在IOS12.4之前,建立安全的站點間隧道只能使用GRE Over IPSec,但是從IOS 12.4 這個版本開始,Cisco設計了一個全新的隧道技術,這個技術被稱爲Virtual Tunnel Interface(VTI)。其實這就是一個IPsec的隧道技術,使用戶無需再依託GRE,可以直接使用IPsec來建立一個隧道接口。
因此,相比GRE Over IPSec技術,VTI技術減少了每個饅中GRE的頭部的4個字節。由於VTI也是一個隧道接口,因此它也能夠解決普通IPSec ***存在的三大問題。
VTI技術分爲兩種:
靜態VTI(Static VTI,SVTI)
動態VTI(Dynamic VTI,DVTI)
下面來使用SVTI技術實現兩個站點的***互聯(同GRE一樣兩個站點需要都是靜態IP地址。)
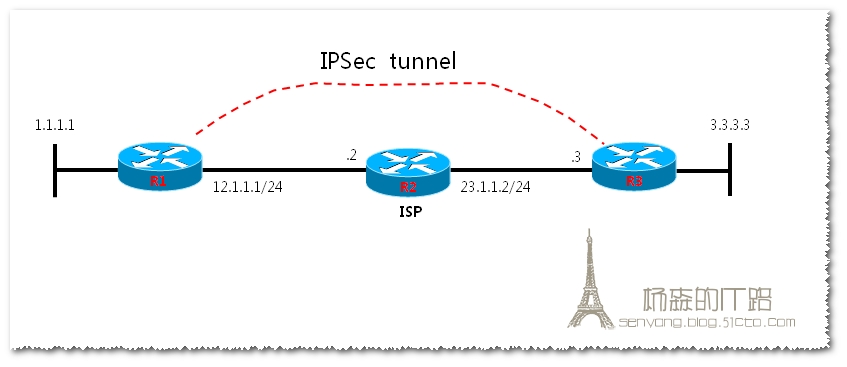
實驗環境:
實驗拓撲:
實驗配置:
基礎配置如下:
R1配置:
en
conf t
host R1
int f0/0
ip add 12.1.1.1 255.255.255.0
no shut
int lo 0
ip add 1.1.1.1 255.255.255.0
ip route 0.0.0.0 0.0.0.0 12.1.1.2
R2配置:
en
conf t
host R2
int f0/0
ip add 12.1.1.2 255.255.255.0
no shut
int f1/0
ip add 23.1.1.2 255.255.255.0
no shut
R3配置:
en
conf t
host R3
int f1/0
ip add 23.1.1.3 255.255.255.0
no shut
int lo 0
ip add 3.3.3.3 255.255.255.0
ip route 0.0.0.0 0.0.0.0 23.1.1.2
配置完成後,檢測R1和R3的連通性:
在R1上pingR3的公網IP地址:
R1#ping 23.1.1.3
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 23.1.1.3, timeout is 2 seconds:
!!!!!
Success rate is 100 percent (5/5), round-trip min/avg/max = 60/67/80 ms
可以ping通,說明公網通信正常。
R1配置:
crypto isakmp policy 10
hash md5
authentication pre-share
crypto isakmp key cisco address 23.1.1.3
crypto ipsec transform-set trans esp-des esp-md5-hmac
crypto ipsec profile ipsec-profile
set transform-set trans
R3配置:
crypto isakmp policy 10
hash md5
authentication pre-share
crypto isakmp key cisco address 12.1.1.1
crypto ipsec transform-set trans esp-des esp-md5-hmac
crypto ipsec profile ipsec-profile
set transform-set trans
配置SVTI:
R1:
interface Tunnel0
ip address 172.16.1.1 255.255.255.0
tunnel source FastEthernet0/0
tunnel destination 23.1.1.3
tunnel mode ipsec ipv4
tunnel protection ipsec profile ipsec-profile
R3:
interface Tunnel0
ip address 172.16.1.2 255.255.255.0
tunnel source FastEthernet1/0
tunnel destination 12.1.1.1
tunnel mode ipsec ipv4
tunnel protection ipsec profile ipsec-profile
驗證:
R1#show crypto isakmp sa
IPv4 Crypto ISAKMP SA
dst src state conn-id slot status
12.1.1.1 23.1.1.3 QM_IDLE 1001 0 ACTIVE
ping測試
R1#ping 172.16.1.2
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 172.16.1.2, timeout is 2 seconds:
!!!!!
Success rate is 100 percent (5/5), round-trip min/avg/max = 124/144/168 ms