Keepalived是集羣管理中保證集羣高可用的一個服務軟件,用來防止單點故障。它是以VRRP協議(虛擬路由冗餘協議)爲基礎的。 Keepalived主要有三個模塊,分別是core、check和vrrp。Core模塊是keepalived的核心模塊,主要負責主進程的啓動,維 護以及全局配置文件的加載和解析。Check模塊主要負責健康檢查。Vrrp模塊主要用來實現VRRP協議的。
LVS集羣採用三層結構,其主要組成部分爲:
A、負載調度器(load balancer),它是整個集羣對外面的前端機,負責將客戶的請求發送到一組服務器上執行,而客戶認爲服務是來自一個IP地址(我們可稱之爲虛擬IP地址)上的。
B、服務器池(server pool),是一組真正執行客戶請求的服務器,執行的服務有WEB、MAIL、FTP和DNS等。
C、共享存儲(shared storage),它爲服務器池提供一個共享的存儲區,這樣很容易使得服務器池擁有相同的內容,提供相同的服務。
VS/TUN技術對服務器有要求,即所有的服務器必須支持“ IP Tunneling”或者““ IP Encapsulation”協議。目前,VS/TUN的後端服務器主要運行 Linux 操作系統。在VS/TUN 的集羣系統中,負載調度器只將請求調度到不同的後端服務器,後端服務器將應答的數據直接返回給用戶。這樣,負載調度器就可以處理大量的請求,它甚至可以調 度百臺以上的服務器(同等規模的服務器),而它不會成爲系統的瓶頸。即使負載調度器只有100Mbps的全雙工網卡,整個系統的最大吞吐量可超過 1Gbps。所以,VS/TUN可以極大地增加負載調度器調度的服務器數量。VS/TUN調度器可以調度上百臺服務器,而它本身不會成爲系統的瓶頸,可以 用來構建高性能的超級服務器。
VS/NAT 的優點是服務器可以運行任何支持TCP/IP的操作系統,它只需要一個IP地址配置在調度器上,服務器組可以用私有的IP地址。缺點是它的伸縮能力有限, 當服務器結點數目升到20時,調度器本身有可能成爲系統的新瓶頸,因爲在VS/NAT中請求和響應報文都需要通過負載調度器。
VS/DR方式是通過改寫請求報文中的MAC地址部分來實現的。Director和RealServer必需在物理上有一個網卡通過不間斷的局域網相連。 RealServer上綁定的VIP配置在各自Non-ARP的網絡設備上(如lo或tunl),Director的VIP地址對外可見,而RealServer的VIP對外是不可見的。RealServer的地址即可以是內部地址,也可以是真實地址。
DR模式,VS和RS在同一網段。客戶端給vip發送請求,然後vip根據請求選擇合適的real server,然後vip將這個請求的地址改爲real server的地址。
TUN模式,支持廣域網連接,在數據傳輸過程也支持隧道協議。封裝過大的數據。
NAT模式,VS和RS不在同一網段。
準備工作:
4臺虛擬機:
server2和server3的內存1024
server7和server8的內存512
server3.example.com 172.25.85.3 1024M
server2.example.com 172.25.85.2 1024M (server2做調度)
server7.example.com 172.25.85.7 512M
server8.example.com 172.25.85.8 512M
1.在server7,server8上:
yum install httpd -y
/etc/init.d/httpd start
在server7上:
echo server7.linux.org > /var/www/html/index.html
ip addr add 172.25.85.100/32 dev eth0
在server8上:
echo server8.westos.org > /var/www/html/index.html
ip addr add 172.25.85.100/32 dev eth0
在server2上: ##server2作爲調度主機
ip addr add 172.25.85.100/24 dev eth0
ip addr show
ipsvadm --help
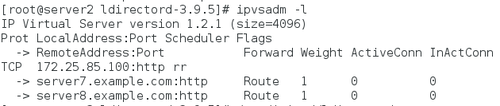
ipvsadm -A -t 172.25.85.100:80 -s rr ##加載 rule
##-A添加虛擬ip -s指定調度算法 -a添加real server -g直聯DR模式 -t tcp協議
ipvsadm -a -t 172.25.85.100:80 -r 172.25.85.7:80 -g
ipvsadm -a -t 172.25.85.100:80 -r 172.25.85.8:80 -g
ipvsadm -l
/etc/init.d/ipvsadm save ##將ipvsadm信息保存在/etc/sysconfig/ipvsadm/
2.在server7上:
yum install arptables_jf -y
arptables -A IN -d 172.25.85.100 -j DROP
arptables -A OUT -s 172.25.85.100 -j mangle --mangle-ip-s 172.25.85.7
/etc/init.d/arptables_jf save
/etc/init.d/httpd start
在server8上:
yum install arptables_jf -y
arptables -A IN -d 172.25.85.100 -j DROP
arptables -A OUT -s 172.25.85.100 -j mangle --mangle-ip-s 172.25.85.8
/etc/init.d/arptables_jf save
/etc/init.d/httpd stop
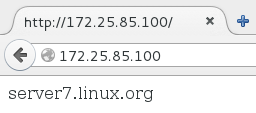
在瀏覽器中打開172.25.85.100
3.在server2上結合了heartbeat:
cd /usr/share/doc/ldirectord-3.9.5
cp ldirectord.cf /etc/ha.d
vim /etc/ha.d/ldirectord.cf
virtual=172.25.85.100:80 real=172.25.85.7:80 gate real=172.25.85.8:80 gate fallback=127.0.0.1:80 gate service=http scheduler=rr #persistent=600 #netmask=255.255.255.255 protocol=tcp checktype=negotiate checkport=80 request="index.html" # receive="Test Page" # virtualhost=www.x.y.z
ipvsadm -C
ipvsadm -l
/etc/init.d/ldirectord start
ipvsadm -l
scp /etc/ha.d/ldirectord.cf [email protected]:/etc/ha.d/
ip addr del 172.25.85.100/24 dev eth0
cd /etc/ha.d
vim haresources
server2.example.com IPaddr::172.25.85.100/24/eth1 httpd ldirectord
scp /etc/ha.d/haresources 172.25.85.3:/etc/ha.d/
/etc/init.d/heartbeat stop
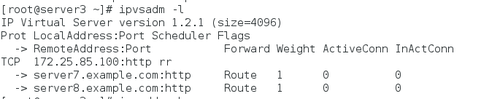
ipvsadm -l
在server3上:
/etc/init.d/heartbeat start
tail -f /var/log/messages
ipvsadm -l
ip addr show
出現虛擬ip172.25.85.100
如果開啓server2上的heartbeat。關閉server3上的heartbeat。虛擬ip出現在server2上。
4.在server3/2上:
/etc/init.d/heartbeat stop
/etc/init.d/ldirectord start
server3:
tar zxf keepalived-1.2.20.tar.gz
cd /root/keepalived-1.2.20
yum install openssl-devel libnl-devel net-snmp-devel -y
cd /root
rpm -ivh libnfnetlink-devel-1.0.0-1.el6.x86_64.rpm
cd /root/keepalived-1.2.20
./configure --prefix=/usr/local/keepalived ##編譯成功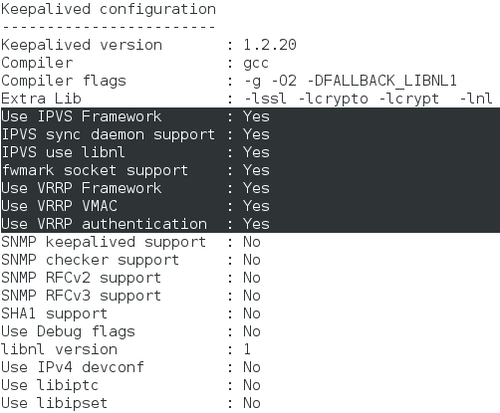
make
make install
cd /usr/local/
scp -r keepalived/ 172.25.85.3:/usr/local
cd /usr/local/keepalived/etc/rc.d/init.d/
ln -s /usr/local/keepalived/etc/rc.d/init.d/keepalived /etc/init.d/
ln -s /usr/local/keepalived/etc/sysconfig/keepalived /etc/sysconfig/
ln -s /usr/local/keepalived/etc/keepalived/ /etc/
ln -s /usr/local/keepalived/sbin/keepalived /sbin/
ln -s /usr/local/keepalived/bin/genhash /bin/
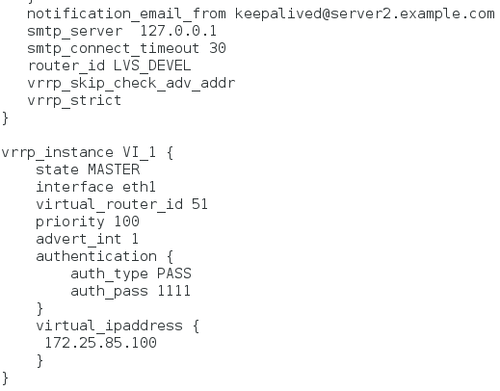
vim keepalived.conf
notification_email_from [email protected] smtp_server 127.0.0.1
vrrp_instance VI_1 {
state MASTER
interface eth1
virtual_router_id 51
priority 100
advert_int 1
authentication {
auth_type PASS
auth_pass 1111
}
virtual_ipaddress {
172.25.85.100
}
}
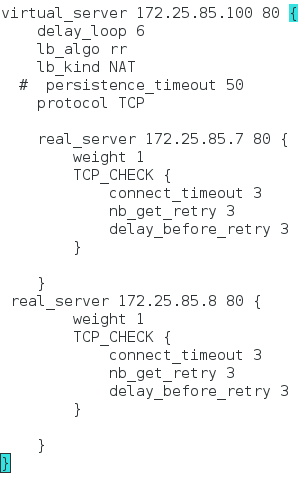
virtual_server 172.25.85.100 80 {
delay_loop 6
lb_algo rr
lb_kind NAT
# persistence_timeout 50
protocol TCP
real_server 172.25.85.7 80 {
weight 1
TCP_CHECK {
connect_timeout 3
nb_get_retry 3
delay_before_retry 3
}
}
real_server 172.25.85.8 80 {
weight 1
TCP_CHECK {
connect_timeout 3
nb_get_retry 3
delay_before_retry 3
}
}
}
scp keepalived.conf 172.25.85.3:/etc/keepalived/
/etc/init.d/keepalived start
tail -f /var/log/messages
在server3上:
ln -s /usr/local/keepalived/etc/rc.d/init.d/keepalived /etc/init.d/
ln -s /usr/local/keepalived/etc/sysconfig/keepalived /etc/sysconfig/
ln -s /usr/local/keepalived/etc/keepalived/ /etc/
ln -s /usr/local/keepalived/sbin/keepalived /sbin/
ln -s /usr/local/keepalived/bin/genhash /bin/
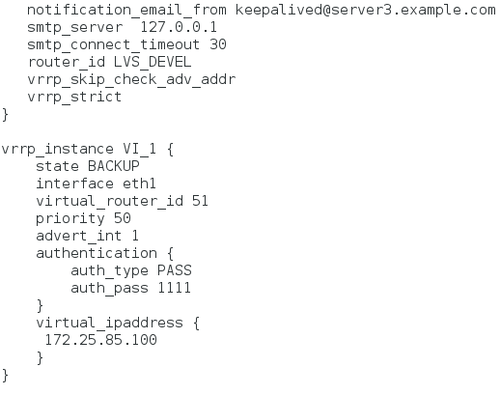
vim keepalived.conf
notification_email_from [email protected] smtp_server 127.0.0.1 vrrp_instance VI_1 { state BACKUP interface eth1 virtual_router_id 51 priority 50 advert_int 1 authentication { auth_type PASS auth_pass 1111 } virtual_ipaddress { 172.25.85.100 } }
/etc/init.d/keepalived start
檢測:
打開server7和server8中的httpd:
在瀏覽器中打開172.25.85.100,交替出現
server7.linux.org 和 server8.westos.org
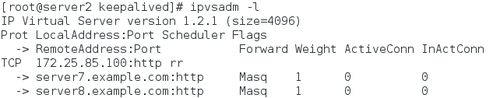
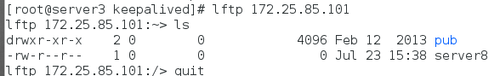
在server2中:ipvsadm -l
關閉server2中的keepalived,在server3上,ipvsadm -l
圖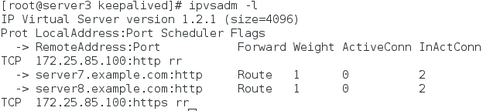
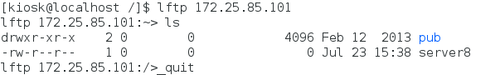
4.在serve7/8上安裝:
yum install vsftpd -y
/etc/init.d/vsftpd start
server7:
cd /var/ftp
touch server7
ip addr add 172.25.85.101/32 dev eth1
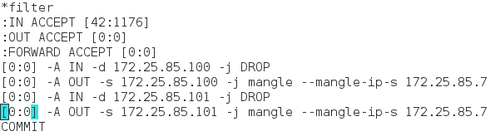
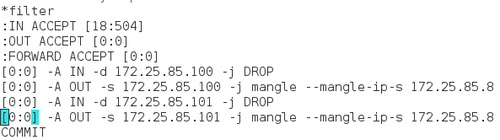
vim /etc/sysconfig/arptables
[0:0] -A IN -d 172.25.85.100 -j DROP [0:0] -A OUT -s 172.25.85.100 -j mangle --mangle-ip-s 172.25.85.7 [0:0] -A IN -d 172.25.85.101 -j DROP [0:0] -A OUT -s 172.25.85.101 -j mangle --mangle-ip-s 172.25.85.7 COMMIT
/etc/init.d/arptables_jf restart
server8:
cd /var/ftp
ip addr add 172.25.85.101/32 dev eth1 touch server8
vim /etc/sysconfig/arptables
[0:0] -A IN -d 172.25.85.100 -j DROP [0:0] -A OUT -s 172.25.85.100 -j mangle --mangle-ip-s 172.25.85.8 [0:0] -A IN -d 172.25.85.101 -j DROP [0:0] -A OUT -s 172.25.85.101 -j mangle --mangle-ip-s 172.25.85.8 COMMIT
/etc/init.d/arptables_jf restart
server2:
vim /etc/keepalived/keepalived.conf
##添加一個虛擬ip 172.25.85.101
再添加以下內容
vrrp_instance VI_1 {
state MASTER
interface eth1
virtual_router_id 51
priority 100
advert_int 1
authentication {
auth_type PASS
auth_pass 1111
}
virtual_ipaddress {
172.25.85.100
172.25.85.101
}
}
virtual_server 172.25.85.101 21 {
delay_loop 6
lb_algo wlc
lb_kind DR
persistence_timeout 60
protocol TCP
real_server 172.25.85.7 21 {
weight 1
TCP_CHECK {
connect_timeout 3
nb_get_retry 3
delay_before_retry 3
}
}
real_server 172.25.85.8 21 {
weight 1
TCP_CHECK {
connect_timeout 3
nb_get_retry 3
delay_before_retry 3
}
}
}
/etc/init.d/keepalived restart
scp keepalived.conf [email protected]:/etc/keepalived/
server3:
vim /etc/keepalived/keepalived.conf
修改優先級爲50,並修改state 爲BACKUP
/etc/init.d/keepalived restart
找一個不同於172.25.85.*網段的ip進行檢測:
真機ip是172.25.254.85
在server3上:
fullnat模式就是完全NAT,fullnat模式需要編譯內核。
server3.example.com 172.25.85.3
編譯內核:
1.在server3上:
rpm -ivh kernel-2.6.32-220.23.1.el6.src.rpm
cd rpmbuild/SPECS
yum install rpm-build -y
rpmbuild -bp kernel.spec
yum install gcc redhat-rpm-config patchutils xmlto asciidoc elfutils-libelf-devel zlib-devel binutils-devel newt-devel python-devel perl-ExtUtils-Embed -y
rpmbuild -bp kernel.spec
yum install asciidoc-8.4.5-4.1.el6.noarch.rpm
slang-devel-2.2.1-1.el6.x86_64.rpm
newt-devel-0.52.11-3.el6.x86_64.rpm -y
rpmbuild -bp kernel.spec ##時間較長
另外打開一個終端:server3:
yum provides */rngd
yum install rng-tools -y
rngd -r /dev/urandom ## rpmbuild -bp kernel.spec 立刻結束
cd /root/rpmbuild/BUILD/kernel-2.6.32-220.23.1.el6
cd /root/rpmbuild/BUILD/kernel-2.6.32-220.23.1.el6
tar Lvs-fullnat-synproxy.tar.gz
cd vs-fullnat-synproxy
cp lvs-2.6.32-220.23.1.el6.patch ../linux-2.6.32-220.23.1.el6.x86_64/
cd ../linux-2.6.32-220.23.1.el6.x86_64
##目錄爲/root/rpmbuild/BUILD/kernel-2.6.32-220.23.1.el6/linux-2.6.32-220.23.1.el6.x86_64
yum install patch -y
patch -p1 < lvs-2.6.32-220.23.1.el6.patch ##
vim Makefile
EXTRAVERSION=-220.23.1.el6
先給server3分配20G的虛擬硬盤,並進行拉伸
make -j2
make modules_install
make install
重啓主機。檢查內核是不是最新安裝的內核。
2.在server3:
cd /root/rpmbuild/BUILD/kernel-2.6.32-220.23.1.el6/lvs-fullnat-synproxy
cp lvs-tools.tar.gz /root
tar zxf lvs-tools.tar.gz
cd /root/tools/keepalived
yum install openssl-devel popt-devel
./configure --with-kernel-dir="/lib/modules/`uname -r`/build" ##編譯成功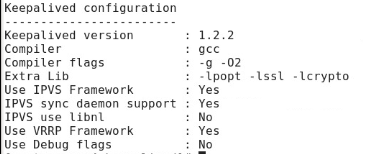
make
make install
which keepalived ##/usr/local/sbin/keepalived
yum install ipvsadm -y
ipvsadm -l
cd /root/tools/ipvsadm
make
make install