一. 加密算法,協議:
對稱加密,公鑰加密,單向加密,認證協議
1.)對稱加密:使用同一個密鑰對數據進行加密,解密。對稱加密速度比較快。
常用的對稱加密有:DES、IDEA、RC2、RC4、SKIPJACK、RC5、AES等。
2.)公鑰加密:生成兩個密鑰,公開的密鑰爲公鑰,不公開的密鑰爲私鑰。解密數據時需要使用私鑰解密。
常用加密算法:RSA, DSA,EIGamal等。
3.)單向加密:加密數據定長輸出,不可逆解密。數據變動一點就會導致整個數據損壞。
常見加密算法:MD5,SHA1,SHA256,SHA384,SHA512等。
使用加密計算功能:數據保密性,數據完整性,身份驗證。
二. 加密算法通信:
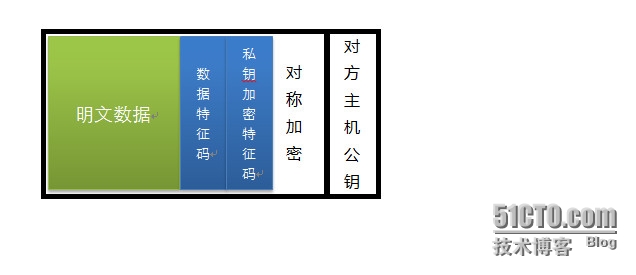
1.)兩個主機之間進行通信,發送方首先使用單向加密,獲取數據特徵碼,以保證數據的完整性。使用私鑰加密特徵碼,生成一次性對稱密鑰,保證數據保密性。使用某種加密算法,對整個數據加密,包含特徵碼,私鑰加密特徵碼,驗證發送者身份。最後用對方主機公鑰加密,保證所有數據完整性,保密性。
2.)接收方使用私鑰解密公鑰,得到對稱加密密鑰,使用對方公鑰解密私鑰加密特徵碼,然後用單向加密獲取數據特徵碼,最後驗證數據完整性。
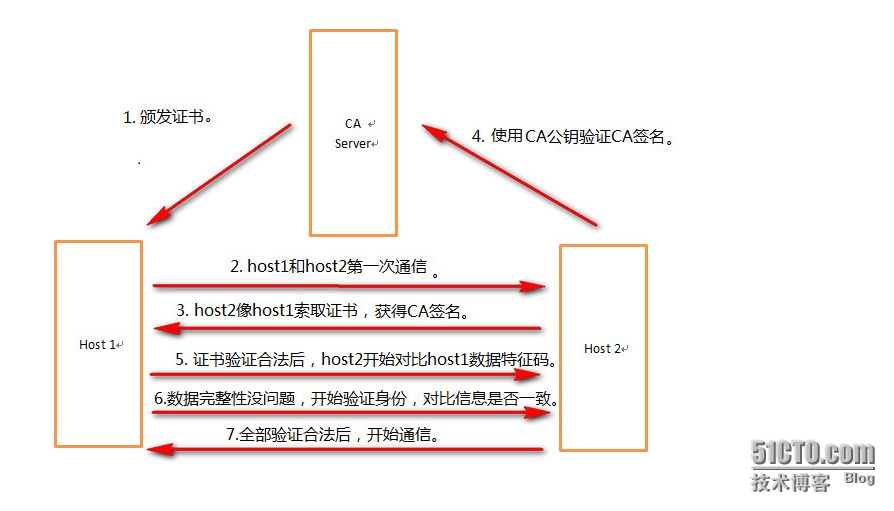
然後通過CA驗證。
CA理解:
三.升級OpenSSL
1.)首先升級OpenSSL,由於CentOS6.5上默認安裝的版本是openssl-1.0.1e-15.el6。
去官網下載最新版本,openssl-1.0.1h.tar.gz。
2.)解壓安裝:
# tar -zxf openssl-1.0.1h.tar.gz -C/usr/local/ # cd /usr/local/openssl-1.0.1h/ # ./config shared zlib # make;make install
以上方法安裝的會在/usr/local下生成一個ssl目錄。
3.)開始替換版本,把老版本的文件和命令修改名字,或者刪除。
# mv/usr/bin/openssl /usr/bin/openssl.old.bak # mv/usr/include/openssl/ /usr/include/openssl.old.bak # ln -s/usr/local/ssl/bin/openssl /usr/bin/openssl # ln -s/usr/local/ssl/include/openssl/ /usr/include/openssl/ ln: target`/usr/include/openssl/' is not a directory: No such file or directory #不要加/ # ln -s/usr/local/ssl/include/openssl/ /usr/include/openssl
4.)修改lib搜索路徑,綁定。
#echo "/usr/local/ssl/lib" >>/etc/ld.so.conf #ldconfig
5.)查看版本是否更新:
#openssl version -a OpenSSL1.0.1h 5 Jun 2014 builton: Fri Aug 1 15:40:43 CST 2014 platform:linux-x86_64 …… OPENSSLDIR:"/usr/local/ssl"
四.OpenSSL建立CA:
CA路徑可以隨便建立,但是要修改配置文件中的dir和路徑一致,然後還要創建certs crl index.txt newcerts private serial
1.)修改openssl.cnf配置文件
# vimopenssl.cnf dir = /usr/local/ssl/demoCA # Where everything is kept #ls bin CA certs demoCA include lib man misc openssl.cnf private
2.)生成密鑰
#cd demoCA/ #(umask 077;openssl genrsa -out private/cakey.pem 2048) GeneratingRSA private key, 2048 bit long modulus ................................................................+++ ..................................+++ eis 65537 (0x10001)
3.)自簽證書
命令選項: req: 生成證書籤署請求 -news: 新請求 -key/path/to/keyfile: 指定私鑰文件 -out/path/to/somefile: -x509: 生成自簽署證書 -days n: 有效天數 #openssl req -new -x509 -key private/cakey.pem -out/usr/local/ssl/demoCA/cacert.pem -days 365 Youare about to be asked to enter information that will be incorporated intoyour certificate request. Whatyou are about to enter is what is called a Distinguished Name or a DN. Thereare quite a few fields but you can leave some blank Forsome fields there will be a default value, Ifyou enter '.', the field will be left blank. ----- CountryName (2 letter code) [AU]:CN #國家 Stateor Province Name (full name) [Some-State]:Henan #地區 LocalityName (eg, city) []:ZZ # OrganizationName (eg, company) [Internet Widgits Pty Ltd]:text #公司 OrganizationalUnit Name (eg, section) []:mon #部門 CommonName (e.g. server FQDN or YOUR name) []:Mac #主機名 EmailAddress []: #郵箱 #ls cacert.pem certs crl index.txt newcerts private serial #cat serial 01
4.)節點申請證書:
生成密鑰對
# mkdir /usr/local/ssl # cd /usr.local/ssl #(umask 077; openssl genrsa -out /usr/local/ssl/test.key 2048) GeneratingRSA private key, 2048 bit long modulus ....+++ ....+++ eis 65537 (0x10001) #ls test.key
生成證書籤署請求
#openssl req -new -key /usr/local/ssl/test.key -out /usr/local/ssl/test.csr Youare about to be asked to enter information that will be incorporated intoyour certificate request. Whatyou are about to enter is what is called a Distinguished Name or a DN. Thereare quite a few fields but you can leave some blank Forsome fields there will be a default value, Ifyou enter '.', the field will be left blank. ----- 此部分要與CA服務器填寫一致 CountryName (2 letter code) [XX]:CN Stateor Province Name (full name) []:Henan LocalityName (eg, city) [Default City]:ZZ OrganizationName (eg, company) [Default Company Ltd]:text OrganizationalUnit Name (eg, section) []:mon CommonName (eg, your name or your server's hostname) []:Mac EmailAddress []: Pleaseenter the following 'extra' attributes tobe sent with your certificate request Achallenge password []: #密碼部分可以直接回車 Anoptional company name []: #ls test.csr test.key
5.)CA簽署證書;
將簽署請求發送給CA服務器,我這邊是在CA服務器遠程複製到本地
#scp 172.16.26.27:/usr/local/ssl/test.csr ./
由於在本地實驗過一次簽署證書,再次簽署的時候報錯。
Openssl無法同時建立兩個crt。
數據庫更新錯誤
#openssl ca -in /usr/local/ssl/demoCA/client-crt/test.csr -out/usr/local/ssl/demoCA/client-crt/test.crt -days 356 Usingconfiguration from /usr/local/ssl/openssl.cnf Checkthat the request matches the signature Signatureok CertificateDetails: Serial Number: 2 (0x2) Validity Not Before: Aug 2 10:12:44 2014 GMT Not After : Jul 24 10:12:44 2015GMT Subject: countryName = CN stateOrProvinceName = Henan organizationName = text organizationalUnitName = mon commonName = Mac X509v3 extensions: X509v3 Basic Constraints: CA:FALSE Netscape Comment: OpenSSL Generated Certificate X509v3 Subject Key Identifier: 38:54:F5:0E:8A:11:FF:83:52:51:5F:8C:54:2E:29:B3:5D:ED:EB:28 X509v3 Authority Key Identifier: keyid:C6:33:EA:CF:E5:29:D3:AA:56:7F:79:21:D1:3D:99:C4:B1:F4:D9:81 Certificateis to be certified until Jul 24 10:12:44 2015 GMT (356 days) Signthe certificate? [y/n]:y failedto update database TXT_DBerror number 2
刪除index.txt索引,然後新touch一個。
#cd ../ #ls cacert.pem certs client-crt crl index.txt index.txt.attr index.txt.old newcerts private serial serial.old #rm -rf index.txt #touch index.txt
重新簽署:
#openssl ca -in /usr/local/ssl/demoCA/client-crt/test.csr -out/usr/local/ssl/demoCA/client-crt/test.crt -days 356 Usingconfiguration from /usr/local/ssl/openssl.cnf Checkthat the request matches the signature Signatureok CertificateDetails: Serial Number: 2 (0x2) Validity Not Before: Aug 2 10:13:54 2014 GMT Not After : Jul 24 10:13:54 2015GMT Subject: countryName = CN stateOrProvinceName = Henan organizationName = text organizationalUnitName = mon commonName = Mac X509v3 extensions: X509v3 Basic Constraints: CA:FALSE Netscape Comment: OpenSSL Generated Certificate X509v3 Subject Key Identifier: 38:54:F5:0E:8A:11:FF:83:52:51:5F:8C:54:2E:29:B3:5D:ED:EB:28 X509v3 Authority Key Identifier: keyid:C6:33:EA:CF:E5:29:D3:AA:56:7F:79:21:D1:3D:99:C4:B1:F4:D9:81 Certificateis to be certified until Jul 24 10:13:54 2015 GMT (356 days) Signthe certificate? [y/n]:y 1out of 1 certificate requests certified, commit? [y/n]y Writeout database with 1 new entries DataBase Updated
這回成功了,將證書發送給請求者。
6.)吊銷證書:
/usr/local/ssl/demoCA/newcerts # openssl ca -revoke 00.pem Using configuration from /usr/local/ssl/openssl.cnf Revoking Certificate 00. Data Base Updated
更新證書吊銷列表
/usr/local/ssl/demoCA/crl #openssl ca -gencrl -out thisca.crl
查看crl文件的內容
# openssl crl -in thisca.crl -noout -text
7.)期間出現了以下問題:Erroropening CA private key ./demoCA/private/cakey.pem
# openssl ca -in /usr/local/client.csr -out /usr/local/client.crt-days 356
Using configuration from /usr/local/ssl/openssl.cnf
Error opening CA private key./demoCA/private/cakey.pem
140486259500712:error:02001002:systemlibrary:fopen:No such file ordirectory:bss_file.c:398:fopen('./demoCA/private/cakey.pem','r')
140486259500712:error:20074002:BIOroutines:FILE_CTRL:system lib:bss_file.c:400:
unable to load CA private key
修改openssl.cnf
[CA_default ] dir = ./ demoCA #修改成要存放密鑰的路徑,而不是升級後默認的路徑。 此路徑是/usr/local/ssl/misc #updatedb locateCA.sh /usr/local/openssl-1.0.1h/apps/CA.sh /usr/local/ssl/misc/CA.sh #locate CA.pl /usr/local/openssl-1.0.1h/apps/CA.pl /usr/local/openssl-1.0.1h/apps/CA.pl.bak /usr/local/openssl-1.0.1h/apps/CA.pl.in /usr/local/openssl-1.0.1h/doc/apps/CA.pl.pod /usr/local/ssl/man/man1/CA.pl.1 /usr/local/ssl/misc/CA.pl #./CA.sh –newca #新建立證書
總結:源碼包升級openssl時,注意修改配置dir路徑,否則會出錯。
生成密鑰時注意權限問題。
申請證書時,所填寫的內容要和CA主機保持一致,不然也會出錯。
開始的時候想要卸載自帶openssl的rpm包,但是發現依賴關係比較複雜。