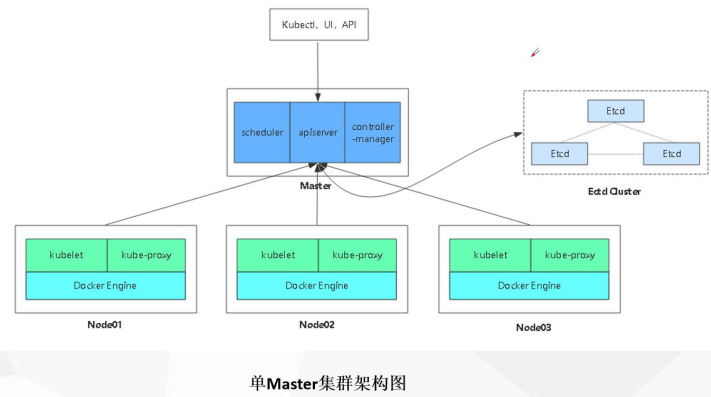
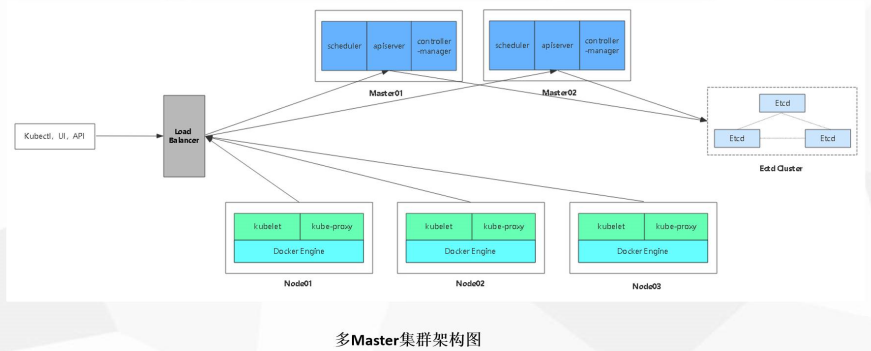
Kubernetes平臺環境規劃
部署環境
負載均衡
Nginx1:192.168.13.128/24
Nginx2:192.168.13.129/24
Master節點
master1:192.168.13.131/24 kube-apiserver kube-controller-manager kube-scheduler etcd
master2:192.168.13.130/24 kube-apiserver kube-controller-manager kube-scheduler etcd
Node節點
node1:192.168.13.132/24 kubelet kube-proxy docker flannel etcd
node2:192.168.13.133/24 kubelet kube-proxy docker flannel etcd
Kubernetes單節點部署步驟
1:自籤ETCD證書
2:ETCD部署
3:Node安裝docker
4:Flannel部署(先寫入子網到etcd)
-----------master---------------------------
5:自籤APIServer證書
6:部署APIServer組件(token,csv)
7:部署controller-manager(指定apiserver證書)和scheduler組件
-------------node----------------------------------
8:生成kubeconfig(bootstrap,kubeconfig和kube-proxy.kubeconfig)
9:部署kubelet組件
10:部署kube-proxy組件
---------------加入羣集-----------------
11:kubectl get csr && kubectl certificate approve 允許辦法證書,加入羣集
12:添加一個node節點
13:查看kubectl get node 節點一,etcd證書及flannel網絡部署
1,在master01中自籤ETCD證書
[root@master01 ~]# mkdir k8s
[root@master01 ~]# cd k8s/
[root@master01 k8s]# rz -E ##上傳etcd腳本
[root@master01 k8s]# ls
etcd-cert.sh etcd.shvim etcd-cert.sh ##證書創建腳本內容
cat > ca-config.json <<EOF
{
"signing": {
"default": {
"expiry": "87600h"
},
"profiles": {
"www": {
"expiry": "87600h",
"usages": [
"signing",
"key encipherment",
"server auth",
"client auth"
]
}
}
}
}
EOF
cat > ca-csr.json <<EOF
{
"CN": "etcd CA",
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"L": "Beijing",
"ST": "Beijing"
}
]
}
EOF
cfssl gencert -initca ca-csr.json | cfssljson -bare ca -
#-----------------------
cat > server-csr.json <<EOF
{
"CN": "etcd",
"hosts": [
"10.206.240.188",
"10.206.240.189",
"10.206.240.111"
],
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"L": "BeiJing",
"ST": "BeiJing"
}
]
}
EOF
cfssl gencert -ca=ca.pem -ca-key=ca-key.pem -config=ca-config.json -profile=www server-csr.json | cfssljson -bare servervim etcd.sh ##etcd服務腳本
#!/bin/bash
# example: ./etcd.sh etcd01 192.168.1.10 etcd02=https://192.168.1.11:2380,etcd03=https://192.168.1.12:2380
ETCD_NAME=$1
ETCD_IP=$2
ETCD_CLUSTER=$3
WORK_DIR=/opt/etcd
cat <<EOF >$WORK_DIR/cfg/etcd
#[Member]
ETCD_NAME="${ETCD_NAME}"
ETCD_DATA_DIR="/var/lib/etcd/default.etcd"
ETCD_LISTEN_PEER_URLS="https://${ETCD_IP}:2380"
ETCD_LISTEN_CLIENT_URLS="https://${ETCD_IP}:2379"
#[Clustering]
ETCD_INITIAL_ADVERTISE_PEER_URLS="https://${ETCD_IP}:2380"
ETCD_ADVERTISE_CLIENT_URLS="https://${ETCD_IP}:2379"
ETCD_INITIAL_CLUSTER="etcd01=https://${ETCD_IP}:2380,${ETCD_CLUSTER}"
ETCD_INITIAL_CLUSTER_TOKEN="etcd-cluster"
ETCD_INITIAL_CLUSTER_STATE="new"
EOF
cat <<EOF >/usr/lib/systemd/system/etcd.service
[Unit]
Description=Etcd Server
After=network.target
After=network-online.target
Wants=network-online.target
[Service]
Type=notify
EnvironmentFile=${WORK_DIR}/cfg/etcd
ExecStart=${WORK_DIR}/bin/etcd \
--name=\${ETCD_NAME} \
--data-dir=\${ETCD_DATA_DIR} \
--listen-peer-urls=\${ETCD_LISTEN_PEER_URLS} \
--listen-client-urls=\${ETCD_LISTEN_CLIENT_URLS},http://127.0.0.1:2379 \
--advertise-client-urls=\${ETCD_ADVERTISE_CLIENT_URLS} \
--initial-advertise-peer-urls=\${ETCD_INITIAL_ADVERTISE_PEER_URLS} \
--initial-cluster=\${ETCD_INITIAL_CLUSTER} \
--initial-cluster-token=\${ETCD_INITIAL_CLUSTER_TOKEN} \
--initial-cluster-state=new \
--cert-file=${WORK_DIR}/ssl/server.pem \
--key-file=${WORK_DIR}/ssl/server-key.pem \
--peer-cert-file=${WORK_DIR}/ssl/server.pem \
--peer-key-file=${WORK_DIR}/ssl/server-key.pem \
--trusted-ca-file=${WORK_DIR}/ssl/ca.pem \
--peer-trusted-ca-file=${WORK_DIR}/ssl/ca.pem
Restart=on-failure
LimitNOFILE=65536
[Install]
WantedBy=multi-user.target
EOF
systemctl daemon-reload
systemctl enable etcd
systemctl restart etcd[root@master01 k8s]# mkdir etcd-cert ##創建證書目錄
[root@master01 k8s]# mv etcd-cert.sh etcd-cert ##將腳本放到目錄中
[root@master01 k8s]# vim cfssl.sh ##工具下載腳本
curl -L https://pkg.cfssl.org/R1.2/cfssl_linux-amd64 -o /usr/local/bin/cfssl
curl -L https://pkg.cfssl.org/R1.2/cfssljson_linux-amd64 -o /usr/local/bin/cfssljson
curl -L https://pkg.cfssl.org/R1.2/cfssl-certinfo_linux-amd64 -o /usr/local/bin/cfssl-certinfo
chmod +x /usr/local/bin/cfssl /usr/local/bin/cfssljson /usr/local/bin/cfssl-certinfo
[root@master01 k8s]# bash cfssl.sh ##下載cfssl官方包
[root@master01 k8s]# ls /usr/local/bin/
cfssl cfssl-certinfo cfssljson
##cfssl生成證書工具、cfssljson通過傳入json文件生成證書、cfssl-certinfo查看證書信息
[root@master01 k8s]# cd /root/k8s/etcd-cert/ ##切換到證書腳本目錄下
[root@master01 etcd-cert]# ls
etcd-cert.sh##定義ca證書
[root@master01 etcd-cert]# cat > ca-config.json <<EOF
{
"signing": {
"default": {
"expiry": "87600h"
},
"profiles": {
"www": {
"expiry": "87600h",
"usages": [
"signing",
"key encipherment",
"server auth",
"client auth"
]
}
}
}
}
EOF ##實現證書的簽名
[root@master01 etcd-cert]# cat > ca-csr.json <<EOF
{
"CN": "etcd CA",
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"L": "Beijing",
"ST": "Beijing"
}
]
}
EOF[root@master01 etcd-cert]# ls
ca-config.json ca-csr.json etcd-cert.sh
[root@master01 etcd-cert]# cfssl gencert -initca ca-csr.json | cfssljson -bare ca -
##生產證書,生成ca-key.pem ca.pem
2020/02/09 18:09:13 [INFO] generating a new CA key and certificate from CSR
2020/02/09 18:09:13 [INFO] generate received request
2020/02/09 18:09:13 [INFO] received CSR
2020/02/09 18:09:13 [INFO] generating key: rsa-2048
2020/02/09 18:09:13 [INFO] encoded CSR
2020/02/09 18:09:13 [INFO] signed certificate with serial number 443437184464842782624738198723332409563005728279
[root@master01 etcd-cert]# ls
ca-config.json ca.csr ca-csr.json ca-key.pem ca.pem etcd-cert.sh##指定etcd三個節點之間的通信驗證
[root@master01 etcd-cert]#cat > server-csr.json <<EOF
{
"CN": "etcd",
"hosts": [
"192.168.13.131", ##三個主機的地址
"192.168.13.132",
"192.168.13.133"
],
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"L": "BeiJing",
"ST": "BeiJing"
}
]
}
EOF[root@master01 etcd-cert]# cfssl gencert -ca=ca.pem -ca-key=ca-key.pem -config=ca-config.json -profile=www server-csr.json | cfssljson -bare server
##生成ETCD證書 server-key.pem server.pem2,在master01和node節點上部署etcd
[root@master01 etcd-cert]# cd /root/k8s/
[root@master01 k8s]# rz -E ##將源碼包放到k8s目錄下
[root@master01 k8s]# ls
etcd-cert flannel-v0.10.0-linux-amd64.tar.gz
etcd.sh kubernetes-server-linux-amd64.tar.gz
etcd-v3.3.10-linux-amd64.tar.gz
[root@master01 k8s]# tar zxvf etcd-v3.3.10-linux-amd64.tar.gz ##解壓
[root@master01 k8s]# cd etcd-v3.3.10-linux-amd64/
[root@master01 etcd-v3.3.10-linux-amd64]# ls
Documentation etcd etcdctl README-etcdctl.md README.md READMEv2-etcdctl.md
[root@master01 etcd-v3.3.10-linux-amd64]# mkdir /opt/etcd/{cfg,bin,ssl} -p
##創建配置文件,命令文件,證書工作目錄
[root@master01 etcd-v3.3.10-linux-amd64]# mv etcd etcdctl /opt/etcd/bin/ ##放置命令
[root@master01 etcd-v3.3.10-linux-amd64]# cd ../etcd-cert/
[root@master01 etcd-cert]# cp *.pem /opt/etcd/ssl/ ##證書拷貝
[root@master01 etcd-cert]# ls /opt/etcd/ssl/
ca-key.pem ca.pem server-key.pem server.pem
[root@master01 etcd-cert]# cd ../
[root@master01 k8s]# bash etcd.sh etcd01 192.168.13.131 etcd02=https://192.168.13.132:2380,etcd03=https://192.168.13.133:2380
##執行etcd.sh服務腳本,進入卡住狀態等待其他節點加入
[root@master01 ~]# ps -ef | grep etcd
##使用另外一個會話打開,會發現etcd進程已經開啓
[root@master01 ~]# systemctl stop firewalld.service ##關閉防火牆
[root@master01 ~]# setenforce 0
#######node節點的防火牆也需要關閉
[root@node01 ~]# systemctl stop firewalld.service ##關閉防火牆
[root@node01 ~]# setenforce 0
#########
[root@master01 k8s]# scp -r /opt/etcd/ [email protected]:/opt ##拷貝證書去其他node節點
[root@master01 k8s]# scp -r /opt/etcd/ [email protected]:/opt
##啓動腳本拷貝其他node節點
[root@master01 k8s]# scp /usr/lib/systemd/system/etcd.service [email protected]:/usr/lib/systemd/system/
[root@master01 k8s]# scp /usr/lib/systemd/system/etcd.service [email protected]:/usr/lib/systemd/system/
#########修改node01的etcd配置文件#########
[root@node01 ~]# vim /opt/etcd/cfg/etcd
#[Member]
ETCD_NAME="etcd02" ##修改名稱
ETCD_DATA_DIR="/var/lib/etcd/default.etcd"
ETCD_LISTEN_PEER_URLS="https://192.168.13.132:2380" ##地址
ETCD_LISTEN_CLIENT_URLS="https://192.168.13.132:2379" ##地址修改
#[Clustering]
ETCD_INITIAL_ADVERTISE_PEER_URLS="https://192.168.13.132:2380" ##地址修改
ETCD_ADVERTISE_CLIENT_URLS="https://192.168.13.132:2379" ##地址修改
ETCD_INITIAL_CLUSTER="etcd01=https://192.168.13.131:2380,etcd02=https://192.168.13.132:2380,etcd03=https://192.168.13.133:2380"
ETCD_INITIAL_CLUSTER_TOKEN="etcd-cluster"
ETCD_INITIAL_CLUSTER_STATE="new"
#########修改node02的etcd配置文件#########
[root@node02 ~]# vim /opt/etcd/cfg/etcd
#[Member]
ETCD_NAME="etcd03" ##修改名稱
ETCD_DATA_DIR="/var/lib/etcd/default.etcd"
ETCD_LISTEN_PEER_URLS="https://192.168.13.133:2380" ##修改地址
ETCD_LISTEN_CLIENT_URLS="https://192.168.13.133:2379" ##修改地址
#[Clustering]
ETCD_INITIAL_ADVERTISE_PEER_URLS="https://192.168.13.133:2380" ##修改地址
ETCD_ADVERTISE_CLIENT_URLS="https://192.168.13.133:2379" ##修改地址
ETCD_INITIAL_CLUSTER="etcd01=https://192.168.13.131:2380,etcd02=https://192.168.13.132:2380,etcd03=https://192.168.13.133:2380"
ETCD_INITIAL_CLUSTER_TOKEN="etcd-cluster"
ETCD_INITIAL_CLUSTER_STATE="new"
#########在master01上啓動腳本等待節點加入#########
[root@master01 k8s]# bash etcd.sh etcd01 192.168.13.131 etcd02=https://192.168.13.132:2380,etcd03=https://192.168.13.133:2380
#########在node上啓動etcd服務#########
[root@node01 ~]# systemctl start etcd.service
[root@node02 ~]# systemctl start etcd.service
#########在master01上檢查羣集狀態#########
[root@master01 k8s]# cd etcd-cert/ ##切換到證書的目錄下
[root@master01 etcd-cert]# /opt/etcd/bin/etcdctl --ca-file=ca.pem --cert-file=server.pem --key-file=server-key.pem --endpoints="https://192.168.13.131:2379,https://192.168.13.132:2379,https://192.168.13.133:2379" cluster-health
##檢查羣集狀態
member 76e0a15c7cd72ef7 is healthy: got healthy result from https://192.168.13.133:2379
member cbcfa6e700d4aa11 is healthy: got healthy result from https://192.168.13.132:2379
member e4f560fae6a18df3 is healthy: got healthy result from https://192.168.13.131:2379
cluster is healthy3,在所有的node節點上安裝docker
[root@node01 ~]# yum install -y yum-utils device-mapper-persistent-data lvm2 ##安裝依賴包
[root@node01 ~]# yum-config-manager --add-repo https://mirrors.aliyun.com/docker-ce/linux/centos/docker-ce.repo
##設置阿里雲鏡像源
[root@node01 ~]# yum install -y docker-ce ##安裝docker
[root@node01 ~]# systemctl start docker.service
[root@node01 ~]# systemctl enable docker.service
[root@node01 ~]# tee /etc/docker/daemon.json <<-'EOF' ##容器加速
{
"registry-mirrors": ["https://3a9s8zx5.mirror.aliyuncs.com"]
}
EOF
[root@node01 ~]# systemctl daemon-reload ##重載
[root@node01 ~]# systemctl restart docker
[root@node01 ~]# vim /etc/sysctl.conf
net.ipv4.ip_forward=1 ##開啓路由轉發
[root@node01 ~]# sysctl -p ##重載
[root@node01 ~]# service network restart
[root@node01 ~]# systemctl restart docker 4,在所有node上部署flannel網絡
[root@master01 etcd-cert]# /opt/etcd/bin/etcdctl --ca-file=ca.pem --cert-file=server.pem --key-file=server-key.pem --endpoints="https://192.168.13.131:2379,https://192.168.13.132:2379,https://192.168.13.133:2379" set /coreos.com/network/config '{ "Network": "172.17.0.0/16", "Backend": {"Type": "vxlan"}}'
##寫入分配的子網段到ETCD中,供flannel使用,網絡爲172.17.0.0
[root@master01 etcd-cert]# /opt/etcd/bin/etcdctl --ca-file=ca.pem --cert-file=server.pem --key-file=server-key.pem --endpoints="https://192.168.13.131:2379,https://192.168.13.132:2379,https://192.168.13.133:2379" get /coreos.com/network/config
##get查看寫入的信息
[root@master01 etcd-cert]# cd ../
##拷貝到所有node節點(只需要部署在node節點即可)
[root@master01 k8s]# scp flannel-v0.10.0-linux-amd64.tar.gz [email protected]:/root
[root@master01 k8s]# scp flannel-v0.10.0-linux-amd64.tar.gz [email protected]:/root
#########在所有node節點上部署安裝flannel###########
[root@node01 ~]# tar zxvf flannel-v0.10.0-linux-amd64.tar.gz ##解壓
flanneld
mk-docker-opts.sh
README.md
[root@node01 ~]# mkdir /opt/kubernetes/{cfg,bin,ssl} -p
[root@node01 ~]# mv mk-docker-opts.sh flanneld /opt/kubernetes/bin/
[root@node01 ~]# rz -E ##上傳flannel腳本文件vim flannel.sh ##編輯flannel配置文件個啓動服務的腳本
#!/bin/bash
ETCD_ENDPOINTS=${1:-"http://127.0.0.1:2379"}
cat <<EOF >/opt/kubernetes/cfg/flanneld
FLANNEL_OPTIONS="--etcd-endpoints=${ETCD_ENDPOINTS} \
-etcd-cafile=/opt/etcd/ssl/ca.pem \
-etcd-certfile=/opt/etcd/ssl/server.pem \
-etcd-keyfile=/opt/etcd/ssl/server-key.pem"
EOF
cat <<EOF >/usr/lib/systemd/system/flanneld.service
[Unit]
Description=Flanneld overlay address etcd agent
After=network-online.target network.target
Before=docker.service
[Service]
Type=notify
EnvironmentFile=/opt/kubernetes/cfg/flanneld
ExecStart=/opt/kubernetes/bin/flanneld --ip-masq \$FLANNEL_OPTIONS
ExecStartPost=/opt/kubernetes/bin/mk-docker-opts.sh -k DOCKER_NETWORK_OPTIONS -d /run/flannel/subnet.env
Restart=on-failure
[Install]
WantedBy=multi-user.target
EOF
systemctl daemon-reload
systemctl enable flanneld
systemctl restart flanneld[root@node01 ~]# bash flannel.sh https://192.168.13.131:2379,https://192.168.13.132:2379,https://192.168.13.133:2379
##開啓flannel網絡功能
[root@node01 ~]# vim /usr/lib/systemd/system/docker.service ##修改服務啓動文件
13 # for containers run by docker
14 EnvironmentFile=/run/flannel/subnet.env ##添加此項
15 ExecStart=/usr/bin/dockerd $DOCKER_NETWORK_OPTIONS -H fd:// --containerd=/ru n/containerd/containerd.sock
##引用參數
[root@node01 ~]# cat /run/flannel/subnet.env ##查看子網段信息
DOCKER_OPT_BIP="--bip=172.17.45.1/24"
DOCKER_OPT_IPMASQ="--ip-masq=false"
DOCKER_OPT_MTU="--mtu=1450"
DOCKER_NETWORK_OPTIONS=" --bip=172.17.45.1/24 --ip-masq=false --mtu=1450"
[root@node01 ~]# systemctl daemon-reload ##重載docker
[root@node01 ~]# systemctl restart docker
[root@node01 ~]# ifconfig ##此時docker0網關爲172.17.45.1,flannel是虛擬網絡
[root@node01 ~]# docker run -it centos:7 /bin/bash ##安裝centos7並進入容器
[root@720f2727f307 /]# yum install net-tools -y ##安裝網絡工具
[root@720f2727f307 /]# ifconfig ##容器的地址爲172.17.45.2
##############node2和node1一樣的配置##############
##node2的docker0地址爲172.17.1.1
[root@node02 ~]# docker run -it centos:7 /bin/bash ##開啓容器並進入容器
[root@c2cfc9af3b9f /]# yum install -y net-tools
[root@c2cfc9af3b9f /]# ifconfig ##容器地址爲172.17.1.2
[root@c2cfc9af3b9f /]# ping 172.17.45.2 ##測試flannel網絡是否互通二,部署master01節點上 apiserver,kube-controller-manager,kube-scheduler三個組件
1,自籤APIServer證書
[root@master01 k8s]# rz -E ##上傳master腳本壓縮包
[root@master01 k8s]# ls
master.zip
[root@master01 k8s]# unzip master.zip ##解壓
Archive: master.zip
inflating: apiserver.sh
inflating: controller-manager.sh
inflating: scheduler.sh
[root@master01 k8s]# chmod +x controller-manager.sh ##給執行權限
[root@master01 k8s]# mkdir k8s-cert ##apiserver自簽證書目錄
[root@master01 k8s]# cd k8s-cert/
[root@master01 k8s-cert]# rz -E
[root@master01 k8s-cert]# ls ##上傳k8s證書腳本
k8s-cert.shvim k8s-cert.sh ##api證書腳本
cat > ca-config.json <<EOF
{
"signing": {
"default": {
"expiry": "87600h"
},
"profiles": {
"kubernetes": {
"expiry": "87600h",
"usages": [
"signing",
"key encipherment",
"server auth",
"client auth"
]
}
}
}
}
EOF
cat > ca-csr.json <<EOF
{
"CN": "kubernetes",
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"L": "Beijing",
"ST": "Beijing",
"O": "k8s",
"OU": "System"
}
]
}
EOF
cfssl gencert -initca ca-csr.json | cfssljson -bare ca -
#-----------------------
cat > server-csr.json <<EOF
{
"CN": "kubernetes",
"hosts": [
"10.0.0.1",
"127.0.0.1",
"192.168.13.131", //master1
"192.168.13.130", //master2
"192.168.13.100", //vip 公共訪問入口
"192.168.13.128", //lb負載均衡 (master)
"192.168.13.129", //lb負載均衡(backup)
"kubernetes",
"kubernetes.default",
"kubernetes.default.svc",
"kubernetes.default.svc.cluster",
"kubernetes.default.svc.cluster.local"
],
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"L": "BeiJing",
"ST": "BeiJing",
"O": "k8s",
"OU": "System"
}
]
}
EOF
cfssl gencert -ca=ca.pem -ca-key=ca-key.pem -config=ca-config.json -profile=kubernetes server-csr.json | cfssljson -bare server
#-----------------------
cat > admin-csr.json <<EOF
{
"CN": "admin",
"hosts": [],
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"L": "BeiJing",
"ST": "BeiJing",
"O": "system:masters",
"OU": "System"
}
]
}
EOF
cfssl gencert -ca=ca.pem -ca-key=ca-key.pem -config=ca-config.json -profile=kubernetes admin-csr.json | cfssljson -bare admin
#-----------------------
cat > kube-proxy-csr.json <<EOF
{
"CN": "system:kube-proxy",
"hosts": [],
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"L": "BeiJing",
"ST": "BeiJing",
"O": "k8s",
"OU": "System"
}
]
}
EOF
cfssl gencert -ca=ca.pem -ca-key=ca-key.pem -config=ca-config.json -profile=kubernetes kube-proxy-csr.json | cfssljson -bare kube-proxy[root@master01 k8s-cert]# bash k8s-cert.sh ##執行腳本
[root@master01 k8s-cert]# ls *pem ##生成8個證書
admin-key.pem ca-key.pem kube-proxy-key.pem server-key.pem
admin.pem ca.pem kube-proxy.pem server.pem
[root@master01 k8s-cert]# mkdir /opt/kubernetes/{cfg,bin,ssl} -p ##創建工作目錄
[root@master01 k8s-cert]# cp ca*pem server*pem /opt/kubernetes/ssl/ ##證書複製到工作目錄2,部署APIServer組件(token,csv)
[root@master01 k8s-cert]# cd ..
[root@master01 k8s]# tar zxvf kubernetes-server-linux-amd64.tar.gz ##解壓
[root@master01 k8s]# cd kubernetes/server/bin/ ##查看工具
[root@master01 bin]# ls
apiextensions-apiserver kube-controller-manager.tar
cloud-controller-manager kubectl
cloud-controller-manager.docker_tag kubelet
cloud-controller-manager.tar kube-proxy
hyperkube kube-proxy.docker_tag
kubeadm kube-proxy.tar
kube-apiserver kube-scheduler
kube-apiserver.docker_tag kube-scheduler.docker_tag
kube-apiserver.tar kube-scheduler.tar
kube-controller-manager mounter
kube-controller-manager.docker_tag
[root@master01 bin]# cp kube-apiserver kubectl kube-scheduler kube-controller-manager /opt/kubernetes/bin/
##將master的組件拷貝到工作目錄下
[root@master01 bin]# head -c 16 /dev/urandom | od -An -t x | tr -d ' ' ##隨機生成序列號
b555625c736044a609cf020902e773fa
[root@master01 bin]# vim /opt/kubernetes/cfg/token.csv ##編輯token角色
b555625c736044a609cf020902e773fa,kubelet-bootstrap,10001,"system:kubelet-bootstrap"
##序列號,用戶名,id,角色vim /root/k8s/apiserver.sh ##查看apiserver腳本
#!/bin/bash
MASTER_ADDRESS=$1
ETCD_SERVERS=$2
cat <<EOF >/opt/kubernetes/cfg/kube-apiserver
KUBE_APISERVER_OPTS="--logtostderr=true \\
--v=4 \\
--etcd-servers=${ETCD_SERVERS} \\
--bind-address=${MASTER_ADDRESS} \\
--secure-port=6443 \\
--advertise-address=${MASTER_ADDRESS} \\
--allow-privileged=true \\
--service-cluster-ip-range=10.0.0.0/24 \\
--enable-admission-plugins=NamespaceLifecycle,LimitRanger,ServiceAccount,Res ourceQuota,NodeRestriction \\
--authorization-mode=RBAC,Node \\
--kubelet-https=true \\
--enable-bootstrap-token-auth \\
--token-auth-file=/opt/kubernetes/cfg/token.csv \\
--service-node-port-range=30000-50000 \\
--tls-cert-file=/opt/kubernetes/ssl/server.pem \\
--tls-private-key-file=/opt/kubernetes/ssl/server-key.pem \\
--client-ca-file=/opt/kubernetes/ssl/ca.pem \\
--service-account-key-file=/opt/kubernetes/ssl/ca-key.pem \\
--etcd-cafile=/opt/etcd/ssl/ca.pem \\
--etcd-certfile=/opt/etcd/ssl/server.pem \\
--etcd-keyfile=/opt/etcd/ssl/server-key.pem"
EOF
cat <<EOF >/usr/lib/systemd/system/kube-apiserver.service
[Unit]
Description=Kubernetes API Server
Documentation=https://github.com/kubernetes/kubernetes
[Service]
EnvironmentFile=-/opt/kubernetes/cfg/kube-apiserver
ExecStart=/opt/kubernetes/bin/kube-apiserver \$KUBE_APISERVER_OPTS
Restart=on-failure
[Install]
WantedBy=multi-user.target
EOF
systemctl daemon-reload
systemctl enable kube-apiserver
systemctl restart kube-apiserver[root@master01 bin]# cd /root/k8s/
[root@master01 k8s]# bash apiserver.sh 192.168.13.131 https://192.168.13.131:2379,https://192.168.13.132:2379,https://192.168.13.133:2379
##開啓apiserver前面是本地地址,後面是etcd羣集的地址
[root@master01 k8s]# ps aux | grep kube ##檢查進程是否啓動成功
[root@master01 k8s]# cat /opt/kubernetes/cfg/kube-apiserver ##查看配置文件
[root@master01 k8s]# netstat -ntap | grep 6443 ##查看https的端口
tcp 0 0 192.168.13.131:6443 0.0.0.0:* LISTEN 38191/kube-apiserve
tcp 0 0 192.168.13.131:6443 192.168.13.131:34900 ESTABLISHED 38191/kube-apiserve
tcp 0 0 192.168.13.131:34900 192.168.13.131:6443 ESTABLISHED 38191/kube-apiserve
[root@master01 k8s]# netstat -ntap | grep 8080 ##查看8080端口
tcp 0 0 127.0.0.1:8080 0.0.0.0:* LISTEN 38191/kube-apiserve 3,部署controller-manager(指定apiserver證書)和scheduler組件
vim scheduler.sh ##調度的腳本
#!/bin/bash
MASTER_ADDRESS=$1
cat <<EOF >/opt/kubernetes/cfg/kube-scheduler
KUBE_SCHEDULER_OPTS="--logtostderr=true \\
--v=4 \\
--master=${MASTER_ADDRESS}:8080 \\
--leader-elect"
EOF
cat <<EOF >/usr/lib/systemd/system/kube-scheduler.service
[Unit]
Description=Kubernetes Scheduler
Documentation=https://github.com/kubernetes/kubernetes
[Service]
EnvironmentFile=-/opt/kubernetes/cfg/kube-scheduler
ExecStart=/opt/kubernetes/bin/kube-scheduler \$KUBE_SCHEDULER_OPTS
Restart=on-failure
[Install]
WantedBy=multi-user.target
EOF
systemctl daemon-reload
systemctl enable kube-scheduler
systemctl restart kube-scheduler[root@master01 k8s]# ./scheduler.sh 127.0.0.1 ##開啓scheduler服務vim controller-manager.sh ##控制管理腳本
#!/bin/bash
MASTER_ADDRESS=$1
cat <<EOF >/opt/kubernetes/cfg/kube-controller-manager
KUBE_CONTROLLER_MANAGER_OPTS="--logtostderr=true \\
--v=4 \\
--master=${MASTER_ADDRESS}:8080 \\
--leader-elect=true \\
--address=127.0.0.1 \\
--service-cluster-ip-range=10.0.0.0/24 \\
--cluster-name=kubernetes \\
--cluster-signing-cert-file=/opt/kubernetes/ssl/ca.pem \\
--cluster-signing-key-file=/opt/kubernetes/ssl/ca-key.pem \\
--root-ca-file=/opt/kubernetes/ssl/ca.pem \\
--service-account-private-key-file=/opt/kubernetes/ssl/ca-key.pem \\
--experimental-cluster-signing-duration=87600h0m0s"
EOF
cat <<EOF >/usr/lib/systemd/system/kube-controller-manager.service
[Unit]
Description=Kubernetes Controller Manager
Documentation=https://github.com/kubernetes/kubernetes
[Service]
EnvironmentFile=-/opt/kubernetes/cfg/kube-controller-manager
ExecStart=/opt/kubernetes/bin/kube-controller-manager \$KUBE_CONTROLLER_MANAGER_OPTS
Restart=on-failure
[Install]
WantedBy=multi-user.target
EOF
systemctl daemon-reload
systemctl enable kube-controller-manager
systemctl restart kube-controller-manager[root@master01 k8s]# ./controller-manager.sh 127.0.0.1 ##啓動controller-manager
[root@master01 k8s]# /opt/kubernetes/bin/kubectl get cs ##查看master 節點狀態
NAME STATUS MESSAGE ERROR
scheduler Healthy ok
controller-manager Healthy ok
etcd-2 Healthy {"health":"true"}
etcd-0 Healthy {"health":"true"}
etcd-1 Healthy {"health":"true"}三,部署node節點上kubelet kube-proxy組件
1,生成kubeconfig(bootstrap,kubeconfig和kube-proxy.kubeconfig)
##在master01上操作
[root@master01 k8s]# cd kubernetes/server/bin/
##把 kubelet、kube-proxy拷貝到node節點上去
[root@master01 bin]# scp kubelet kube-proxy [email protected]:/opt/kubernetes/bin/
[root@master01 bin]# scp kubelet kube-proxy [email protected]:/opt/kubernetes/bin/
##在node節點上操作
[root@node01 ~]# rz -E ##上傳node腳本壓縮包
[root@node01 ~]# unzip node.zip ##解壓
Archive: node.zip
inflating: proxy.sh
inflating: kubelet.sh
##在master01上操作
[root@master01 bin]# cd /root/k8s/
[root@master01 k8s]# mkdir kubeconfig ##創建目錄
[root@master01 k8s]# cd kubeconfig/
[root@master01 kubeconfig]# rz -E ##上傳kubeconfig腳本
[root@master01 kubeconfig]# ls
kubeconfig.sh
[root@master01 kubeconfig]# cat /opt/kubernetes/cfg/token.csv
b555625c736044a609cf020902e773fa,kubelet-bootstrap,10001,"system:kubelet-bootstrap"
##複製序列號進行腳本修改vim kubeconfig.sh ##腳本信息
##token部分要刪除
APISERVER=$1
SSL_DIR=$2
# 創建kubelet bootstrapping kubeconfig
export KUBE_APISERVER="https://$APISERVER:6443"
# 設置集羣參數
kubectl config set-cluster kubernetes \
--certificate-authority=$SSL_DIR/ca.pem \
--embed-certs=true \
--server=${KUBE_APISERVER} \
--kubeconfig=bootstrap.kubeconfig
# 設置客戶端認證參數
kubectl config set-credentials kubelet-bootstrap \
--token=b555625c736044a609cf020902e773fa \ ##修改序列號
--kubeconfig=bootstrap.kubeconfig
# 設置上下文參數
kubectl config set-context default \
--cluster=kubernetes \
--user=kubelet-bootstrap \
--kubeconfig=bootstrap.kubeconfig
# 設置默認上下文
kubectl config use-context default --kubeconfig=bootstrap.kubeconfig
#----------------------
# 創建kube-proxy kubeconfig文件
kubectl config set-cluster kubernetes \
--certificate-authority=$SSL_DIR/ca.pem \
--embed-certs=true \
--server=${KUBE_APISERVER} \
--kubeconfig=kube-proxy.kubeconfig
kubectl config set-credentials kube-proxy \
--client-certificate=$SSL_DIR/kube-proxy.pem \
--client-key=$SSL_DIR/kube-proxy-key.pem \
--embed-certs=true \
--kubeconfig=kube-proxy.kubeconfig
kubectl config set-context default \
--cluster=kubernetes \
--user=kube-proxy \
--kubeconfig=kube-proxy.kubeconfig
kubectl config use-context default --kubeconfig=kube-proxy.kubeconfig[root@master01 kubeconfig]# vim /etc/profile ##修改環境變量
export PATH=$PATH:/opt/kubernetes/bin/
[root@master01 kubeconfig]# source /etc/profile ##刷新配置文件
[root@master01 kubeconfig]# bash kubeconfig 192.168.13.131 /root/k8s/k8s-cert/ ##生成配置文件
[root@master01 kubeconfig]# ls
bootstrap.kubeconfig kubeconfig kube-proxy.kubeconfig
[root@master01 kubeconfig]# scp bootstrap.kubeconfig kube-proxy.kubeconfig [email protected]:/opt/kubernetes/cfg/
##拷貝配置文件到node節點
[root@master01 kubeconfig]# scp bootstrap.kubeconfig kube-proxy.kubeconfig [email protected]:/opt/kubernetes/cfg/
[root@master01 kubeconfig]# kubectl create clusterrolebinding kubelet-bootstrap --clusterrole=system:node-bootstrapper --user=kubelet-bootstrap
##創建bootstrap角色賦予權限用於連接apiserver請求籤名(關鍵)2,部署kubelet組件
#####在node01上操作#######
vim kubelet.sh 腳本信息
#!/bin/bash
NODE_ADDRESS=$1
DNS_SERVER_IP=${2:-"10.0.0.2"}
cat <<EOF >/opt/kubernetes/cfg/kubelet
KUBELET_OPTS="--logtostderr=true \\
--v=4 \\
--hostname-override=${NODE_ADDRESS} \\
--kubeconfig=/opt/kubernetes/cfg/kubelet.kubeconfig \\
--bootstrap-kubeconfig=/opt/kubernetes/cfg/bootstrap.kubeconfig \\
--config=/opt/kubernetes/cfg/kubelet.config \\
--cert-dir=/opt/kubernetes/ssl \\
--pod-infra-container-image=registry.cn-hangzhou.aliyuncs.com/google-containers/pause-amd64:3.0"
EOF
cat <<EOF >/opt/kubernetes/cfg/kubelet.config
kind: KubeletConfiguration
apiVersion: kubelet.config.k8s.io/v1beta1
address: ${NODE_ADDRESS}
port: 10250
readOnlyPort: 10255
cgroupDriver: cgroupfs
clusterDNS:
- ${DNS_SERVER_IP}
clusterDomain: cluster.local.
failSwapOn: false
authentication:
anonymous:
enabled: true
EOF
cat <<EOF >/usr/lib/systemd/system/kubelet.service
[Unit]
Description=Kubernetes Kubelet
After=docker.service
Requires=docker.service
[Service]
EnvironmentFile=/opt/kubernetes/cfg/kubelet
ExecStart=/opt/kubernetes/bin/kubelet \$KUBELET_OPTS
Restart=on-failure
KillMode=process
[Install]
WantedBy=multi-user.target
EOF
systemctl daemon-reload
systemctl enable kubelet
systemctl restart kubelet[root@node01 ~]# bash kubelet.sh 192.168.13.132 ##執行腳本
[root@node01 ~]# ps aux | grep kube ##查看服務啓動狀態
##########在master01上操作############
[root@master01 kubeconfig]# kubectl get csr ##查看證書狀態
NAME AGE REQUESTOR CONDITION
node-csr-PvqJh9Nza5SyPUakuwOkiMUsh7zo3ZG9vw3OTNtlkgg 73s kubelet-bootstrap Pending
##等待集羣給該節點頒發證書
[root@master01 kubeconfig]# kubectl certificate approve node-csr-PvqJh9Nza5SyPUakuwOkiMUsh7zo3ZG9vw3OTNtlkgg
[root@master01 kubeconfig]# kubectl get csr ##查看證書狀態
NAME AGE REQUESTOR CONDITION
node-csr-PvqJh9Nza5SyPUakuwOkiMUsh7zo3ZG9vw3OTNtlkgg 3m34s kubelet-bootstrap Approved,Issued
##已經被允許加入羣集
[root@master01 kubeconfig]# kubectl get node ##查看羣集節點,成功加入node01節點
NAME STATUS ROLES AGE VERSION
192.168.13.132 Ready <none> 115s v1.12.33,部署kube-proxy組件
vim proxy.sh ##proxy腳本
#!/bin/bash
NODE_ADDRESS=$1
cat <<EOF >/opt/kubernetes/cfg/kube-proxy
KUBE_PROXY_OPTS="--logtostderr=true \\
--v=4 \\
--hostname-override=${NODE_ADDRESS} \\
--cluster-cidr=10.0.0.0/24 \\
--proxy-mode=ipvs \\
--kubeconfig=/opt/kubernetes/cfg/kube-proxy.kubeconfig"
EOF
cat <<EOF >/usr/lib/systemd/system/kube-proxy.service
[Unit]
Description=Kubernetes Proxy
After=network.target
[Service]
EnvironmentFile=-/opt/kubernetes/cfg/kube-proxy
ExecStart=/opt/kubernetes/bin/kube-proxy \$KUBE_PROXY_OPTS
Restart=on-failure
[Install]
WantedBy=multi-user.target
EOF
systemctl daemon-reload
systemctl enable kube-proxy
systemctl restart kube-proxy##在node01節點操作
[root@node01 ~]# bash proxy.sh 192.168.13.132 ##啓動proxy服務
[root@node01 ~]# systemctl status kube-proxy.service ##查看服務狀態4,部署node02節點
##在node01上操作
[root@node01 ~]# scp -r /opt/kubernetes/ [email protected]:/opt/
//把現成的/opt/kubernetes目錄複製到其他節點進行修改即可
[root@node01 ~]# scp /usr/lib/systemd/system/{kubelet,kube-proxy}.service [email protected]:/usr/lib/systemd/system/
//把kubelet,kube-proxy的service文件拷貝到node2中
##在node02上操作,進行修改
[root@node02 ~]# cd /opt/kubernetes/ssl/ ##切換到證書目錄下
[root@node02 ssl]# ls
kubelet-client-2020-02-10-00-10-11.pem kubelet.crt
kubelet-client-current.pem kubelet.key
[root@node02 ssl]# rm -rf * ##首先刪除複製過來的證書,等會node02會自行申請證書
[root@node02 ssl]# cd ../cfg/ ##修改配置文件kubelet kubelet.config kube-proxy(三個配置文件)
[root@node02 cfg]# vim kubelet
--hostname-override=192.168.13.133 \ ##修改地址
[root@node02 cfg]# vim kubelet.config
address: 192.168.13.133 ##修改地址
[root@node02 cfg]# vim kube-proxy
--hostname-override=192.168.13.133 \ ##修改地址
[root@node02 cfg]# systemctl start kubelet.service ##啓動kubelet服務
[root@node02 cfg]# systemctl enable kubelet.service
[root@node02 cfg]# systemctl start kube-proxy.service ##啓動kube-proxy服務
[root@node02 cfg]# systemctl enable kube-proxy.service四,加入羣集
##在master01上操作
[root@master01 k8s]# kubectl get csr ##查看請求
NAME AGE REQUESTOR CONDITION
node-csr-PvqJh9Nza5SyPUakuwOkiMUsh7zo3ZG9vw3OTNtlkgg 23m kubelet-bootstrap Approved,Issued
node-csr-qE6kNPzFp6dducllhsQucd-3PJQA5t7eVf-xNkx48MA 103s kubelet-bootstrap Pending
[root@master01 k8s]# kubectl certificate approve node-csr-qE6kNPzFp6dducllhsQucd-3PJQA5t7eVf-xNkx48MA
//授權許可加入羣集
[root@master01 k8s]# kubectl get node ##查看羣集中的節點
NAME STATUS ROLES AGE VERSION
192.168.13.132 Ready <none> 21m v1.12.3
192.168.13.133 Ready <none> 70s v1.12.3