openssl的配置文件:/etc/pki/tls/openssl.cnf
三種策略:匹配、支持和可選。匹配:指要求申請填寫的信息跟CA設置信息必須一致;支持:指必須填寫這項申請信息;可選:指可有可無。
實驗環境:需要兩臺主機,我這裏用主機A(Centos6:ip爲172.17.250.83)創建CA並給其他主機提供CA服務;主機B(Centos7:ip爲172.17.253.204)爲httpd服務器,用來申請證書。
1、首先看一下配置文件的部分內容,其中以下內容在創建CA時是必須要寫的:
dir = /etc/pki/CA # Where everything is kept certs = $dir/certs # Where the issued certs are kept crl_dir = $dir/crl # Where the issued crl are kept database = $dir/index.txt # database index file. #unique_subject = no # Set to 'no' to allow creation of # several ctificates with same subject. new_certs_dir = $dir/newcerts # default place for new certs. certificate = $dir/cacert.pem # The CA certificate serial = $dir/serial # The current serial number crlnumber = $dir/crlnumber # the current crl number # must be commented out to leave a V1 CRL crl = $dir/crl.pem # The current CRL private_key = $dir/private/cakey.pem # The private key
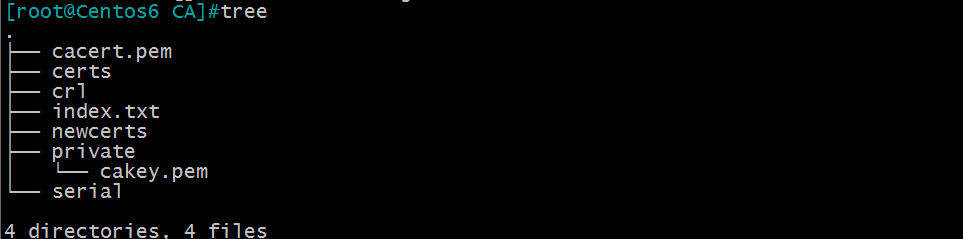
2、根據配置文件的需要創建必須的文件。
[root@Centos6 ~]#touch /etc/pki/CA/index.txt #生成證書索引數據庫的文件 [root@Centos6 ~]#echo 01 > /etc/pki/CA/serial #指定第一個頒發證書的序列號 [root@Centos6 ~]#tree /etc/pki/CA/ /etc/pki/CA/ ├── certs ├── crl ├── index.txt ├── newcerts ├── private └── serial 4 directories, 2 files
注意:創建的這兩個文件,包括接下的實驗裏創建的文件名一定要與配置文件中的文件名一樣。
3、在主機A(Centos6)上創建CA服務,並自簽證書
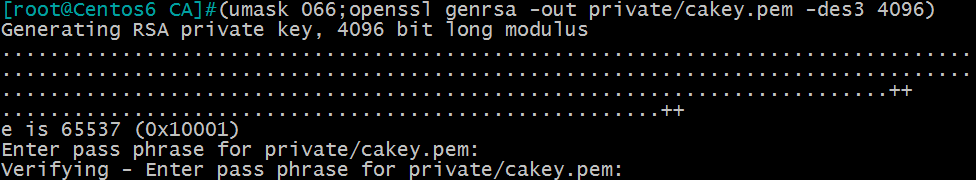
(1)生成私鑰
[root@Centos6 ~]#(umask 066;openssl genrsa -out private/cakey.pem -des3 4096) #-des3是對文件進行加密
注意:用小括號說明是在子shell中執行括號內的命令,不會影響父shell的設置;將umask設置爲066是爲了防止其他人有權限查看和修改生成的私鑰;在4096前還可以給私鑰加上加密算法,比如des3、 rsa等,本例子用了des3加密。
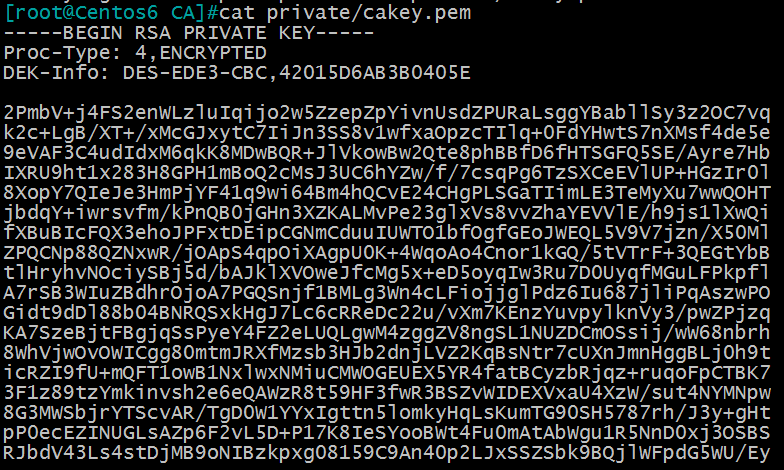
可以看一下加密過後的部分文本:
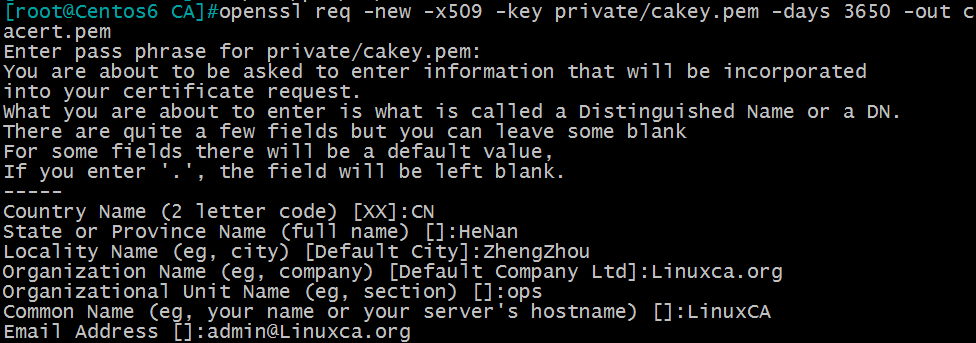
(2)生成自簽證書
[root@Centos6 ~]#openssl req -new -x509 -key private/cakey.pem -days 3650 -out cacert.pem
其中:-new: 生成新證書籤署請求
-x509: 專用於CA生成自簽證書
-key: 生成請求時用到的私鑰文件
-days n:證書的有效期限
-out /PATH/TO/SOMECERTFILE: 證書的保存路徑
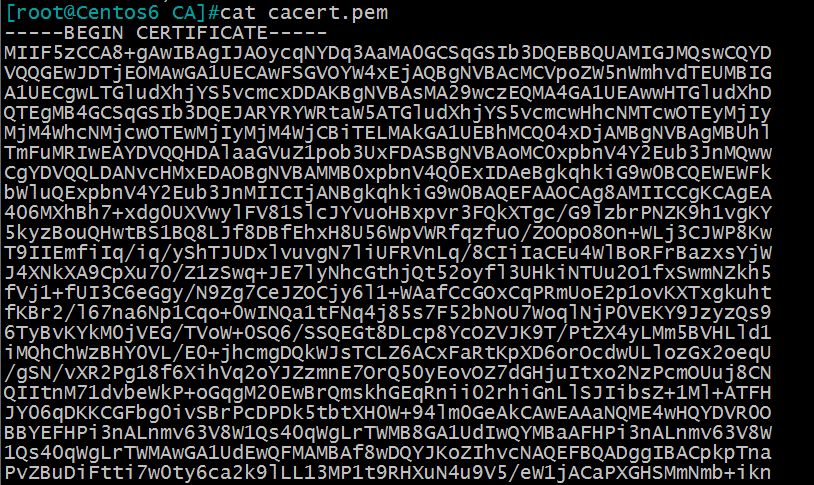
查看一下證書的部分加密文本:
(3)把cacert.pem文件傳輸到windows上,由於在windows上不能識別.pem爲後綴的文本,所以這裏我們要把該文本改成以.cer爲後綴的文本,修改後的文件圖標爲
在windows上打開證書看一下。
4、在需要使用證書的主機B(Centos7)上生成證書請求
(1)給httpd服務生成私鑰
[root@Centos7 ~]#(umask 066;openssl genrsa -out /etc/pki/tls/private/test.key -des3 4096) Generating RSA private key, 4096 bit long modulus ..........................................................++ ...........................................................................................................................................................................................................................++ e is 65537 (0x10001) Enter pass phrase for /etc/pki/tls/private/test.key: Verifying - Enter pass phrase for /etc/pki/tls/private/test.key:
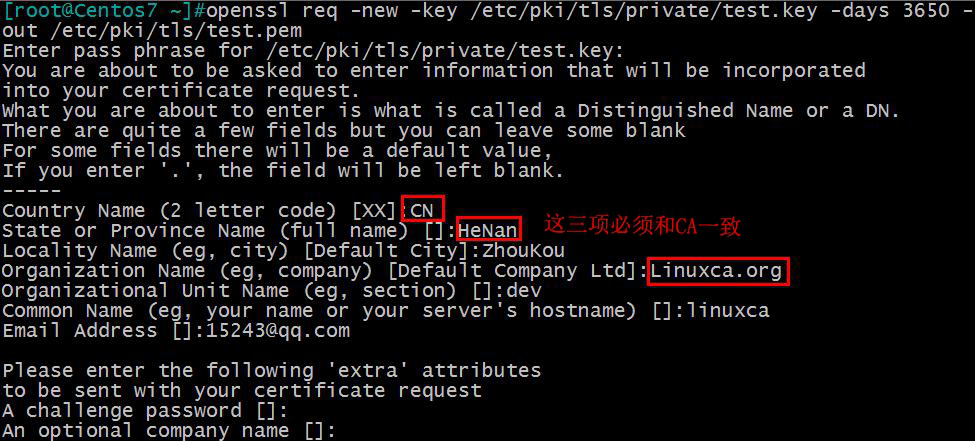
(2)生成證書申請文件
[root@Centos7 ~]#openssl req -new -key /etc/pki/tls/private/test.key -days 3650 -out /etc/pki/tls/test.pem
(3)將證書請求文件傳輸給CA
[root@Centos7 ~]#scp /etc/pki/tls/test.pem @172.17.250.83:/etc/pki/tls/ The authenticity of host '172.17.250.83 (172.17.250.83)' can't be established. RSA key fingerprint is 09:52:06:53:a1:13:99:f3:b9:5c:5f:0a:c4:b6:1c:ed. Are you sure you want to continue connecting (yes/no)? yes Warning: Permanently added '172.17.250.83' (RSA) to the list of known hosts. [email protected]'s password: test.pem 100% 1736 1.7KB/s 00:00
5、在主機A(Centos6)上籤署證書,並頒發給證書申請者(主機B)
(1)簽署證書
[root@Centos6 ~]#openssl ca -in /etc/pki/tls/test.pem -out /etc/pki/CA/certs/test.crt -days 3650 Using configuration from /etc/pki/tls/openssl.cnf Enter pass phrase for /etc/pki/CA/private/cakey.pem: Check that the request matches the signature Signature ok Certificate Details: Serial Number: 1 (0x1) Validity Not Before: Sep 12 23:04:23 2017 GMT Not After : Sep 10 23:04:23 2027 GMT Subject: countryName = CN stateOrProvinceName = HeNan organizationName = Linuxca.org organizationalUnitName = dev commonName = linuxca emailAddress = [email protected] X509v3 extensions: X509v3 Basic Constraints: CA:FALSE Netscape Comment: OpenSSL Generated Certificate X509v3 Subject Key Identifier: 97:B6:0A:0A:70:C6:FB:29:BB:B9:4A:26:98:3E:73:8B:20:F4:37:5E X509v3 Authority Key Identifier: keyid:73:E2:DE:70:0B:9E:6B:FA:DD:5F:16:D5:0B:38:D2:A5:A0:2E:B4:D6 Certificate is to be certified until Sep 10 23:04:23 2027 GMT (3650 days) Sign the certificate? [y/n]:y 1 out of 1 certificate requests certified, commit? [y/n]y Write out database with 1 new entries Data Base Updated
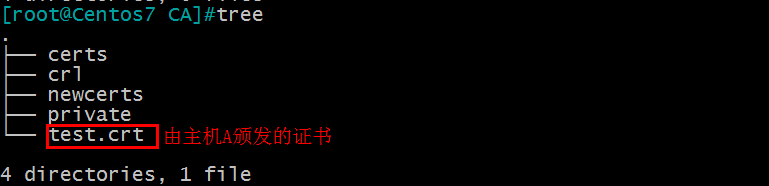
(2)把證書頒發給主機B(Centos7)
[root@Centos6 CA]#scp certs/test.crt @172.17.253.204:/etc/pki/CA/ The authenticity of host '172.17.253.204 (172.17.253.204)' can't be established. RSA key fingerprint is 91:d3:76:ba:60:12:0d:13:9b:93:6a:39:71:18:fe:65. Are you sure you want to continue connecting (yes/no)? yes Warning: Permanently added '172.17.253.204' (RSA) to the list of known hosts. [email protected]'s password: test.crt 100% 7311 7.1KB/s 00:00
(3)在主機B(Centos7)上查看證書中的信息,
openssl x509 -in /PATH/FROM/CERT_FILE
-text|issuer|subject|serial|dates
opensslca -status SERIAL查看指定編號的證書狀態
[root@Centos7 CA]#openssl x509 -in test.crt -text
至此,CA的創建和申請、頒發就完成了。