Keepalived是類似於layer3層,4層,7層交換機制的軟件,作用是檢查WEB服務器健康狀態,根據超時間件來判斷WEB服務器的健康狀態,其中一臺WEB節點出現故障,Keepalived將會把故障的WEB節點移除。故障修復後自動添加回來。
layer3層,4層,7層工作在TCP/IP的協議棧的IP層,TCP層,應用層。
keepalived使用layer3層的方式工作時,keepalived會根據設定時間定期像後端服務器發送一個ICMP的ping包,來檢測web服務器是否在線。
keepalived使用layer4層的方式工作時,是根據TCP的端口來進行檢測,例如web服務器的80端口。
keepalived使用layer7層的方式工作時,就需要檢測的是web節點的httpd或者nginx是否正常運行。
下圖爲根據keepalived畫出簡單的OSI7層模型:
keepalived上面說到是檢查後端服務器健康狀態的,也就是模擬VRRP的工作模式來實現的。
VRRP的特點:VRRP是一種容錯協議,保證當主機的下一跳路由出現故障,由另外一臺路由器代替出現故障的路由器進行工作,而保證網絡通信的連接性及可靠性。
VRRP將局域網內的一組路由器劃分在一起,形成一個VRRP備份組,它在功能上相當於一臺虛擬路由器,使用虛擬路由器號進行標識。以下使用虛擬路由器代替VRRP備份組進行描述。
虛擬路由器有自己的虛擬IP地址和虛擬MAC地址,它的外在表現形式和實際的物理路由器完全一樣。局域網內的主機將虛擬路由器的IP地址設置爲默認網關,通過虛擬路由器與外部網絡進行通信。
準備兩個主機,安裝keepalived。既然是模擬VRRP的工作模式,就需要一個MASTER節點和一個BACKUP節點。
安裝keepalived。
# yum install keepalived
配置MASTER節點的keepalived.conf主配置文件。
! Configuration File forkeepalived
global_defs { #全局定義段
notification_email {
[email protected]
[email protected]
[email protected]
}
[email protected]
smtp_server 192.168.200.1
smtp_connect_timeout 30
router_id LVS_DEVEL
}
vrrp_instance VI_1 { #實例名稱
state MASTER #當前節點爲主節點
interface eth1 #指定網卡
virtual_router_id 132 #虛擬路由ID,默認爲51
priority 100 #優先級,主節點要數字要大於從節點
advert_int 1
authentication {
auth_type PASS
auth_pass 111111
}
virtual_ipaddress { #虛擬IP地址
192.168.0.121
}
}BACKUP節點需要修改下優先級和虛擬路由ID即可。
MASTER節點可以查看下日誌,keepalived是否正常啓動。
# tail -f /var/log/messages Sep 22 02:02:12 webKeepalived_healthcheckers[2734]: Opening file '/etc/keepalived/keepalived.conf'. Sep 22 02:02:12 webKeepalived_healthcheckers[2734]: Configuration is using : 7450 Bytes Sep 22 02:02:12 webKeepalived_vrrp[2735]: VRRP sockpool: [ifindex(3), proto(112), fd(11,12)] Sep 22 02:02:12 webKeepalived_healthcheckers[2734]: Using LinkWatch kernel netlink reflector... Sep 22 02:02:13 webKeepalived_vrrp[2735]: VRRP_Instance(VI_1) Transition to MASTER STATE Sep 22 02:02:14 webKeepalived_vrrp[2735]: VRRP_Instance(VI_1) Entering MASTER STATE Sep 22 02:02:14 webKeepalived_vrrp[2735]: VRRP_Instance(VI_1) setting protocol VIPs. Sep 22 02:02:14 webKeepalived_vrrp[2735]: VRRP_Instance(VI_1) Sending gratuitous ARPs on eth1 for192.168.0.121 Sep 22 02:02:14 webKeepalived_healthcheckers[2734]: Netlink reflector reports IP 192.168.0.121added Sep 22 02:02:19 webKeepalived_vrrp[2735]: VRRP_Instance(VI_1) Sending gratuitous ARPs on eth1 for192.168.0.121
查看指定配置的虛擬IP。
# ip addr show | grep eth1 3: eth1:<BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen1000 inet 192.168.0.110/24 brd 192.168.0.255scope global eth1 inet 192.168.0.121/32 scope global eth1 192.168.0.121已經在這裏了
停止掉keepalived,看看虛擬IP是否還在。
# ip addr show | grep eth1 3: eth1:<BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen1000 inet 192.168.0.110/24 brd 192.168.0.255 scope global eth1
接下來在BACKUP的節點啓動keepalived。
# service keepalived start Starting keepalived: [ OK ] # ip addr show | grep eth1 3: eth1:<BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen1000 inet 192.168.0.111/24 brd 192.168.0.255scope global eth1 inet 192.168.0.121/32 scope global eth1
這時候在MASTER節點啓動keepalived,查看虛擬IP是否回到主節點。
# ip addr show | grep eth1 3: eth1:<BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen1000 inet 192.168.0.110/24 brd 192.168.0.255scope global eth1 inet 192.168.0.121/32 scope global eth1 虛擬IP重新回來了
可以查看下BACKUP節點的日誌。
# tail -f /var/log/messages Sep 22 02:07:10 webKeepalived_vrrp[1904]: VRRP_Instance(VI_1) Transition to MASTER STATE Sep 22 02:07:11 webKeepalived_vrrp[1904]: VRRP_Instance(VI_1) Entering MASTER STATE Sep 22 02:07:11 webKeepalived_vrrp[1904]: VRRP_Instance(VI_1) setting protocol VIPs. Sep 22 02:07:11 webKeepalived_vrrp[1904]: VRRP_Instance(VI_1) Sending gratuitous ARPs on eth1 for192.168.0.121 Sep 22 02:07:11 webKeepalived_healthcheckers[1903]: Netlink reflector reports IP 192.168.0.121added Sep 22 02:07:16 webKeepalived_vrrp[1904]: VRRP_Instance(VI_1) Sending gratuitous ARPs on eth1 for192.168.0.121 Sep 22 02:07:41 webKeepalived_vrrp[1904]: VRRP_Instance(VI_1) Received higher prio advert Sep 22 02:07:41 webKeepalived_vrrp[1904]: VRRP_Instance(VI_1) Entering BACKUP STATE Sep 22 02:07:41 webKeepalived_vrrp[1904]: VRRP_Instance(VI_1) removing protocol VIPs. Sep 22 02:07:41 webKeepalived_healthcheckers[1903]: Netlink reflector reports IP 192.168.0.121removed
重新選舉後,虛擬IP被移除到192.168.0.121,這時候BACKUP節點的虛擬IP就沒有了。
接下來實現Keepalived雙主模式。
兩個keepalived使用兩個虛擬IP,每個節點都使用一個虛擬IP地址,當其中一臺故障的時候,可以直接把虛擬IP地址轉移到另外一臺節點上去,另外一臺正常工作的keepalived將會調度故障那臺後端所管理的WEB主機。
MASTER節點的keepalived.conf添加如下配置。
vrrp_instance VI_2{
state BACKUP
interface eth1
virtual_router_id 232
priority 99
advert_int 1
authentication {
auth_type PASS
auth_pass 222222
}
virtual_ipaddress {
192.168.0.122
}
}定義第二個VRRP實例,修改節點爲BACKUP,優先級爲99,虛擬IP爲192.168.0.122,虛擬路由ID爲232。
而原BACKUOP節點定義修改節點爲MASTER,優先級爲100即可。
兩個節點的keepalived都進行重啓,虛擬IP就會一邊一個。
# ip addr show |grep eth1 3: eth1:<BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen1000 inet 192.168.0.110/24 brd 192.168.0.255scope global eth1 inet 192.168.0.121/32 scope global eth1 # ip addr show |grep eth1 3: eth1:<BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen1000 inet 192.168.0.111/24 brd 192.168.0.255 scopeglobal eth1 inet 192.168.0.122/32 scope global eth1
而當我們把其中一個節點停掉的話,虛擬IP會立即轉移到另外一個節點。
# ip addr show |grep eth1 3: eth1:<BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen1000 link/ether 00:0c:29:b0:80:e9 brdff:ff:ff:ff:ff:ff inet 192.168.0.110/24 brd 192.168.0.255scope global eth1 inet 192.168.0.121/32 scope global eth1 inet 192.168.0.122/32 scope global eth1
這樣即可保證一臺主機出現故障後後端WEB服務器正常被訪問,並且可以解決另外一臺服務器過於空閒。並且需要監控的時候還可以添加郵箱,可以以郵件的方式監控keepalived是否正常工作。
定義監控腳本,檢查web服務運行狀態。
vrrp_scriptchk_httpd { #定義一個名爲chk_httpd的腳本
script "killall -0 httpd" #返回狀態值
interval 1 #檢測間隔時間
weight -5 #權重
fall 2
rise 1
}
vrrp_instance VI_1{
state MASTER
interface eth1
virtual_router_id 132
priority 100
advert_int 1
authentication {
auth_type PASS
auth_pass 111111
}
virtual_ipaddress {
192.168.0.121
}
track_script {
chk_httpd
}
notify_master "/etc/init.d/httpdstart"
notify_backup "/etc/init.d/httpdstop"
notify_fault "/etc/init.d/httpdstop"
}剛安裝好的httpd是沒有啓動的,通過啓動keepalived查看httpd是否同時啓動。
# ss -tnl State Recv-Q Send-Q Local Address:Port Peer Address:Port LISTEN 0 128 :::80 :::* LISTEN 0 128 :::22 :::* LISTEN 0 128 *:22 *:* LISTEN 0 100 ::1:25 :::* LISTEN 0 100 127.0.0.1:25 *:* 端口已經看見了
這時候把MASTER節點的keepalived.conf複製到BACKUP節點,並且修改虛擬路由ID和優先級。
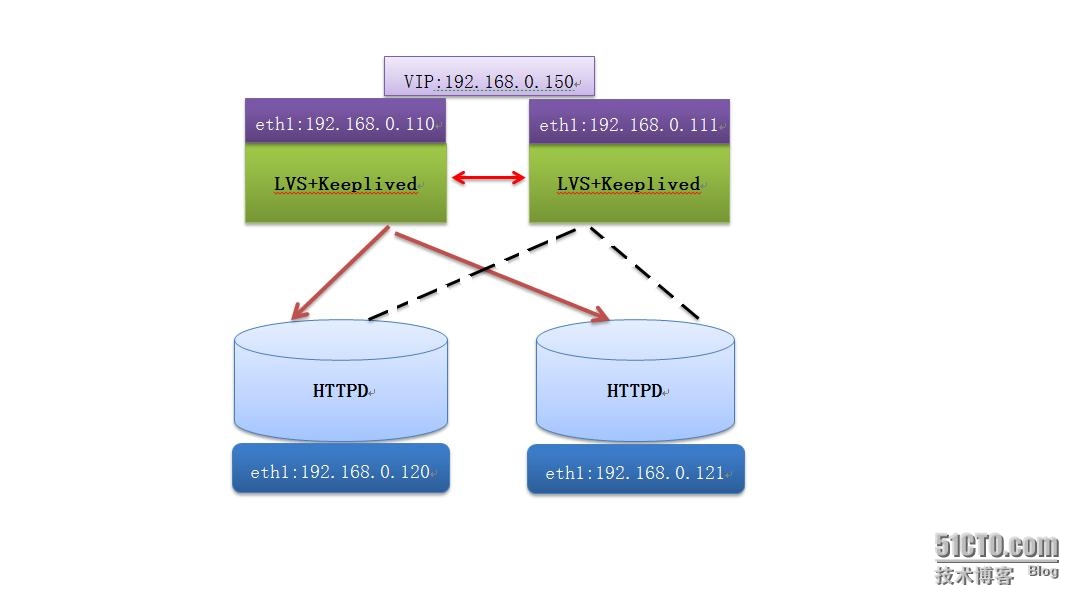
LVS + Keepalived 的實現。
WEB節點的配置:
安裝好httpd服務,配置迴環接口IP地址。
# echo 1 >/proc/sys/net/ipv4/conf/eth1/arp_ignore # echo 1 >/proc/sys/net/ipv4/conf/all/arp_ignore # echo 2 >/proc/sys/net/ipv4/conf/all/arp_announce # echo 2 >/proc/sys/net/ipv4/conf/eth1/arp_announce # ifconfig eth0down # ifconfig lo:0192.168.0.150 netmask 255.255.255.255 broadcast 192.168.0.150 up # ifconfig lo:0 Link encap:Local Loopback inet addr:192.168.0.150 Mask:255.255.255.255 UP LOOPBACK RUNNING MTU:16436 Metric:1 # route add -host192.168.0.150 dev lo:0
另外一臺WEB節點相同配置。
後端服務器準備完畢後,開始配置keepalived。
# vim /etc/keepalived/keepalived.conf
vrrp_instance VI_1{
state MASTER
interface eth1
virtual_router_id 132
priority 100
advert_int 1
authentication {
auth_type PASS
auth_pass 111111
}
virtual_ipaddress {
192.168.0.150
}
}
virtual_server192.168.0.150 80 {
delay_loop 6
lb_algo rr
lb_kind DR
nat_mask 255.255.255.0
protocol TCP
real_server 192.168.0.120 80 {
weight 1
HTTP_GET {
url {
path /
status_code 200
}
connect_timeout 2
nb_get_retry 2
delay_before_retry 1
}
}
real_server 192.168.0.122 80 {
weight 1
HTTP_GET {
url {
path /
status_code 200
}
connect_timeout 2
nb_get_retry 2
delay_before_retry 1
}
}
}訪問測試:
當把主節點的keepalived停掉後,查看虛擬IP是否轉移以及ipvsadm規則。
# ip addr show |grep eth1 3: eth1:<BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen1000 inet 192.168.0.111/24 brd 192.168.0.255scope global eth1 inet 192.168.0.150/32 scope global eth1 # ipvsadm -L -n IP Virtual Serverversion 1.2.1 (size=4096) ProtLocalAddress:Port Scheduler Flags -> RemoteAddress:Port Forward Weight ActiveConn InActConn TCP 192.168.0.150:80 rr -> 192.168.0.120:80 Route 1 0 1 -> 192.168.0.121:80 Route 1 0 1
虛擬IP順利轉移,也可以看到ipvsadm的規則了。
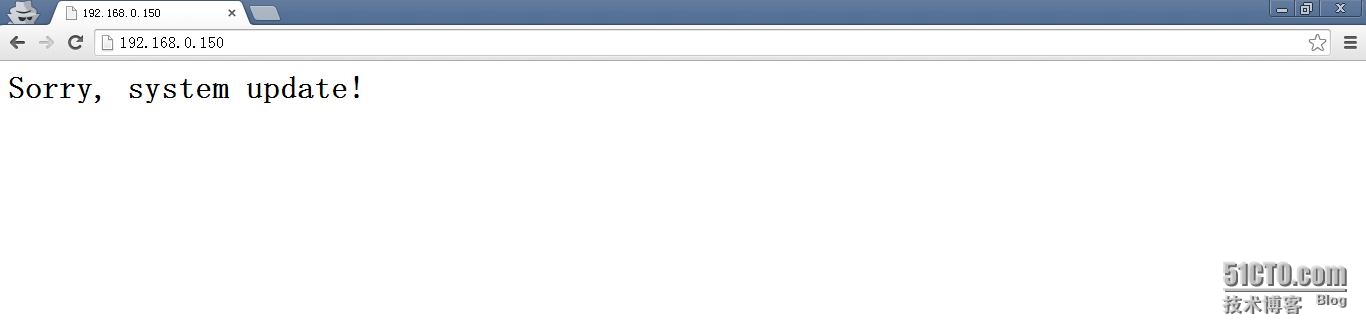
定義一個sorryserver 爲了後端節點全部故障後用來響應的。
在keepalived.conf中添加一條。
sorry_server192.168.0.110 80
下面把WEB服務器的兩個節點全部停掉,測試。
測試完成。