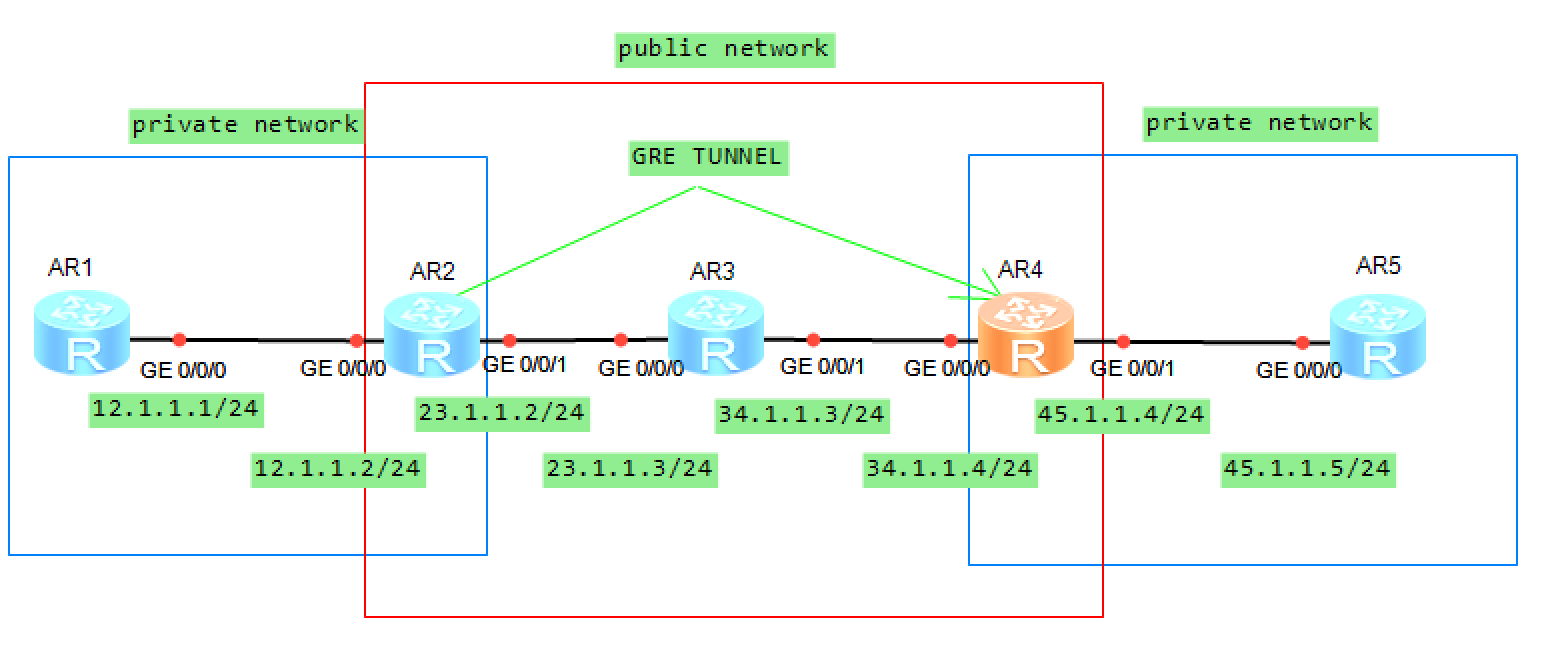
1.先确认网路之间可以通讯
2.在AR2和AR4在配置IKE策略(也可以手动设定)
[AR2]ike proposal 1
[AR2]encryption-algorithm aes-cbc-128
[AR2]authentication-algorithm md5
[AR2]quit
[AR4]ike proposal 1
[AR4]encryption-algorithm aes-cbc-128
[AR4]authentication-algorithm md5
[AR4]quit
display ike proposal3.定义IKE阶段1的参数
[AR2]ike peer test v1
[AR2]ike-proposal 1
[AR2]pre-shared-key simple yeslab
[AR2]remate-address 34.1.1.4
[AR2]local-address 23.1.1.2
[AR2]quit
[AR4]ike peer test v1
[AR4]ike-proposal 1
[AR4]pre-shared-key simple yeslab
[AR4]remate-address 23.1.1.2
[AR4]local-address 34.1.1.2
[AR4]quit
display ike peer name test verbose4.定义感兴趣流
[AR2]acl number 3000
[AR2]rule permit gre source any destination any
[AR4]acl number 3000
[AR4]rule permit gre source any destination any5.IPsec 安全策略
[AR2]ipsec proposal trans1
[AR2]encapsulation-mode tunnel
[AR2]transform esp
[AR2]esp encryption-algorithm des
[AR2]esp authentication-algorithm sha1
[AR4]ipsec proposal trans1
[AR4]encapsulation-mode tunnel
[AR4]transform esp
[AR4]esp encryption-algorithm des
[AR4]esp authentication-algorithm sha1
display ipsec proposal6.关联上述策略
[AR2]ipsec policy r2-r4
[AR2]ike-peer test
[AR2]proposal trans1
[AR2]security acl 3000
[AR4]ipsec policy r4-r2
[AR4]ike-peer test
[AR4]proposal trans1
[AR4]security acl 30007.在接口上套用策略
[AR2]int g0/0/1
[AR2]ipsec policy r2-r4
[AR4]int g0/0/0
[AR4]ipsec policy r4-r2
display ipsec sa