具體原理及參數可以參考:https://blog.51cto.com/14227204/2449696
這裏我就不詳細說明了,大致原理都一樣,我就直接開整了
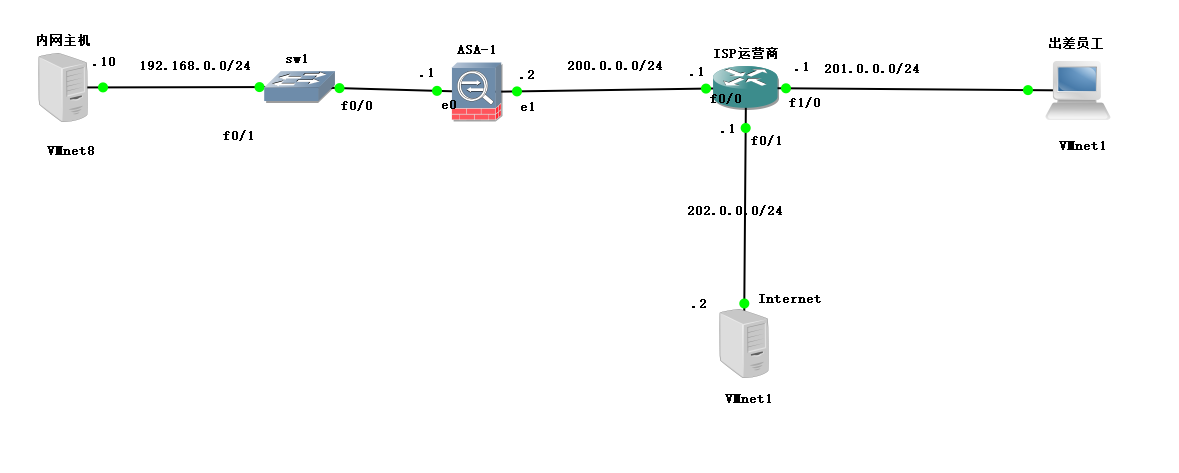
1、環境如下:
2、開始配置(自行配置接口IP)
ASA 配置如下:
ciscoasa> en
Password:
ciscoasa# conf t
ciscoasa(config)# int e 0/0
ciscoasa(config-if)# nameif inside
INFO: Security level for "inside" set to 100 by default.
ciscoasa(config-if)# ip add 192.168.0.1
ciscoasa(config-if)# no shutdown
ciscoasa(config-if)# exit
ciscoasa(config)# int e 0/1
ciscoasa(config-if)# nameif outside
INFO: Security level for "outside" set to 0 by default.
ciscoasa(config-if)# ip add 200.0.0.2
ciscoasa(config-if)# no shutdown
ciscoasa(config)# route outside 0 0 200.0.0.1 # 0代表0.0.0.0
# ASA中的AAA默認開啓,所以不需要手動開啓了
ciscoasa(config)# username zhangsan password 123123 # 配置AAA認證用戶
ciscoasa(config)# crypto isakmp enable outside # 開啓IKE協商功能
# 階段一:指定管理連接的相關參數,加密算法等
ciscoasa(config)# crypto isakmp policy 10
ciscoasa(config-isakmp-policy)# encryption 3des
ciscoasa(config-isakmp-policy)# hash sha
ciscoasa(config-isakmp-policy)# authentication pre-share
ciscoasa(config-isakmp-policy)# group 2
ciscoasa(config-isakmp-policy)# exit
ciscoasa(config)# ip local pool test-pool 192.168.1.200-192.168.1.210 # 創建地址池
ciscoasa(config)# access-list split-acl permit ip 192.168.0.0 255.255.255.0 any # 編寫ACl
ciscoasa(config)# group-policy test-group internal
ciscoasa(config)# group-policy test-group attributes
ciscoasa(config-group-policy)# split-tunnel-policy tunnelspecified
ciscoasa(config-group-policy)# split-tunnel-network-list value split-acl
ciscoasa(config-group-policy)# exit
ciscoasa(config)# tunnel-group test1-group type ipsec-ra
ciscoasa(config)# tunnel-group test1-group general-attributes
ciscoasa(config-tunnel-general)# address-pool test-pool # 應用所創建的地址池
ciscoasa(config-tunnel-general)# default-group-policy test-group
ciscoasa(config-tunnel-general)# exit
ciscoasa(config)# tunnel-group test1-group ipsec-attributes
ciscoasa(config-tunnel-ipsec)# pre-shared-key 321321 # 配置組密鑰
ciscoasa(config-tunnel-ipsec)# exit
ciscoasa(config)# crypto ipsec transform-set test-set esp-3des esp-sha-hmac
ciscoasa(config)# crypto dynamic-map test-dymap 1 set transform-set test-set
ciscoasa(config)# crypto map test-stamap 1000 ipsec-isakmp dynamic test-dymap
ciscoasa(config)# crypto map test-stamap int outside # 應用到接口客戶端安裝也可參考:https://blog.51cto.com/14227204/2449696 (後半部分)
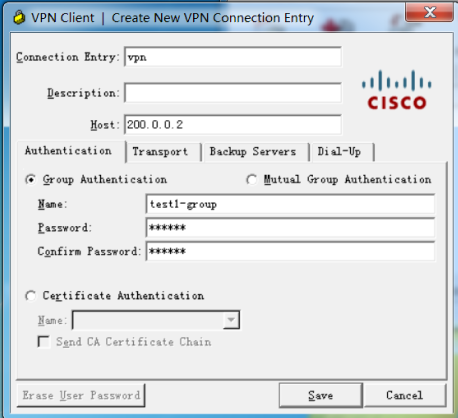
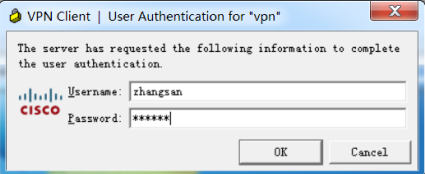
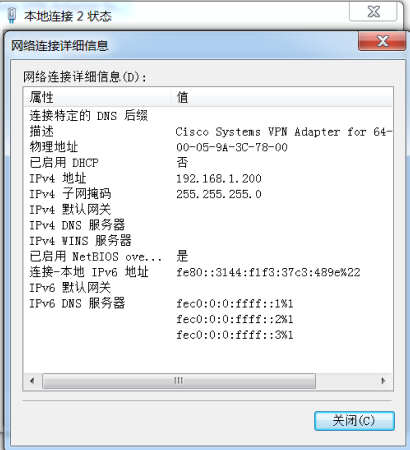
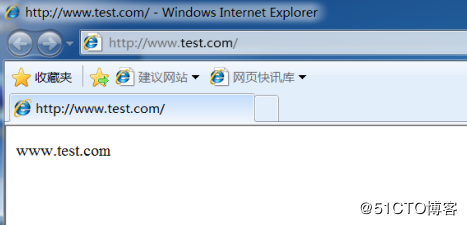
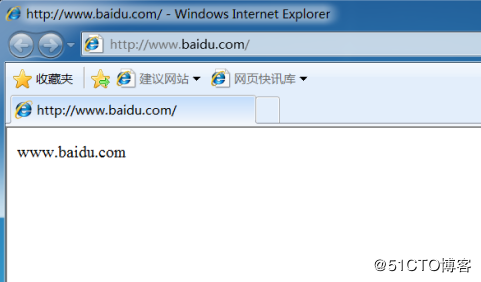
3、驗證