kubeadm是Kubernetes官方提供的用於快速安裝 Kubernetes 集羣的工具,通過將集羣的各個組件進行容器化安裝管理,通過kubeadm的方式安裝集羣比二進制的方式安裝要方便不少,但是目錄kubeadm還處於beta狀態,還不能用於生產環境,Using kubeadm to Create a Cluster文檔中已經說明kubeadm將會很快能夠用於生產環境了。
所以現在來了解下kubeadm的使用方式的話還是很有必要的,對於現階段想要用於生產環境的,建議還是參考我們前面的文章:手動搭建高可用的kubernetes 集羣或者視頻教程。
環境
我們這裏準備兩臺Centos7的主機用於安裝,後續節點可以根究需要添加即可:
$ cat /etc/hosts10.151.30.57 ydzs-master110.151.30.62 evjfaxic
禁用防火牆:
$ systemctl stop firewalld$ systemctl disable firewalld
禁用SELINUX:
$ setenforce 0$ cat /etc/selinux/configSELINUX=disabled
創建/etc/sysctl.d/k8s.conf文件,添加如下內容:
net.bridge.bridge-nf-call-ip6tables = 1net.bridge.bridge-nf-call-iptables = 1net.ipv4.ip_forward = 1
執行如下命令使修改生效:
$ modprobe br_netfilter$ sysctl -p /etc/sysctl.d/k8s.conf
鏡像
如果你的節點上面有科學上網的工具,可以忽略這一步,我們需要提前將所需的gcr.io上面的鏡像下載到節點上面,當然前提條件是你已經成功安裝了docker。
master節點,執行下面的命令:
docker pull cnych/kube-apiserver-amd64:v1.10.0docker pull cnych/kube-scheduler-amd64:v1.10.0docker pull cnych/kube-controller-manager-amd64:v1.10.0docker pull cnych/kube-proxy-amd64:v1.10.0docker pull cnych/k8s-dns-kube-dns-amd64:1.14.8docker pull cnych/k8s-dns-dnsmasq-nanny-amd64:1.14.8docker pull cnych/k8s-dns-sidecar-amd64:1.14.8docker pull cnych/etcd-amd64:3.1.12docker pull cnych/flannel:v0.10.0-amd64 docker pull cnych/pause-amd64:3.1docker tag cnych/kube-apiserver-amd64:v1.10.0 k8s.gcr.io/kube-apiserver-amd64:v1.10.0docker tag cnych/kube-scheduler-amd64:v1.10.0 k8s.gcr.io/kube-scheduler-amd64:v1.10.0docker tag cnych/kube-controller-manager-amd64:v1.10.0 k8s.gcr.io/kube-controller-manager-amd64:v1.10.0docker tag cnych/kube-proxy-amd64:v1.10.0 k8s.gcr.io/kube-proxy-amd64:v1.10.0docker tag cnych/k8s-dns-kube-dns-amd64:1.14.8 k8s.gcr.io/k8s-dns-kube-dns-amd64:1.14.8docker tag cnych/k8s-dns-dnsmasq-nanny-amd64:1.14.8 k8s.gcr.io/k8s-dns-dnsmasq-nanny-amd64:1.14.8docker tag cnych/k8s-dns-sidecar-amd64:1.14.8 k8s.gcr.io/k8s-dns-sidecar-amd64:1.14.8docker tag cnych/etcd-amd64:3.1.12 k8s.gcr.io/etcd-amd64:3.1.12docker tag cnych/flannel:v0.10.0-amd64 quay.io/coreos/flannel:v0.10.0-amd64 docker tag cnych/pause-amd64:3.1 k8s.gcr.io/pause-amd64:3.1
可以將上面的命令保存爲一個shell腳本,然後直接執行即可。這些鏡像是在master節點上需要使用到的鏡像,一定要提前下載下來。
其他Node,執行下面的命令:
docker pull cnych/kube-proxy-amd64:v1.10.0docker pull cnych/flannel:v0.10.0-amd64 docker pull cnych/pause-amd64:3.1docker pull cnych/kubernetes-dashboard-amd64:v1.8.3docker pull cnych/heapster-influxdb-amd64:v1.3.3docker pull cnych/heapster-grafana-amd64:v4.4.3docker pull cnych/heapster-amd64:v1.4.2docker tag cnych/flannel:v0.10.0-amd64 quay.io/coreos/flannel:v0.10.0-amd64 docker tag cnych/pause-amd64:3.1 k8s.gcr.io/pause-amd64:3.1docker tag cnych/kube-proxy-amd64:v1.10.0 k8s.gcr.io/kube-proxy-amd64:v1.10.0docker tag cnych/kubernetes-dashboard-amd64:v1.8.3 k8s.gcr.io/kubernetes-dashboard-amd64:v1.8.3docker tag cnych/heapster-influxdb-amd64:v1.3.3 k8s.gcr.io/heapster-influxdb-amd64:v1.3.3docker tag cnych/heapster-grafana-amd64:v4.4.3 k8s.gcr.io/heapster-grafana-amd64:v4.4.3docker tag cnych/heapster-amd64:v1.4.2 k8s.gcr.io/heapster-amd64:v1.4.2
上面的這些鏡像是在Node節點中需要用到的鏡像,在join節點之前也需要先下載到節點上面。
安裝 kubeadm、kubelet、kubectl
在確保docker安裝完成後,上面的相關環境配置也完成了,對應所需要的鏡像(如果可以科學上網可以跳過這一步)也下載完成了,現在我們就可以來安裝kubeadm了,我們這裏是通過指定yum源的方式來進行安裝的:
cat <<EOF > /etc/yum.repos.d/kubernetes.repo [kubernetes] name=Kubernetesbaseurl=https://packages.cloud.google.com/yum/repos/kubernetes-el7-x86_64 enabled=1gpgcheck=1repo_gpgcheck=1gpgkey=https://packages.cloud.google.com/yum/doc/yum-key.gpg https://packages.cloud.google.com/yum/doc/rpm-package-key.gpgEOF
當然了,上面的yum源也是需要科學上網的,如果不能科學上網的話,我們可以使用阿里雲的源進行安裝:
cat <<EOF > /etc/yum.repos.d/kubernetes.repo [kubernetes]name=Kubernetesbaseurl=http://mirrors.aliyun.com/kubernetes/yum/repos/kubernetes-el7-x86_64enabled=1gpgcheck=0repo_gpgcheck=0gpgkey=http://mirrors.aliyun.com/kubernetes/yum/doc/yum-key.gpg http://mirrors.aliyun.com/kubernetes/yum/doc/rpm-package-key.gpg EOF
目前阿里雲的源最新版本已經是1.10版本,所以可以直接安裝。yum源配置完成後,執行安裝命令即可:
$ yum makecache fast && yum install -y kubelet kubeadm kubectl
正常情況我們可以都能順利安裝完成上面的文件。
配置 kubelet
安裝完成後,我們還需要對kubelet進行配置,因爲用yum源的方式安裝的kubelet生成的配置文件將參數--cgroup-driver改成了systemd,而docker的cgroup-driver是cgroupfs,這二者必須一致才行,我們可以通過docker info命令查看:
$ docker info |grep Cgroup Cgroup Driver: cgroupfs
修改文件kubelet的配置文件/etc/systemd/system/kubelet.service.d/10-kubeadm.conf,將其中的KUBELET_CGROUP_ARGS參數更改成cgroupfs:
Environment="KUBELET_CGROUP_ARGS=--cgroup-driver=cgroupfs"
另外還有一個問題是關於交換分區的,之前我們在手動搭建高可用的kubernetes 集羣一文中已經提到過,Kubernetes從1.8開始要求關閉系統的 Swap ,如果不關閉,默認配置的kubelet將無法啓動,我們可以通過 kubelet 的啓動參數--fail-swap-on=false更改這個限制,所以我們需要在上面的配置文件中增加一項配置(在ExecStart之前):
Environment="KUBELET_EXTRA_ARGS=--fail-swap-on=false"
當然最好的還是將swap給關掉,這樣能提高kubelet的性能。修改完成後,重新加載我們的配置文件即可:
$ systemctl daemon-reload
集羣安裝
初始化
到這裏我們的準備工作就完成了,接下來我們就可以在master節點上用kubeadm命令來初始化我們的集羣了:
$ kubeadm init --kubernetes-version=v1.10.0 --pod-network-cidr=10.244.0.0/16 --apiserver-advertise-address=10.151.30.57
命令非常簡單,就是kubeadm init,後面的參數是需要安裝的集羣版本,因爲我們這裏選擇flannel作爲 Pod 的網絡插件,所以需要指定–pod-network-cidr=10.244.0.0/16,然後是apiserver的通信地址,這裏就是我們master節點的IP 地址。執行上面的命令,如果出現 running with swap on is not supported. Please disable swap之類的錯誤,則我們還需要增加一個參數–ignore-preflight-errors=Swap來忽略swap的錯誤提示信息:
$ kubeadm init \ --kubernetes-version=v1.10.0 \ --pod-network-cidr=10.244.0.0/16 \ --apiserver-advertise-address=10.151.30.57 \ --ignore-preflight-errors=Swap [init] Using Kubernetes version: v1.10.0 [init] Using Authorization modes: [Node RBAC] [preflight] Running pre-flight checks. [WARNING FileExisting-crictl]: crictl not found in system pathSuggestion: go get github.com/kubernetes-incubator/cri-tools/cmd/crictl [preflight] Starting the kubelet service [certificates] Generated ca certificate and key. [certificates] Generated apiserver certificate and key. [certificates] apiserver serving cert is signed for DNS names [ydzs-master1 kubernetes kubernetes.default kubernetes.default.svc kubernetes.default.svc.cluster.local] and IPs [10.96.0.1 10.151.30.57] [certificates] Generated apiserver-kubelet-client certificate and key. [certificates] Generated etcd/ca certificate and key. [certificates] Generated etcd/server certificate and key. [certificates] etcd/server serving cert is signed for DNS names [localhost] and IPs [127.0.0.1] [certificates] Generated etcd/peer certificate and key. [certificates] etcd/peer serving cert is signed for DNS names [ydzs-master1] and IPs [10.151.30.57] [certificates] Generated etcd/healthcheck-client certificate and key. [certificates] Generated apiserver-etcd-client certificate and key. [certificates] Generated sa key and public key. [certificates] Generated front-proxy-ca certificate and key. [certificates] Generated front-proxy-client certificate and key. [certificates] Valid certificates and keys now exist in "/etc/kubernetes/pki"[kubeconfig] Wrote KubeConfig file to disk: "/etc/kubernetes/admin.conf"[kubeconfig] Wrote KubeConfig file to disk: "/etc/kubernetes/kubelet.conf"[kubeconfig] Wrote KubeConfig file to disk: "/etc/kubernetes/controller-manager.conf"[kubeconfig] Wrote KubeConfig file to disk: "/etc/kubernetes/scheduler.conf"[controlplane] Wrote Static Pod manifest for component kube-apiserver to "/etc/kubernetes/manifests/kube-apiserver.yaml"[controlplane] Wrote Static Pod manifest for component kube-controller-manager to "/etc/kubernetes/manifests/kube-controller-manager.yaml"[controlplane] Wrote Static Pod manifest for component kube-scheduler to "/etc/kubernetes/manifests/kube-scheduler.yaml"[etcd] Wrote Static Pod manifest for a local etcd instance to "/etc/kubernetes/manifests/etcd.yaml"[init] Waiting for the kubelet to boot up the control plane as Static Pods from directory "/etc/kubernetes/manifests". [init] This might take a minute or longer if the control plane images have to be pulled. [apiclient] All control plane components are healthy after 22.007661 seconds [uploadconfig] Storing the configuration used in ConfigMap "kubeadm-config" in the "kube-system" Namespace [markmaster] Will mark node ydzs-master1 as master by adding a label and a taint [markmaster] Master ydzs-master1 tainted and labelled with key/value: node-role.kubernetes.io/master=""[bootstraptoken] Using token: 8xomlq.0cdf2pbvjs2gjho3 [bootstraptoken] Configured RBAC rules to allow Node Bootstrap tokens to post CSRs in order for nodes to get long term certificate credentials [bootstraptoken] Configured RBAC rules to allow the csrapprover controller automatically approve CSRs from a Node Bootstrap Token [bootstraptoken] Configured RBAC rules to allow certificate rotation for all node client certificates in the cluster [bootstraptoken] Creating the "cluster-info" ConfigMap in the "kube-public" namespace [addons] Applied essential addon: kube-dns [addons] Applied essential addon: kube-proxy Your Kubernetes master has initialized successfully! To start using your cluster, you need to run the following as a regular user: mkdir -p $HOME/.kube sudo cp -i /etc/kubernetes/admin.conf $HOME/.kube/config sudo chown $(id -u):$(id -g) $HOME/.kube/config You should now deploy a pod network to the cluster. Run "kubectl apply -f [podnetwork].yaml" with one of the options listed at: https://kubernetes.io/docs/concepts/cluster-administration/addons/You can now join any number of machines by running the following on each node as root: kubeadm join 10.151.30.57:6443 --token 8xomlq.0cdf2pbvjs2gjho3 --discovery-token-ca-cert-hash sha256:92802317cb393682c1d1356c15e8b4ec8af2b8e5143ffd04d8be4eafb5fae368
上面的信息記錄了kubeadm初始化整個集羣的過程,生成相關的各種證書、kubeconfig文件、bootstraptoken等等,後邊是使用kubeadm join往集羣中添加節點時用到的命令,下面的命令是配置如何使用kubectl訪問集羣的方式: mkdir -p $HOME/.kube sudo cp -i /etc/kubernetes/admin.conf $HOME/.kube/config sudo chown $(id -u):$(id -g) $HOME/.kube/config 最後給出了將節點加入集羣的命令:
kubeadm join 10.151.30.57:6443 --token 8xomlq.0cdf2pbvjs2gjho3 --discovery-token-ca-cert-hash sha256:92802317cb393682c1d1356c15e8b4ec8af2b8e5143ffd04d8be4eafb5fae368
我們根據上面的提示配置好kubectl後,就可以使用kubectl來查看集羣的信息了:
$ kubectl get cs
NAME STATUS MESSAGE ERROR
scheduler Healthy ok
controller-manager Healthy ok
etcd-0 Healthy {"health": "true"}
$ kubectl get csr
NAME AGE REQUESTOR CONDITION
node-csr-8qygb8Hjxj-byhbRHawropk81LHNPqZCTePeWoZs3-g 1h system:bootstrap:8xomlq Approved,Issued
$ kubectl get nodes
NAME STATUS ROLES AGE VERSION
ydzs-master1 Ready master 3h v1.10.0如果你的集羣安裝過程中遇到了其他問題,我們可以使用下面的命令來進行重置:
$ kubeadm reset$ ifconfig cni0 down && ip link delete cni0$ ifconfig flannel.1 down && ip link delete flannel.1$ rm -rf /var/lib/cni/
安裝 Pod Network
接下來我們來安裝flannel網絡插件,很簡單,和安裝普通的POD沒什麼兩樣:
$ wget https://raw.githubusercontent.com/coreos/flannel/master/Documentation/kube-flannel.yml$ kubectl apply -f kube-flannel.yml clusterrole.rbac.authorization.k8s.io "flannel" created clusterrolebinding.rbac.authorization.k8s.io "flannel" created serviceaccount "flannel" created configmap "kube-flannel-cfg" created daemonset.extensions "kube-flannel-ds" created
另外需要注意的是如果你的節點有多個網卡的話,需要在kube-flannel.yml中使用--iface參數指定集羣主機內網網卡的名稱,否則可能會出現dns無法解析。flanneld啓動參數加上--iface=<iface-name>
args:- --ip-masq- --kube-subnet-mgr- --iface=eth0
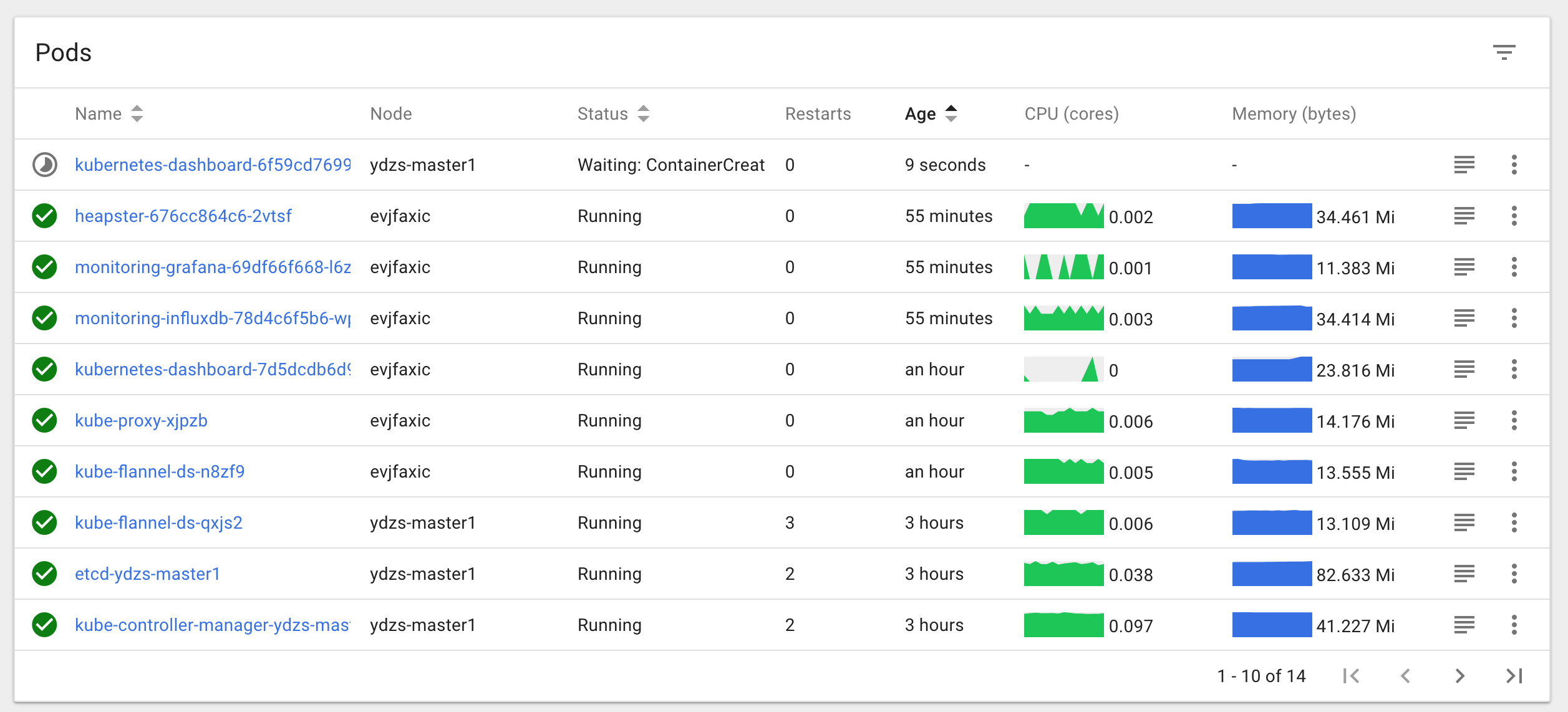
安裝完成後使用kubectl get pods命令可以查看到我們集羣中的組件運行狀態,如果都是Running狀態的話,那麼恭喜你,你的master節點安裝成功了。
$ kubectl get pods --all-namespaces NAMESPACE NAME READY STATUS RESTARTS AGE kube-system etcd-ydzs-master1 1/1 Running 0 10mkube-system kube-apiserver-ydzs-master1 1/1 Running 0 10mkube-system kube-controller-manager-ydzs-master1 1/1 Running 0 10mkube-system kube-dns-86f4d74b45-f5595 3/3 Running 0 10mkube-system kube-flannel-ds-qxjs2 1/1 Running 0 1mkube-system kube-proxy-vf5fg 1/1 Running 0 10mkube-system kube-scheduler-ydzs-master1 1/1 Running 0 10m
kubeadm初始化完成後,默認情況下Pod是不會被調度到master節點上的,所以現在還不能直接測試普通的Pod,需要添加一個工作節點後纔可以。
添加節點
同樣的上面的環境配置、docker 安裝、kubeadmin、kubelet、kubectl 這些都在Node(10.151.30.62)節點安裝配置好過後,我們就可以直接在 Node 節點上執行kubeadm join命令了(上面初始化的時候有),同樣加上參數--ignore-preflight-errors=Swap:
$ kubeadm join 10.151.30.57:6443 --token 8xomlq.0cdf2pbvjs2gjho3 --discovery-token-ca-cert-hash sha256:92802317cb393682c1d1356c15e8b4ec8af2b8e5143ffd04d8be4eafb5fae368 --ignore-preflight-errors=Swap [preflight] Running pre-flight checks. [WARNING Swap]: running with swap on is not supported. Please disable swap [WARNING FileExisting-crictl]: crictl not found in system pathSuggestion: go get github.com/kubernetes-incubator/cri-tools/cmd/crictl [discovery] Trying to connect to API Server "10.151.30.57:6443"[discovery] Created cluster-info discovery client, requesting info from "https://10.151.30.57:6443"[discovery] Requesting info from "https://10.151.30.57:6443" again to validate TLS against the pinned public key [discovery] Cluster info signature and contents are valid and TLS certificate validates against pinned roots, will use API Server "10.151.30.57:6443"[discovery] Successfully established connection with API Server "10.151.30.57:6443"This node has joined the cluster: * Certificate signing request was sent to master and a response was received. * The Kubelet was informed of the new secure connection details. Run 'kubectl get nodes' on the master to see this node join the cluster.
我們可以看到該節點已經加入到集羣中去了,然後我們把master節點的~/.kube/config文件拷貝到當前節點對應的位置即可使用kubectl命令行工具了。
$ kubectl get nodes NAME STATUS ROLES AGE VERSION evjfaxic Ready <none> 1h v1.10.0 ydzs-master1 Ready master 3h v1.10.0
到這裏就算我們的集羣部署成功了,接下來就可以根據我們的需要安裝一些附加的插件,比如 Dashboard、Heapster、Ingress-Controller等等,這些插件的安裝方法就和我們之前手動安裝集羣的方式方法一樣了,這裏就不在重複了,有問題可以在下面留言討論。
參考資料
下面是基於1.9版本手動搭建高可用Kubernetes集羣的視頻教程,對視頻感興趣的同學可以觀看視頻:
掃描下面的二維碼(或微信搜索k8s技術圈)關注我們的微信公衆帳號,在微信公衆帳號中回覆 加羣 即可加入到我們的 kubernetes 討論羣裏面共同學習。
轉自 楊明的博客:https://blog.qikqiak.com/post/use-kubeadm-install-kubernetes-1.10/