官方提供了三種安裝方式
minikubeMinikube
是一個工具,可以在本地快速運行一個單點的Kubernetes,僅用於嘗試Kubernetes或日常開發的用戶使用。部署地址:https://kubernetes.io/docs/setup/minikube/
kubeadmKubeadm
也是一個工具,提供kubeadm init和kubeadm join,用於快速部署Kubernetes集羣。部署地址:https://kubernetes.io/docs/reference/setup-tools/kubeadm/kubeadm/
二進制包推薦
從官方下載發行版的二進制包,手動部署每個組件,組成Kubernetes集羣。下載地址:https://github.com/kubernetes/kubernetes/releases
我們選擇二進制包安裝
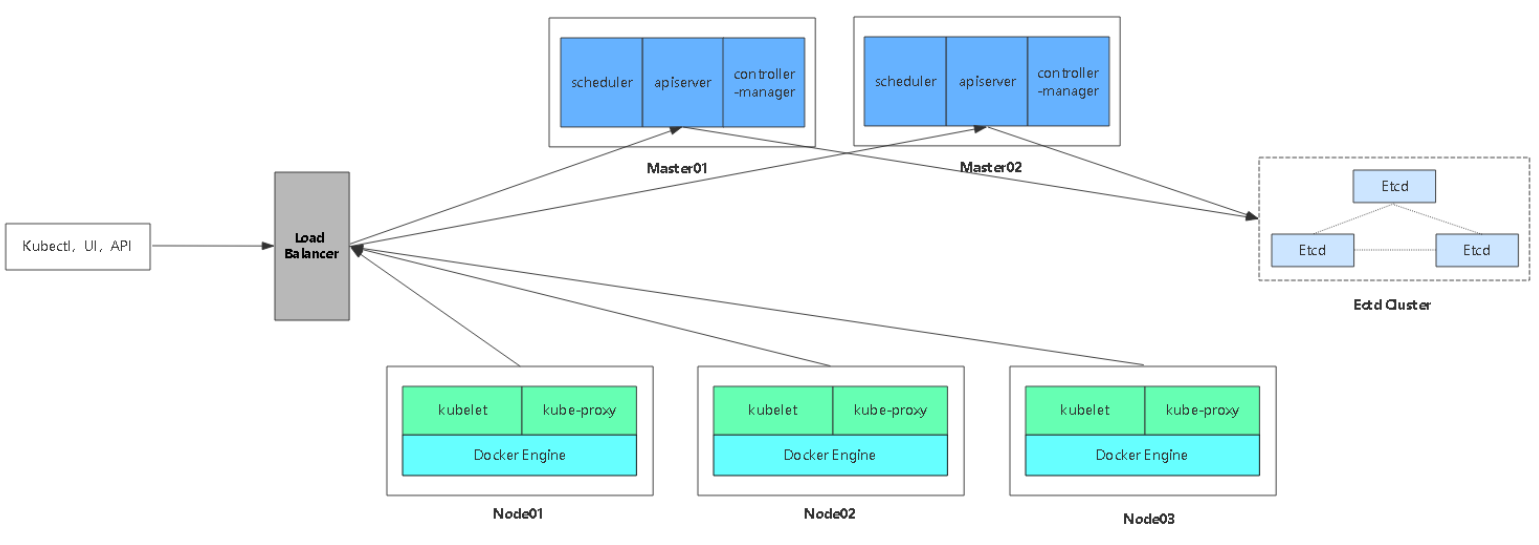
一、規劃服務器
| 主機 | ip | 作用 |
|---|---|---|
| master 01 | 192.168.13.134 | master01節點 |
| master 02 | 192.168.13.135 | master01節點 |
| etcd 01 | 192.168.13.134 | 數據庫01節點 |
| etcd 02 | 192.168.13.135 | 數據庫02節點 |
| etcd 03 | 192.168.13.136 | 數據庫03節點 |
| node01 | 192.168.13.134 | node01節點 |
| node02 | 192.168.13.135 | node02節點 |
| node03 | 192.168.13.136 | node03節點 |
| slb01 | 192.168.13.134 | 負載均衡主節點 |
| slb02 | 192.168.13.135 | 負載均衡備節點 |
生產環境雙master高可用,數據庫最少三臺,奇數增加。node節點最少五個,可以用雲服務器SLB進行負載均衡,也可以使用nginx+keepa高可用。
1.1、部署Etcd集羣
1.1.1、生成Etcd SSL自簽證書
使用cfssl來生成自簽證書,先下載cfssl工具
curl -L https://pkg.cfssl.org/R1.2/cfssl_linux-amd64 -o /usr/local/bin/cfssl
curl -L https://pkg.cfssl.org/R1.2/cfssljson_linux-amd64 -o /usr/local/bin/cfssljson
curl -L https://pkg.cfssl.org/R1.2/cfssl-certinfo_linux-amd64 -o /usr/local/bin/cfssl-certinfo
chmod +x /usr/local/bin/cfssl /usr/local/bin/cfssljson /usr/local/bin/cfssl-certinfo
創建以下三個文件,用來生成證書
# cat ca-config.json
{
"signing": {
"default": {
"expiry": "87600h"
},
"profiles": {
"www": {
"expiry": "87600h",
"usages": [
"signing",
"key encipherment",
"server auth",
"client auth"
]
}
}
}
}
# cat ca-csr.json
{
"CN": "etcd CA",
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"L": "Beijing",
"ST": "Beijing"
}
]
}
# cat server-csr.json
{
"CN": "etcd",
"hosts": [
"192.168.13.134",
"192.168.13.135",
"192.168.13.136"
],
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"L": "BeiJing",
"ST": "BeiJing"
}
]
}生成證書
cfssl gencert -initca ca-csr.json | cfssljson -bare ca -
cfssl gencert -ca=ca.pem -ca-key=ca-key.pem -config=ca-config.json -profile=www server-csr.json | cfssljson -bare server
# ls *pem
ca-key.pem ca.pem server-key.pem server.pem
1.1.2、部署Etcd集羣
二進制包下載地址:https://github.com/etcd-io/etcd/releases
以下部署步驟在規劃的三個etcd節點操作一樣,唯一不同的是etcd配置文件中的服務器IP要寫當前的
解壓二進制包:
# mkdir /opt/etcd/{bin,cfg,ssl} -p
# tar zxvf etcd-v3.2.12-linux-amd64.tar.gz
# mv etcd-v3.2.12-linux-amd64/{etcd,etcdctl} /opt/etcd/bin/創建etcd配置文件
# cat /opt/etcd/cfg/etcd
#[Member]
ETCD_NAME="etcd01"
ETCD_DATA_DIR="/var/lib/etcd/default.etcd"
ETCD_LISTEN_PEER_URLS="https://192.168.13.134:2380" #本機ip地址,server端口
ETCD_LISTEN_CLIENT_URLS="https://192.168.13.134:2379" #本機ip地址,數據庫端口
#[Clustering]
ETCD_INITIAL_ADVERTISE_PEER_URLS="https://192.168.13.134:2380"
ETCD_ADVERTISE_CLIENT_URLS="https://192.168.13.134:2379"
ETCD_INITIAL_CLUSTER="etcd01=https://192.168.13.134:2380,etcd02=https://192.168.13.135:2380,etcd03=https://192.168.13.136:2380"
ETCD_INITIAL_CLUSTER_TOKEN="etcd-cluster"
ETCD_INITIAL_CLUSTER_STATE="new"• ETCD_NAME #節點名稱
• ETCD_DATA_DIR #數據目錄
• ETCD_LISTEN_PEER_URLS #集羣通信監聽地址
• ETCD_LISTEN_CLIENT_URLS #客戶端訪問監聽地址
• ETCD_INITIAL_ADVERTISE_PEER_URLS #集羣通告地址
• ETCD_ADVERTISE_CLIENT_URLS #客戶端通告地址
• ETCD_INITIAL_CLUSTER #集羣節點地址
• ETCD_INITIAL_CLUSTER_TOKEN #集羣Token
• ETCD_INITIAL_CLUSTER_STATE 加入#集羣的當前狀態,new是新集羣,existing表示加入已有集羣
systemd管理etcd:
# cat /usr/lib/systemd/system/etcd.service
[Unit]
Description=Etcd Server
After=network.target
After=network-online.target
Wants=network-online.target
[Service]
Type=notify
EnvironmentFile=/opt/etcd/cfg/etcd
ExecStart=/opt/etcd/bin/etcd \
--name=${ETCD_NAME} \
--data-dir=${ETCD_DATA_DIR} \
--listen-peer-urls=${ETCD_LISTEN_PEER_URLS} \
--listen-client-urls=${ETCD_LISTEN_CLIENT_URLS},http://127.0.0.1:2379 \
--advertise-client-urls=${ETCD_ADVERTISE_CLIENT_URLS} \
--initial-advertise-peer-urls=${ETCD_INITIAL_ADVERTISE_PEER_URLS} \
--initial-cluster=${ETCD_INITIAL_CLUSTER} \
--initial-cluster-token=${ETCD_INITIAL_CLUSTER_TOKEN} \
--initial-cluster-state=new \
--cert-file=/opt/etcd/ssl/server.pem \
--key-file=/opt/etcd/ssl/server-key.pem \
--peer-cert-file=/opt/etcd/ssl/server.pem \
--peer-key-file=/opt/etcd/ssl/server-key.pem \
--trusted-ca-file=/opt/etcd/ssl/ca.pem \
--peer-trusted-ca-file=/opt/etcd/ssl/ca.pem
Restart=on-failure
LimitNOFILE=65536
[Install]
WantedBy=multi-user.target
**把剛纔生成的證書拷貝到配置文件中的位置:**
# cp ca*pem server*pem /opt/etcd/ssl注意:將完整的一份Etcd目錄,複製到其他兩個etcd服務器,只需修改ip地址即可
最後啓動三臺etcd
# systemctl start etcd
# systemctl enable etcd檢查健康狀態
[root@k8s-matser01 k8s]# /opt/etcd/bin/etcdctl --ca-file=/opt/etcd/ssl/ca.pem --cert-file=/opt/etcd/ssl/server.pem --key-file=/opt/etcd/ssl/server-key.pem --endpoints="https://192.168.13.134:2379,https://192.168.13.135:2379,https://192.168.13.136:2379" cluster-health
出現如下輸出,表示etcd集羣完成
member 98d5f0d49711f89d is healthy: got healthy result from https://192.168.13.135:2379
member b37efb70492212de is healthy: got healthy result from https://192.168.13.136:2379
member ffd0c8087276f422 is healthy: got healthy result from https://192.168.13.134:2379
cluster is healthy