首先解釋一下什麼是對稱路由和不對稱路由。
對稱路由:symmetric route,指從A到B所走的路由和從B到A所走的路由是相同的
不對稱路由:asymmetric route,指從A到B所走的路由和從B到A所走的路由是不同的
測試過程如下
說明:
1 以下這三種情況中,iptables和selinux都已關閉
2 所有測試均基於RHEL6.8
*********************************
【情況1】這是測試中遇到的問題。這個問題不是非對稱路由問題,而是普通的路由問題
*********************************
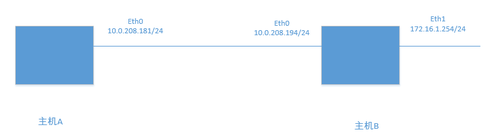
我這裏只是單純的ping不通。在主機B上執行ping -I 172.16.1.254 10.0.208.181(ping的-I是指定源地址),在主機B上進行ping的時候,指定了原IP爲eth1接口的地址,目的地址是主機A的eth0 IP
主機A和主機B的默認網關都指向了10.0.208.254
step1:查看兩臺主機上的路由表
主機B上有2個網段:172和10,主機B的路由表如下
[root@storage ~]# route -n
Kernel IP routing table
Destination Gateway Genmask Flags Metric Ref Use Iface
10.0.208.0 0.0.0.0 255.255.255.0 U 0 0 0 eth0
172.16.1.0 0.0.0.0 255.255.255.0 U 0 0 0 eth1
169.254.0.0 0.0.0.0 255.255.0.0 U 1002 0 0 eth0
169.254.0.0 0.0.0.0 255.255.0.0 U 1003 0 0 eth1
0.0.0.0 10.0.208.254 0.0.0.0 UG 0 0 0 eth0
主機A上有3個網段:10.0.0.0/24,10.0.1.0/24和10.0.208.0/24,這裏只是用10.0.208.0/24網絡。主機A的路由表如下
[root@compute ~]# route -n
Kernel IP routing table
Destination Gateway Genmask Flags Metric Ref Use Iface
10.0.208.0 0.0.0.0 255.255.255.0 U 0 0 0 eth0
10.0.0.0 0.0.0.0 255.255.255.0 U 0 0 0 eth1
10.0.1.0 0.0.0.0 255.255.255.0 U 0 0 0 eth2
169.254.0.0 0.0.0.0 255.255.0.0 U 1002 0 0 eth0
169.254.0.0 0.0.0.0 255.255.0.0 U 1003 0 0 eth1
169.254.0.0 0.0.0.0 255.255.0.0 U 1004 0 0 eth2
0.0.0.0 10.0.208.254 0.0.0.0 UG 0 0 0 eth0
默認情況下是ping不通的:
[root@storage ~]# ping -I 172.16.1.254 10.0.208.181
PING 10.0.208.181 (10.0.208.181) from 172.16.1.254 : 56(84) bytes of data.
^C
--- 10.0.208.181 ping statistics ---
2 packets transmitted, 0 received, 100% packet loss, time 1774ms
step2:設置主機A的非對稱路由參數
主機A的路由參數
[root@compute ~]# sysctl -a|grep rp_filter
net.ipv4.conf.all.rp_filter = 1
net.ipv4.conf.all.arp_filter = 0
net.ipv4.conf.default.rp_filter = 1
net.ipv4.conf.default.arp_filter = 0
net.ipv4.conf.lo.rp_filter = 1
net.ipv4.conf.lo.arp_filter = 0
net.ipv4.conf.eth0.rp_filter = 1
net.ipv4.conf.eth0.arp_filter = 0
net.ipv4.conf.eth1.rp_filter = 1
net.ipv4.conf.eth1.arp_filter = 0
net.ipv4.conf.eth2.rp_filter = 1
net.ipv4.conf.eth2.arp_filter = 0
設置主機A的default.rp_filter
[root@compute ~]# sysctl -w net.ipv4.conf.default.rp_filter=0
[root@compute ~]# sysctl -a|grep rp_filter
net.ipv4.conf.all.rp_filter = 1
net.ipv4.conf.all.arp_filter = 0
net.ipv4.conf.default.rp_filter = 0
net.ipv4.conf.default.arp_filter = 0
net.ipv4.conf.lo.rp_filter = 1
net.ipv4.conf.lo.arp_filter = 0
net.ipv4.conf.eth0.rp_filter = 1
net.ipv4.conf.eth0.arp_filter = 0
net.ipv4.conf.eth1.rp_filter = 1
net.ipv4.conf.eth1.arp_filter = 0
net.ipv4.conf.eth2.rp_filter = 1
net.ipv4.conf.eth2.arp_filter = 0
在主機B上繼續ping
[root@storage ~]# ping -I 172.16.1.254 10.0.208.181
PING 10.0.208.181 (10.0.208.181) from 172.16.1.254 : 56(84) bytes of data.
^C
--- 10.0.208.181 ping statistics ---
5 packets transmitted, 0 received, 100% packet loss, time 4662ms
發現還是不通
step3:在主機A上添加到172網段的路由
在主機A上添加路由172.16.1.0/24,下一跳指向主機B的eth0端口
[root@compute ~]# ip route add 172.16.1.0/24 via 10.0.208.194
[root@compute ~]# route -n
Kernel IP routing table
Destination Gateway Genmask Flags Metric Ref Use Iface
10.0.208.0 0.0.0.0 255.255.255.0 U 0 0 0 eth0
10.0.0.0 0.0.0.0 255.255.255.0 U 0 0 0 eth1
10.0.1.0 0.0.0.0 255.255.255.0 U 0 0 0 eth2
172.16.1.0 10.0.208.194 255.255.255.0 UG 0 0 0 eth0
169.254.0.0 0.0.0.0 255.255.0.0 U 1002 0 0 eth0
169.254.0.0 0.0.0.0 255.255.0.0 U 1003 0 0 eth1
169.254.0.0 0.0.0.0 255.255.0.0 U 1004 0 0 eth2
0.0.0.0 10.0.208.254 0.0.0.0 UG 0 0 0 eth0
此時在主機B上就可以ping通了
[root@storage ~]# ping -I 172.16.1.254 10.0.208.181
PING 10.0.208.181 (10.0.208.181) from 172.16.1.254 : 56(84) bytes of data.
64 bytes from 10.0.208.181: icmp_seq=1 ttl=64 time=0.414 ms
64 bytes from 10.0.208.181: icmp_seq=2 ttl=64 time=0.417 ms
64 bytes from 10.0.208.181: icmp_seq=3 ttl=64 time=0.360 ms
^C
--- 10.0.208.181 ping statistics ---
3 packets transmitted, 3 received, 0% packet loss, time 2294ms
rtt min/avg/max/mdev = 0.360/0.397/0.417/0.026 ms
結論:這個問題的根本原因在於:
在主機A上,默認網關指向10.0.208.254,當收到源地址是172.16.1.254的包時,回覆的包的目的地址是172.16.1.254,而主機A不知道172網段在哪裏,就會將該包發給網關10.0.208.254,而這個網關上也沒有到172.16.1.0/24網段的路由,所以就丟棄了。解決方法是在主機A上添加172.16.1.0/24網段的靜態路由,下一跳指向主機B的10.0.208.194地址即可。這是一個純粹的路由問題,之所以放到這篇文章中,就是要提醒大家在測試的時候要注意這種情況。
*********************************
【情況2】這是遇到的實際問題,實際項目中的IP地址被我修改成了10網段
*********************************
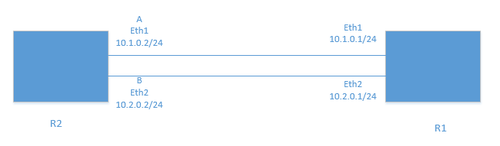
在R1上,執行ping -c 100 -I 10.1.0.1 10.2.0.2不通,需要能夠ping通。也就是在R1上,在ping的時候指定了原IP爲eth1接口的IP,目的IP爲R2的eth2接口IP
默認情況下是無法ping通的
情況2和情況3基本上是一樣的,只是情況3需要多配置一步而已
標紅的是使用到的端口
step1:查看三臺設備的端口IP和路由
controller R2 ,本例中使用eth1/2
[root@controller ~]# ip addr list|egrep -E 'mtu|inet'|grep -v inet6
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN
inet 127.0.0.1/8 scope host lo
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen 1000
inet 10.0.208.179/24 brd 10.0.208.255 scope global eth0
3: eth1: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen 1000
inet 10.1.0.2/24 brd 10.1.0.255 scope global eth1
4: eth2: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen 1000
inet 10.2.0.2/24 brd 10.2.0.255 scope global eth2
[root@controller ~]# ip route
10.0.208.0/24 dev eth0 proto kernel scope link src 10.0.208.179
10.2.0.0/24 dev eth2 proto kernel scope link src 10.2.0.2
10.1.0.0/24 dev eth1 proto kernel scope link src 10.1.0.2
169.254.0.0/16 dev eth0 scope link metric 1002
169.254.0.0/16 dev eth1 scope link metric 1003
169.254.0.0/16 dev eth2 scope link metric 1004
default via 10.1.0.1 dev eth1
network R1 ,本例中使用eth1/2/3
[root@network ~]# ip addr list|egrep -E 'mtu|inet'|grep -v inet6
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN
inet 127.0.0.1/8 scope host lo
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen 1000
inet 10.0.208.180/24 brd 10.0.208.255 scope global eth0
3: eth1: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen 1000
inet 10.1.0.1/24 brd 10.1.0.255 scope global eth1
4: eth2: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen 1000
inet 10.2.0.1/24 brd 10.2.0.255 scope global eth2
5: eth3: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen 1000
inet 10.3.0.1/24 brd 10.3.0.255 scope global eth3
[root@network ~]# ip route
10.0.208.0/24 dev eth0 proto kernel scope link src 10.0.208.180
10.2.0.0/24 dev eth2 proto kernel scope link src 10.2.0.1
10.3.0.0/24 dev eth3 proto kernel scope link src 10.3.0.1
10.1.0.0/24 dev eth1 proto kernel scope link src 10.1.0.1
169.254.0.0/16 dev eth0 scope link metric 1002
169.254.0.0/16 dev eth1 scope link metric 1003
169.254.0.0/16 dev eth2 scope link metric 1004
169.254.0.0/16 dev eth3 scope link metric 1005
default via 10.0.208.254 dev eth0
在R1上ping -I 10.1.0.1 10.2.0.2是不通的
step2:在R2上修改反向路徑檢查參數
[root@controller ~]# sysctl -a |grep -i rp_filter
net.ipv4.conf.all.rp_filter = 0
net.ipv4.conf.all.arp_filter = 0
net.ipv4.conf.default.rp_filter = 1
net.ipv4.conf.default.arp_filter = 0
net.ipv4.conf.lo.rp_filter = 1
net.ipv4.conf.lo.arp_filter = 0
net.ipv4.conf.eth0.rp_filter = 1
net.ipv4.conf.eth0.arp_filter = 0
net.ipv4.conf.eth1.rp_filter = 1
net.ipv4.conf.eth1.arp_filter = 0
net.ipv4.conf.eth2.rp_filter = 1
net.ipv4.conf.eth2.arp_filter = 0
sysctl -w net.ipv4.conf.default.rp_filter=0 ###禁用反向路徑檢查
sysctl -w net.ipv4.conf.eth1.rp_filter=0 ###注意:要設置default和所有使用到的接口的參數,不能只設置default
sysctl -w net.ipv4.conf.eth2.rp_filter=0 ###同上
[root@controller ~]# sysctl -a |grep -i rp_filter
net.ipv4.conf.all.rp_filter = 0
net.ipv4.conf.all.arp_filter = 0
net.ipv4.conf.default.rp_filter = 0
net.ipv4.conf.default.arp_filter = 0
net.ipv4.conf.lo.rp_filter = 1
net.ipv4.conf.lo.arp_filter = 0
net.ipv4.conf.eth0.rp_filter = 1
net.ipv4.conf.eth0.arp_filter = 0
net.ipv4.conf.eth1.rp_filter = 0
net.ipv4.conf.eth1.arp_filter = 0
net.ipv4.conf.eth2.rp_filter = 0
net.ipv4.conf.eth2.arp_filter = 0
之後在R1上ping -I 10.1.0.1 10.2.0.2還是不通
step3:繼續在R1上也修改反向路徑檢查參數
sysctl -w net.ipv4.conf.default.rp_filter=0
sysctl -w net.ipv4.conf.eth1.rp_filter=0
sysctl -w net.ipv4.conf.eth2.rp_filter=0
[root@network ~]# ping -I 10.1.0.1 10.2.0.2
PING 10.2.0.2 (10.2.0.2) from 10.1.0.1 : 56(84) bytes of data.
64 bytes from 10.2.0.2: icmp_seq=1 ttl=64 time=0.352 ms
64 bytes from 10.2.0.2: icmp_seq=2 ttl=64 time=0.454 ms
64 bytes from 10.2.0.2: icmp_seq=3 ttl=64 time=0.316 ms
^C
--- 10.2.0.2 ping statistics ---
3 packets transmitted, 3 received, 0% packet loss, time 2302ms
結論:
1 可以看到,在R2和R1上都禁用了反向路由檢查參數(注意:是所有使用到的接口+default)之後,才能在R1上ping通
2 反向路徑檢查參數就是控制是否允許非對稱路由的。默認是打開反向路徑檢查(1),不允許非對稱路由;設置爲0表示禁用反向路徑檢查,允許非對稱路由。
3 原理如下:默認情況下是打開反向路徑檢查的,這是爲了阻止地址欺騙***。所以,默認情況下,在R1上ping -I 10.1.0.1 10.2.0.2的時候,發送的數據包【源地址:10.1.0.1,目的地址:10.2.0.2】會從R1的eth2(10.2.0.1)出去,到R2的eth2(10.2.0.2)接口,因爲R1的路由表上有到10.2.0.0/24網段的路由,出口是eth2(詳見R1的路由表);而R2收到包後,需要檢查反向路由,此時的包【源地址:10.2.0.2,目的地址:10.1.0.1】會從R2的eth1(10.1.0.2)出去,到R1的eth1(10.1.0.1)接口,因爲R2的路由表上有到10.1.0.0/24網段的路由,出口是eth1(詳見R2的路由表),這樣,對R2和R1來說就造成了非對稱路由。解決方法就是禁止反向路由檢查。
需要注意的是:有時路由條目的緩存會影響測試效果,所以在每次配置修改完成後先刷新一下路由緩存:ip route flush cache
*********************************
【情況3】這是我從網上看到的也測試了一下,鏈接如下:http://m.blog.csdn.net/layrong/article/details/45673037
*********************************
要求如下:
如果一臺主機(或路由器)從接口A收到一個包,其源地址和目的地址分別是10.3.0.2和10.2.0.2,
即<saddr=10.3.0.2, daddr=10.2.0.2, iif=A>, 如果啓用反向路徑過濾功能,它就會以<saddr=10.2.0.2, daddr=10.3.0.2>爲關鍵字去查找路由表,如果得到的輸 出接口不爲A,則認爲反向路徑過濾檢查失敗,它就會丟棄該包。
假設R2的兩個接口分別爲A(10.1.0.2)、B(10.2.0.2)。 從PC ping 10.2.0.2時,包的路徑是PC-->10.3.0.1-->10.2.0.2, 此時包的 <saddr=10.3.0.2, daddr=10.2.0.2, iif=B>, 以<saddr=10.2.0.2, daddr=10.3.0.2>進行反向路徑檢查, 得到輸出設備是A, 因爲目的地址是10.3.0.2,只能使用默認路由。A!=B,反向路徑檢查失敗, 丟棄該包!
step1:查看三臺設備的端口IP和路由
controller R2 ,本例中使用eth1/2
[root@controller ~]# ip addr list|egrep -E 'mtu|inet'|grep -v inet6
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN
inet 127.0.0.1/8 scope host lo
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen 1000
inet 10.0.208.179/24 brd 10.0.208.255 scope global eth0
3: eth1: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen 1000
inet 10.1.0.2/24 brd 10.1.0.255 scope global eth1
4: eth2: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen 1000
inet 10.2.0.2/24 brd 10.2.0.255 scope global eth2
[root@controller ~]# ip route
10.0.208.0/24 dev eth0 proto kernel scope link src 10.0.208.179
10.2.0.0/24 dev eth2 proto kernel scope link src 10.2.0.2
10.1.0.0/24 dev eth1 proto kernel scope link src 10.1.0.2
169.254.0.0/16 dev eth0 scope link metric 1002
169.254.0.0/16 dev eth1 scope link metric 1003
169.254.0.0/16 dev eth2 scope link metric 1004
default via 10.1.0.1 dev eth1
network R1 ,本例中使用eth1/2/3
[root@network ~]# ip addr list|egrep -E 'mtu|inet'|grep -v inet6
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN
inet 127.0.0.1/8 scope host lo
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen 1000
inet 10.0.208.180/24 brd 10.0.208.255 scope global eth0
3: eth1: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen 1000
inet 10.1.0.1/24 brd 10.1.0.255 scope global eth1
4: eth2: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen 1000
inet 10.2.0.1/24 brd 10.2.0.255 scope global eth2
5: eth3: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen 1000
inet 10.3.0.1/24 brd 10.3.0.255 scope global eth3
[root@network ~]# ip route
10.0.208.0/24 dev eth0 proto kernel scope link src 10.0.208.180
10.2.0.0/24 dev eth2 proto kernel scope link src 10.2.0.1
10.3.0.0/24 dev eth3 proto kernel scope link src 10.3.0.1
10.1.0.0/24 dev eth1 proto kernel scope link src 10.1.0.1
169.254.0.0/16 dev eth0 scope link metric 1002
169.254.0.0/16 dev eth1 scope link metric 1003
169.254.0.0/16 dev eth2 scope link metric 1004
169.254.0.0/16 dev eth3 scope link metric 1005
default via 10.0.208.254 dev eth0
comput PC ,本例中只使用eth3
[root@compute ~]# ip addr list|egrep -E 'mtu|inet'|grep -v inet6
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN
inet 127.0.0.1/8 scope host lo
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen 1000
inet 10.0.208.181/24 brd 10.0.208.255 scope global eth0
3: eth1: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen 1000
inet 10.0.0.31/24 brd 10.0.0.255 scope global eth1
4: eth2: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen 1000
inet 10.0.1.31/24 brd 10.0.1.255 scope global eth2
5: eth3: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen 1000
inet 10.3.0.2/24 brd 10.3.0.255 scope global eth3
[root@compute ~]# ip route
10.0.208.0/24 dev eth0 proto kernel scope link src 10.0.208.181
10.0.0.0/24 dev eth1 proto kernel scope link src 10.0.0.31
10.0.1.0/24 dev eth2 proto kernel scope link src 10.0.1.31
10.3.0.0/24 dev eth3 proto kernel scope link src 10.3.0.2
169.254.0.0/16 dev eth0 scope link metric 1002
169.254.0.0/16 dev eth1 scope link metric 1003
169.254.0.0/16 dev eth2 scope link metric 1004
169.254.0.0/16 dev eth3 scope link metric 1005
default via 10.3.0.1 dev eth3
在PC上ping 10.2.0.2或者掛着源IP 10.3.0.2來ping 10.2.0.2(都是一樣的),都是不通的
[root@compute ~]# ping 10.2.0.2
[root@compute ~]# ping -I 10.3.0.2 10.2.0.2
step2:在R2上修改內核參數
[root@controller ~]# sysctl -a |grep -i rp_filter
net.ipv4.conf.all.rp_filter = 0
net.ipv4.conf.all.arp_filter = 0
net.ipv4.conf.default.rp_filter = 1
net.ipv4.conf.default.arp_filter = 0
net.ipv4.conf.lo.rp_filter = 1
net.ipv4.conf.lo.arp_filter = 0
net.ipv4.conf.eth0.rp_filter = 1
net.ipv4.conf.eth0.arp_filter = 0
net.ipv4.conf.eth1.rp_filter = 1
net.ipv4.conf.eth1.arp_filter = 0
net.ipv4.conf.eth2.rp_filter = 1
net.ipv4.conf.eth2.arp_filter = 0
sysctl -w net.ipv4.conf.default.rp_filter=0 ###禁用反向路徑檢查
sysctl -w net.ipv4.conf.eth1.rp_filter=0 ###注意:要設置default和所有使用到的接口的參數,不能只設置default
sysctl -w net.ipv4.conf.eth2.rp_filter=0 ###同上
[root@controller ~]# sysctl -a|grep rp_filter
net.ipv4.conf.all.rp_filter = 0
net.ipv4.conf.all.arp_filter = 0
net.ipv4.conf.default.rp_filter = 0
net.ipv4.conf.default.arp_filter = 0
net.ipv4.conf.lo.rp_filter = 1
net.ipv4.conf.lo.arp_filter = 0
net.ipv4.conf.eth0.rp_filter = 1
net.ipv4.conf.eth0.arp_filter = 0
net.ipv4.conf.eth1.rp_filter = 0
net.ipv4.conf.eth1.arp_filter = 0
net.ipv4.conf.eth2.rp_filter = 0
net.ipv4.conf.eth2.arp_filter = 0
在R1上修改內核參數
sysctl -w net.ipv4.conf.default.rp_filter=0
sysctl -w net.ipv4.conf.eth1.rp_filter=0
sysctl -w net.ipv4.conf.eth2.rp_filter=0
[root@network ~]# sysctl -a|grep rp_filter
net.ipv4.conf.all.rp_filter = 0
net.ipv4.conf.all.arp_filter = 0
net.ipv4.conf.default.rp_filter = 0
net.ipv4.conf.default.arp_filter = 0
net.ipv4.conf.lo.rp_filter = 1
net.ipv4.conf.lo.arp_filter = 0
net.ipv4.conf.eth0.rp_filter = 1
net.ipv4.conf.eth0.arp_filter = 0
net.ipv4.conf.eth1.rp_filter = 0
net.ipv4.conf.eth1.arp_filter = 0
net.ipv4.conf.eth2.rp_filter = 0
net.ipv4.conf.eth2.arp_filter = 0
net.ipv4.conf.eth3.rp_filter = 1
net.ipv4.conf.eth3.arp_filter = 0
之後在PC上進行ping測試: ping -I 10.3.0.2 10.2.0.2 ,不通,這是因爲R1是作爲路由器使用的,需要在R1上打開轉發
step3:在R1上打開路由轉發:
[root@network ~]# sysctl -w net.ipv4.ip_forward=1
在R2/R1和PC上清空緩存,避免對測試產生影響
ip route flush cache
此時在PC上進行ping測試: ping -I 10.3.0.2 10.2.0.2 通了
結論:
1 可以看到,在R2和R1上都禁用了反向路由檢查參數(注意:是所有使用到的接口+default)之後,並且在R1上打開了路由轉發,才能在PC上ping通
2 原理如下:默認情況下是打開反向路徑檢查的,這是爲了阻止地址欺騙***。所以,默認情況下,在PC上ping -I 10.3.0.2 10.2.0.2 的時候,發送的數據包【源地址:10.3.0.2,目的地址:10.2.0.2】會從到R1的eth3接口,之後從R1的eth2(10.2.0.1)出去,到R2的eth2(10.2.0.2)接口,因爲R1的路由表上有到10.2.0.0/24網段的路由,出口是eth2(詳見R1的路由表);而R2收到包後,需要檢查反向路由,此時的包【源地址:10.2.0.2,目的地址:10.3.0.2】會從R2的eth1(10.1.0.2)出去,到R1的eth1(10.1.0.1)接口,因爲R2的路由表上的默認路由可以到達10.3.0.0/24網段,出口是eth1(詳見R2的路由表),這樣,對R2和R1來說就造成了非對稱路由。解決方法就是禁止反向路由檢查以允許非對稱路由。
需要說明的是:在http://m.blog.csdn.net/layrong/article/details/45673037這個鏈接中,作者提到了兩種方法,第二種方法是給R2上添加了一條靜態路由:[root@controller ~]# ip route add 10.3.0.0/24 via 10.2.0.1,也確實可以實現ping通的目標,需要注意的是,對於第二種方法:
也需要設置R1的路由轉發
不需要在R1/R2上關閉反向路由解析(使用默認的打開模式即可),因爲此時我在R2上添加了一條到10.3.0.0/24網段的靜態路由,是走R2的eth2(10.2.0.2)接口,之後到R1的eth2(10.2.0.1)接口的,數據包會走這條明細路由,而不會像之前那樣走默認路由了,此時就是對稱路由了。