系統環境:
CentOS 6.75
Open*** 2.3.11
安裝過程
1、安裝EPEL6的yum源並更新本地緩存
1 2 | #rpm -ivh http://mirrors.sohu.com/fedora-epel/6/x86_64/epel-release-6-8.noarch.rpm #yum makecache |
2、關閉SElinux和防火牆
1 2 | [root@localhost ~]# service iptables stop [root@localhost ~]# chkconfig iptables off |
1 | vi /etc/sysconfig/selinux |
1 2 3 4 5 6 7 8 9 10 | # This file controls the state of SELinux on the system. # SELINUX= can take one of these three values: # enforcing - SELinux security policy is enforced. # permissive - SELinux prints warnings instead of enforcing. # disabled - No SELinux policy is loaded. SELINUX=disabled # SELINUXTYPE= can take one of these two values: # targeted - Targeted processes are protected, # mls - Multi Level Security protection. SELINUXTYPE=targeted |
1 | reboot //重啓server |
3、安裝open*** 和easy-rsa
1 | [root@localhost ~]# yum -y install open*** easy-rsa |
4、easy-rsa配置
1 2 | [root@localhost ~]# mkdir -p /etc/open***/easy-rsa/keys [root@localhost ~]# cp -rf /usr/share/easy-rsa/2.0/* /etc/open***/easy-rsa/ |
5、創建CA證書和密鑰
a、vi /etc/open***/easy-rsa/vars //修改以下內容
1 2 3 4 5 6 | export KEY_COUNTRY="CN" //所在國家 export KEY_PROVINCE="SH" //所在省份 export KEY_CITY="Shanghai" //所在省份 export KEY_ORG="Open*** ORG" //所在組織 export KEY_OU="Open***" //所在單位 |
b、初始化證書的授權中心
1 2 3 4 | [root@localhost easy-rsa]# pwd /etc/open***/easy-rsa[root@localhost easy-rsa]# source ./vars NOTE: If you run ./clean-all, I will be doing a rm -rf on /etc/open***/easy-rsa/keys |
c、清除已存在的證書文件
1 2 3 | [root@localhost easy-rsa]# ./clean-all [root@localhost easy-rsa]# ls keys/ index.txt serial |
d、創建CA證書, 一路回車即可
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 | [root@localhost easy-rsa]# ./build-ca Generating a 2048 bit RSA private key ..........................+++ ............+++ writing new private key to 'ca.key'----- You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter '.', the field will be left blank. ----- Country Name (2 letter code) [CN]: State or Province Name (full name) [SH]: Locality Name (eg, city) [Shanghai]: Organization Name (eg, company) [Open*** ORG]: Organizational Unit Name (eg, section) [Open***]: Common Name (eg, your name or your server's hostname) [Open*** ORG CA]: Name [EasyRSA]: Email Address [[email protected]]: [root@localhost easy-rsa]# |
1 2 | [root@localhost easy-rsa]# ls keys/ ca.crt ca.key index.txt serial |
e、創建服務器端證書,server爲證書名稱
1 | ./build-key-server server |
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 | [root@localhost easy-rsa]# ./build-key-server server Generating a 2048 bit RSA private key ..........+++ ...............................+++ writing new private key to 'server.key'----- You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter '.', the field will be left blank. ----- Country Name (2 letter code) [CN]: State or Province Name (full name) [SH]: Locality Name (eg, city) [Shanghai]: Organization Name (eg, company) [Open*** ORG]: Organizational Unit Name (eg, section) [Open***]: Common Name (eg, your name or your server's hostname) [server]: Name [EasyRSA]: Email Address [[email protected]]: Please enter the following 'extra' attributes to be sent with your certificate request A challenge password []: An optional company name []: Using configuration from /etc/open***/easy-rsa/openssl-1.0.0.cnf Check that the request matches the signature Signature ok The Subject's Distinguished Name is as follows countryName :PRINTABLE:'CN'stateOrProvinceName :PRINTABLE:'SH'localityName :PRINTABLE:'Shanghai'organizationName :PRINTABLE:'Open*** ORG'organizationalUnitName:PRINTABLE:'Open***'commonName :PRINTABLE:'server'name :PRINTABLE:'EasyRSA'emailAddress :IA5STRING:'[email protected]'Certificate is to be certified until Aug 13 02:14:17 2026 GMT (3650 days) Sign the certificate? [y/n]:y 1 out of 1 certificate requests certified, commit? [y/n]y Write out database with 1 new entries Data Base Updated |
注意: 以下兩個地方設置爲yes
1 | Sign the certificate? [y/n]:y |
1 | 1 out of 1 certificate requests certified, commit? [y/n]y |
1 2 3 | [root@localhost easy-rsa]# ls keys/ 01.pem ca.key index.txt.attr serial server.crt server.key ca.crt index.txt index.txt.old serial.old server.csr |
f、生成Diffie-Hellman文件
1 2 3 | ./build-dhGenerating DH parameters, 2048 bit long safe prime, generator 2 This is going to take a long time |
1 2 3 | [root@localhost easy-rsa]# ls keys 01.pem ca.key index.txt index.txt.old serial.old server.csr ca.crt dh2048.pem index.txt.attr serial server.crt server.key |
g、生成TLS-auth密鑰
這一步是可選操作,open***提供了TLS-auth功能,可以用來抵禦Dos、UDP端口淹沒***。出於安全考慮,可以啓用該功能。執行以下命令來生成TLS-auth所需要的密鑰文件
1 2 3 4 | [root@localhost easy-rsa]# open*** --genkey --secret keys/ta.key [root@localhost easy-rsa]# ls keys/ 01.pem ca.key index.txt index.txt.old serial.old server.csr ta.key ca.crt dh2048.pem index.txt.attr serial server.crt server.key |
6、拷貝服務器端證書、密鑰等
1 2 3 4 5 6 | [root@localhost keys]# pwd /etc/open***/easy-rsa/keys[root@localhost keys]# cp server.crt server.key dh2048.pem ca.crt ta.key /etc/open***/ [root@localhost keys]# cd /etc/open***/ [root@localhost open***]# ls ca.crt dh2048.pem easy-rsa server.crt server.key ta.key |
7、修改服務器端配置文件
注意:Open***推薦使用證書進行認證,安全性很高,但是配置起來很麻煩。還好它也能像pptp等***一樣使用用戶名/密碼進行認證。不管何種認證方式,服務端的ca.crt, server.crt, server.key, dh1024.pem這四個證書都是要的。使用username/passwd方式,你需要在服務器配置文件中加入以下語句,取消客戶端的證書認證,如果不加下面這條指令,則表示需要證書和用戶名密碼雙重驗證登錄!
1 | client-cert-not-required |
然後加入auth-user-pass-verify,開啓用戶密碼腳本:
1 | auth-user-pass-verify /etc/open***/checkpsw.sh via-env |
加入script-security消除警告
1 | script-security 3 system |
checkpsw.sh腳本可以通過網絡獲取
1 | wget http://open***.se/files/other/checkpsw.sh |
如果下載失敗,可以創建一個checkpsw.sh文件,注意複製文件到linux系統下換行符的問題
內容如下,只需要修改PASSFILE和LOG_FILE兩個變量
# cd /usr/local/open***/etc/
# wget http://open***.se/files/other/checkpsw.sh
# chmod +x checkpsw.sh
# cat checkpsw.sh
#!/bin/sh
###########################################################
# checkpsw.sh (C) 2004 Mathias Sundman <mathias@open***.se>
#
# This script will authenticate Open*** users against
# a plain text file. The passfile should simply contain
# one row per user with the username first followed by
# one or more space(s) or tab(s) and then the password.
PASSFILE="/etc/open***/psw-file"
LOG_FILE="/etc/open***/open***-password.log"
TIME_STAMP=`date "+%Y-%m-%d %T"`
###########################################################
if [ ! -r "${PASSFILE}" ]; then
echo "${TIME_STAMP}: Could not open password file \"${PASSFILE}\" for reading." >>
${LOG_FILE}
exit 1
fi
CORRECT_PASSWORD=`awk '!/^;/&&!/^#/&&$1=="'${username}'"{print $2;exit}' ${PASSFILE}`
if [ "${CORRECT_PASSWORD}" = "" ]; then
echo "${TIME_STAMP}: User does not exist: username=\"${username}\", password=\"${password}\"." >> ${LOG_FILE}
exit 1
fi
if [ "${password}" = "${CORRECT_PASSWORD}" ]; then
echo "${TIME_STAMP}: Successful authentication: username=\"${username}\"." >> ${LOG_FILE}
exit 0
fi
echo "${TIME_STAMP}: Incorrect password: username=\"${username}\", password=\"${password}\"." >> ${LOG_FILE}
exit 1
checkpsw.sh默認從文件/etc/open***/psw-file中讀取用戶名密碼。
賦予checkpsw.sh文件可執行權限
1 | chmod +x checkpsw.sh |
psw-file中一行是一個賬號,用戶名和密碼之間用空格隔開,如:
username password
修改psw-file文件的權限,保證open***用戶對該文件有讀取權限
1 2 3 4 5 6 7 8 9 10 11 12 13 | [root@localhost open***]# chmod 400 psw-file [root@localhost open***]# chown nobody.nobody psw-file [root@localhost open***]# ll total 48 -rw-r--r-- 1 root root 1732 Aug 15 11:03 ca.crt -rw-r--r-- 1 root root 1267 Aug 15 12:49 checkpsw.sh -rw-r--r-- 1 root root 424 Aug 15 11:03 dh2048.pem drwxr-xr-x 3 root root 4096 Aug 15 10:09 easy-rsa -r-------- 1 nobody nobody 28 Aug 15 12:50 psw-file-rw-r--r-- 1 root root 10749 Aug 15 12:56 server.conf -rw-r--r-- 1 root root 5483 Aug 15 11:03 server.crt -rw------- 1 root root 1704 Aug 15 11:03 server.key -rw------- 1 root root 636 Aug 15 11:03 ta.key |
拷貝server.conf 配置文件
1 2 3 | [root@localhost open***]# cp /usr/share/doc/open***-2.3.11/sample/sample-config-files/server.conf /etc/open***/server.conf [root@localhost open***]# ls ca.crt dh2048.pem easy-rsa server.conf server.crt server.key ta.key |
修改server.conf,配置如下:
1 | [root@localhost open***]# cat server.conf|egrep -v "^#|^;|^$" |
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 | port 1194 //指定監聽的本機端口 proto udp //指定傳輸協議 dev tun //指定通信隧道類型 ca ca.crt //指定CA證書路徑 cert server.crt //指定服務器端證書路徑 key server.key //指定服務器端私鑰文件路徑 dh dh2048.pem //指定迪菲赫爾曼參數的文件路徑 server 10.8.0.0 255.255.255.0 //指定虛擬局域網段 ifconfig-pool-persist ipp.txt //服務器給客戶端分配的IP地址,下次客戶端繼續使用該IP push "dhcp-option DNS 8.8.8.8" //client-to-client //允許客戶端與客戶端相連接,默認情況下客戶端只能與服務器相連接 keepalive 10 120 //每10秒ping一次,連接超時時間設爲120秒 tls-auth ta.key 0 //開啓TLS-auth,使用ta.key防禦***。服務器端的第二個參數值爲0,客戶端的爲1。 comp-lzo //開啓***連接壓縮,如果服務器端開啓,客戶端也必須開啓 persist-key persist-tun //持久化選項可以儘量避免訪問在重啓時由於用戶權限降低而無法訪問的某些資源。 status open***-status.log //指定記錄Open***狀態的日誌文件路徑 log open***.log verb 3 //日誌級別 client-cert-not-required //不使用客戶端證書認證 username-as-common-name script-security 3 system auth-user-pass-verify /etc/open***/checkpsw.sh via-env // |
服務器端需要的文件,注意checkpsw.sh和psw-file兩個文件的權限和屬主屬組
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 | [root@localhost open***]# ll total 76 -rw-r--r-- 1 root root 1732 Aug 15 11:03 ca.crt -rwxr-xr-x 1 root root 1249 Aug 15 13:42 checkpsw.sh -rw-r--r-- 1 root root 424 Aug 15 11:03 dh2048.pem drwxr-xr-x 3 root root 4096 Aug 15 13:17 easy-rsa -rw------- 1 root root 23 Aug 15 15:25 ipp.txt -rw------- 1 root root 3813 Aug 15 15:17 open***.log -rw-r--r-- 1 root root 434 Aug 15 15:17 open***-password.log -rw------- 1 root root 371 Aug 15 15:28 open***-status.log -r-------- 1 nobody nobody 28 Aug 15 12:50 psw-file-rw-r--r-- 1 root root 10601 Aug 15 15:15 server.conf -rw-r--r-- 1 root root 10724 Aug 15 14:40 server.conf.bak -rw-r--r-- 1 root root 5483 Aug 15 11:03 server.crt -rw------- 1 root root 1704 Aug 15 11:03 server.key -rw------- 1 root root 636 Aug 15 11:03 ta.key |
8、修改客戶端配置文件client.conf
註釋掉客戶端證書的配置
client.conf配置文件內容
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 | client //指定當前***是客戶端 dev tun //必須與服務器端的保持一致 proto udp //必須與服務器端的保持一致 remote 172.16.100.225 1194 //指定連接的遠程服務器的實際IP地址和端口號 resolv-retry infinite //斷線自動重新連接,在網絡不穩定的情況下(例如:筆記本電腦無線網絡)非常有用。 nobind //不綁定特定的本地端口號 user nobody group nobody persist-key persist-tun ca ca.crt //指定CA證書的文件路徑 remote-cert-tls server // tls-auth ta.key 1 //tls認證開啓,必須與服務器一致 comp-lzo //必須與服務器一致 verb 3 auth-user-pass //增加詢問賬戶名密碼 |
9、windows客戶端的安裝和配置
下載open***的客戶端:http://www.open***.net/release/open***-2.0.9-install.exe
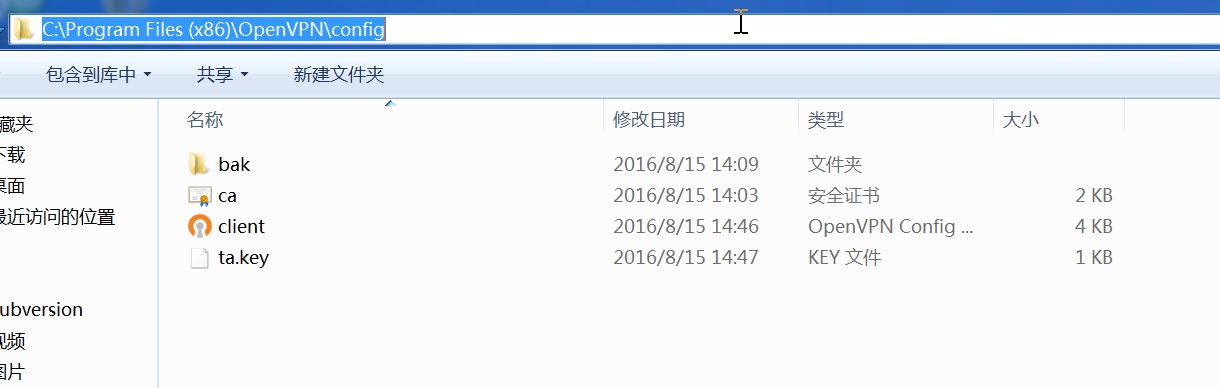
安裝完成後,將服務器端的
1 | ca.crt client.conf ta.key |
三個文件拷貝到open***安裝目錄下的config目錄中
登錄
雙擊“C:\Program Files (x86)\Open***\bin\open***-gui-1.0.3"圖標,在桌面右下角彈出open***的圖標,然後右鍵--client--Connect,輸出賬號密碼登錄
10、Open*** 服務器端的防火牆規則配置
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 | 上面的操作完成後,客戶端能夠訪問*** Server端,也能夠訪問其他的撥號進來的***客戶端,但是不能訪問與*** Server同網段的內網客戶端。原因是向內網其他客戶端發出請求後,內網客戶端沒有到***客戶端的路由,導致無法響應請求。比如說內網是192.168,1.0/24 網段。***客戶端地址段是10.8.0.0/24地址段,在內網客戶端上,沒有到達10.8.0.0/24的路由,所以不能響應內網的客戶端的請求。我們可以在內網客戶端上加一條路由來解決這個問題,但是客戶端有幾百個的話,一臺一臺的去加這個路由不是很麻煩嗎?我們可以通過在*** server上添加一條防火牆策略來解決,假設open*** 服務器的IP爲192.168.1.10 網卡爲eth0 iptables -t nat -A POSTROUTING -s 10.8.0.0/24 -o eth0 -j SNAT --to-source 192.168.1.10 注意:“SNAT --to-source 192.168.1.10” 可以用MASQUERADE來替換,表示地址僞裝,服務器會自動找到合適的IP地址來當成源IP,適用於無固定IP的情況下。如果IP經常變動則可以使用MASQUERADE 下面是網上找到的資料,也是配置Open***防火牆策略的 清空iptables配置: iptables -F iptables -X 配置open***的nat功能,將所有網段的包轉發到eth0口: iptables -t nat -A POSTROUTING -o eth0 -j MASQUERADE 添加FORWARD白名單: iptables -A FORWARD -i tun+ -j ACCEPT 開啓系統內核的路由功能:注意這一條很重要 echo "1" > /proc/sys/net/ipv4/ip_forward service iptables save //保存iptables配置 service iptables restart //重啓iptables |
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 | cat /etc/sysconfig/iptables# Generated by iptables-save v1.4.7 on Mon Aug 15 16:47:30 2016 *nat :PREROUTING ACCEPT [38:8664] :POSTROUTING ACCEPT [0:0] :OUTPUT ACCEPT [0:0] -A POSTROUTING -o eth0 -j MASQUERADE COMMIT # Completed on Mon Aug 15 16:47:30 2016 # Generated by iptables-save v1.4.7 on Mon Aug 15 16:47:30 2016 *filter :INPUT ACCEPT [218:28319] :FORWARD ACCEPT [0:0] :OUTPUT ACCEPT [95:13949] -A FORWARD -i tun+ -j ACCEPT COMMIT # Completed on Mon Aug 15 16:47:30 2016 |
參考資料:
http://www.cnblogs.com/linuxprobe/p/5428098.html
http://www.cnblogs.com/electron/p/3488033.html
http://ylw6006.blog.51cto.com/470441/1009004