本實驗限速設備是用一臺cisco2811路由器來完成,本實驗分兩種方法來做
先看下路由器的flash:
yourname#dir
Directory of flash:/
1 -rw- 25438028 Oct 22 2010 02:25:58 +00:00 c2800nm-ipbase-mz.124-15.T.bin
2 -rw- 1505280 Oct 22 2010 02:26:08 +00:00 common.tar
3 -rw- 931840 Oct 22 2010 02:26:16 +00:00 es.tar
4 -rw- 1038 Oct 22 2010 02:26:20 +00:00 home.shtml
5 -rw- 112640 Oct 22 2010 02:26:26 +00:00 home.tar
6 -rw- 415956 Oct 22 2010 02:26:34 +00:00 sslclient-win-1.1.4.176.pkg
7 -rw- 2748 Oct 22 2010 02:26:38 +00:00 sdmconfig-2811.cfg
8 -rw- 35316 Apr 5 2011 06:09:42 +00:00 crashinfo_20110405-060943
9 -rw- 42068 Apr 5 2011 06:30:26 +00:00 crashinfo_20110405-063027
128733184 bytes total (100229120 bytes free)
以下是實驗過程
第一步:用ACL定義要做限速網段或ip地址,一會做分類的時候要調用
access-list 102 permit ip 192.168.1.0 0.0.0.255 any
access-list 102 permit ip any 192.168.1.0 0.0.0.255
第二步:定義class-map ,調用第一步的ACL
class-map match-all 102
match access-group 102
第三步:定義policy-map,調用class-map,做速率限制
policy-map 102
class 102
police 256000 8000 conform-action transmit exceed-action drop
第四步:把policy-map應用到接口上
interface FastEthernet0/1
service-policy input 102
service-policy output 102
*Apr 5 06:24:04.023: %IP_VFR-4-FRAG_TABLE_OVERFLOW: FastEthernet0/1: the fragment table has reached its maximum threshold 16
yourname#sh policy-map int f0/1
FastEthernet0/1
Service-policy input: 102
Class-map: 102 (match-all)
2746 packets, 672324 bytes
5 minute offered rate 20000 bps, drop rate 0 bps
Match: access-group 102
police:
cir 256000 bps, bc 8000 bytes
conformed 2746 packets, 672324 bytes; actions:
transmit
exceeded 0 packets, 0 bytes; actions:
drop
conformed 90000 bps, exceed 0 bps
Class-map: class-default (match-any)
13407 packets, 1753107 bytes
5 minute offered rate 49000 bps, drop rate 0 bps
Match: any
Service-policy output: 102
Class-map: 102 (match-all)
3506 packets, 2954143 bytes
5 minute offered rate 68000 bps, drop rate 44000 bps
Match: access-group 102
police:
cir 256000 bps, bc 8000 bytes
conformed 2243 packets, 1195420 bytes; actions:
transmit
exceeded 1263 packets, 1758723 bytes; actions:
drop
conformed 162000 bps, exceed 239000 bps
Class-map: class-default (match-any)
15064 packets, 18750663 bytes
5 minute offered rate 430000 bps, drop rate 0 bps
Match: any
yourname#
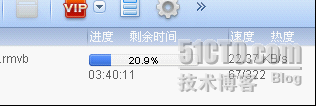
根據上面信息可以知道已經有流量被drop,也是就是超出限制的部分流量,還有一個單位是要注意的,是bit而不是Byte。下面是迅雷的截圖
實驗前:
<?xml:namespace prefix="dd_belatedpng">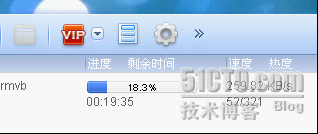
實驗後:
上面是第一種做限速的方法,下面我們來看另外一種簡單方法
首先也是定義ACL:然後直接在接口下啓用rate-limit:
access-list 102 permit ip 192.168.1.0 0.0.0.255 any access-list 102 permit ip any 192.168.1.0 0.0.0.255 interface FastEthernet0/1 rate-limit input access-group 102 256000 1500 2000 conform-action transmit exceed-action drop rate-limit output access-group 102 256000 1500 2000 conform-action transmit exceed-action drop
這就可以了,限速效果跟第一種方法相當
上面兩種方法的配置是對整個ip地址段來限速,如果我們要對ip段中的每一個ip進行限速25.6KB/s的話,就要用下面的方法了:
access-list 121 permit ip host 192.168.0.21 any access-list 121 permit ip any host 192.168.0.21 ! access-list 122 permit ip host 192.168.0.22 any access-list 122 permit ip any host 192.168.0.22 ! access-list 123 permit ip host 192.168.0.23 any access-list 123 permit ip any host 192.168.0.23 ! class-map match-all 121 match access-group 121 ! class-map match-all 122 match access-group 122 ! policy-map xiansu class 121 police 2560000 8000 conform-action transmit exceed-action drop class 122 police 2560000 8000 conform-action transmit exceed-action drop ! interface FastEthernet0/1 service-policy input xiansu service-policy output xiansu
上面是對192.168.0.21,192.168.0.21限速256KB/s,要是限制整個段的ip,那就自己慢慢寫吧。