST_IMMQI_BY_KEVIN match application tcp-8888
set security policies from-zone ISP6 to-zone trust policy ISP6_TO_TRUST_IMMQI_BY_KEVIN match application tcp-8089
set security policies from-zone ISP6 to-zone trust policy ISP6_TO_TRUST_IMMQI_BY_KEVIN then permit
set security policies from-zone ISP6 to-zone trust policy ISP6_TO_TRUST_IMMQI_BY_KEVIN then log session-init
set security policies from-zone ISP6 to-zone trust policy ISP6_TO_TRUST_IMMQI_BY_KEVIN then log session-close
set security policies from-zone ISP6 to-zone trust policy ISP6_TO_TRUST_IMMQI_BY_KEVIN then count
二、定義源NAT【design NAT TO iplc 】
set security nat source rule-set SNAT_Design_TO_ISP1 from zone Design
set security nat source rule-set SNAT_Design_TO_ISP1 to zone ISP1
==定義Snat pool
set security nat source pool SP_ISP1_241 address 119.X.X.241/32
==定義Snat 規則
set security nat source rule-set SNAT_Design_TO_ISP1 rule Design_TO_ISP1_ANY match source-address design_team
set security nat source rule-set SNAT_Design_TO_ISP1 rule Design_TO_ISP1_ANY match destination-address 0.0.0.0/0
set security nat source rule-set SNAT_Design_TO_ISP1 rule Design_TO_ISP1_ANY then source-nat pool SP_ISP1_241
set security nat source rule-set SNAT_Design_TO_ISP1 rule Design_TO_ISP1_ANY match source-address cnspdc4
set security nat source rule-set SNAT_Design_TO_ISP1 rule Design_TO_ISP1_ANY match destination-address 0.0.0.0/0
set security nat source rule-set SNAT_Design_TO_ISP1 rule Design_TO_ISP1_ANY then source-nat pool SP_ISP1_241
===定義不同區間的控制策略
set security policies from-zone Design to-zone ISP1 policy LEGACY_YF_DE_TO_ISP1 match source-address cnspdc4
set security policies from-zone Design to-zone ISP1 policy LEGACY_YF_DE_TO_ISP1 match destination-address any
set security policies from-zone Design to-zone ISP1 policy LEGACY_YF_DE_TO_ISP1 match application any
set security policies from-zone Design to-zone ISP1 policy LEGACY_YF_DE_TO_ISP1 then permit
set security policies from-zone Design to-zone ISP1 policy LEGACY_YF_DE_TO_ISP1 then log session-init
set security policies from-zone Design to-zone ISP1 policy LEGACY_YF_DE_TO_ISP1 then log session-close
set security policies from-zone Design to-zone ISP1 policy LEGACY_YF_DE_TO_ISP1 then count
===如果你有N條策略,那麼你可能需要調整你新增策略的順序即優先級,具體視策略內容調整順序;
===修改策略LIMS-XQ-TEST-OWEN-EDIT的順序在策略DENY之前
insert security policies from-zone ISP6 to-zone trust policy LIMS-PY-OWEN-EDIT before policy DENY
三、驗證策略是否生效
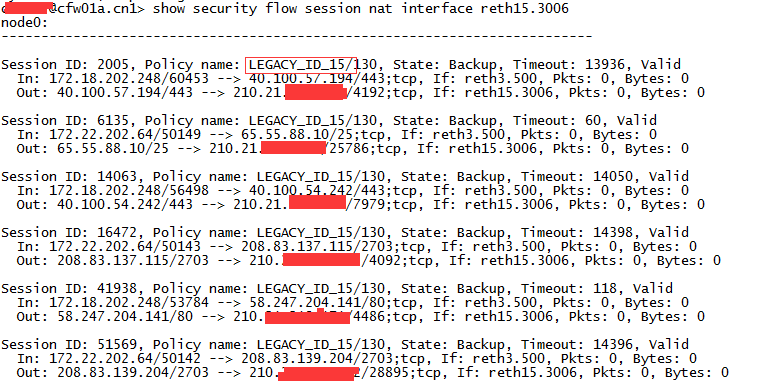
show security flow session nat interface reth15.3006
註釋:reth15.3006 屬於ISP6.因此,查看reth15.3006的會話,從中查找是否出現定義的“區域間訪問控制策略”。有,策略成功,沒有,策略錯誤或策略優先順序錯誤;
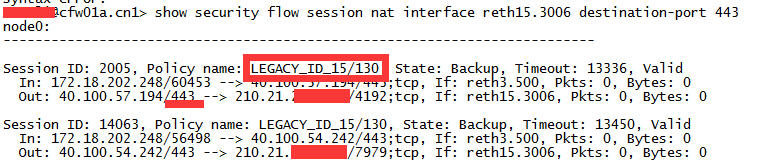
show security flow session nat interface reth15.3006 destination-port 443
註釋:也可以用destination-port、source-port、source-prefix 、destination-prefix等參數對經過ISP6區域的數據流進行更精細的匹配,從結果中判斷策略是否成功應用,加端口查詢的方式尤其適用“內網服務器的業務,通過某個端口發佈到外網,然後驗證”