Zabbix監控docker
公司的測試環境很多機器都用了docker,由於有好幾套的測試環境,進入容器檢查問題又很耗時 ,所以就在zabbix中做了監控,這樣最快的發現問題。節約解決問題的時間。
廢話不多少 ,下面操作是看了網上好多的博客做的,大部分東西都是牛人們做過的,我在這裏只是借鑑並留下自己的操作。
借鑑博客:
http://blog.csdn.net/messiademo/article/details/52241854
http://dl528888.blog.51cto.com/2382721/1660844
1.1Agent端安裝
1.2安裝pip工具
由於zabbix-agent端上要安裝一個python的腳本,所以用的到pip
#wget"https://pypi.python.org/packages/source/p/pip/pip-1.5.4.tar.gz#md5=834b2904f92d46aaa333267fb1c922bb"--no-check-certificate
#tar -xzvf pip-1.5.4.tar.gz
#cd pip-1.5.4
#python setup.py install
安裝docker-py
#pip install docker-py
1.3監控腳本
腳本路徑:mkdir –p /usr/local/zabbix/bin/
腳本權限:chmod 777/usr/local/zabbix/bin/zabbix*
屬主屬組:chown –Rzabbixzabbix /usr/local/zabbix/bin/zabbix*
1.3.1容器檢查腳本
這個腳本用於獲取容器名
[root@test4 bin]# cat/usr/local/zabbix/bin/zabbix_low_discovery.sh
#!/bin/bash
#Fucation:zabbix low-level discovery
docker() {
port=($(sudo docker ps -a|grep -v "CONTAINER ID"|awk '{print$NF}'))
printf '{\n'
printf '\t"data":[\n'
for key in ${!port[@]}
do
if [["${#port[@]}" -gt 1 && "${key}" -ne"$((${#port[@]}-1))" ]];then
printf '\t {\n'
printf"\t\t\t\"{#CONTAINERNAME}\":\"${port[${key}]}\"},\n"
else [[ "${key}" -eq "((${#port[@]}-1))" ]]
printf '\t {\n'
printf"\t\t\t\"{#CONTAINERNAME}\":\"${port[${key}]}\"}\n"
fi
done
printf '\t ]\n'
printf '}\n'
}
case $1 in
docker)
docker
;;
*)
echo "Usage:`basename $0` {docker}"
;;
Esac
檢查腳本效果
[root@test4 bin]# sh zabbix_low_discovery.sh docker
{
"data":[
{
"{#CONTAINERNAME}":"docker111"},
{
"{#CONTAINERNAME}":"docker110"},
{
"{#CONTAINERNAME}":"docker109"},
{
"{#CONTAINERNAME}":"docker108"},
{
"{#CONTAINERNAME}":"docker107"},
{
"{#CONTAINERNAME}":"docker106"},
{
"{#CONTAINERNAME}":"docker105"},
{
"{#CONTAINERNAME}":"docker104"},
{
"{#CONTAINERNAME}":"docker103"},
{
"{#CONTAINERNAME}":"docker102"},
{
"{#CONTAINERNAME}":"docker101"}
]
}
1.3.2獲取docker容器中信息的腳本
[root@test4 bin]# catzabbix_monitor_docker.py
#!/usr/bin/env python
#-*- coding: utf-8 -*-
from docker import Client
import os
import re
import sys
import subprocess
import time
defcheck_container_stats(container_name,collect_item):
globalresult
result=0
container_collect=docker_client.stats(container_name)
old_result=eval(container_collect.next())
new_result=eval(container_collect.next())
container_collect.close()
ifcollect_item == 'cpu_total_usage':
result=new_result['cpu_stats']['cpu_usage']['total_usage']- old_result['cpu_stats']['cpu_usage']['total_usage']
elifcollect_item == 'cpu_system_uasge':
result=new_result['cpu_stats']['system_cpu_usage'] -old_result['cpu_stats']['system_cpu_usage']
elifcollect_item == 'cpu_percent':
cpu_total_usage=new_result['cpu_stats']['cpu_usage']['total_usage'] -old_result['cpu_stats']['cpu_usage']['total_usage']
cpu_system_uasge=new_result['cpu_stats']['system_cpu_usage'] - old_result['cpu_stats']['system_cpu_usage']
cpu_num=len(old_result['cpu_stats']['cpu_usage']['percpu_usage'])
result=round((float(cpu_total_usage)/float(cpu_system_uasge))*cpu_num*100.0,2)
elifcollect_item == 'mem_usage':
result=new_result['memory_stats']['usage']
elifcollect_item == 'mem_limit':
result=new_result['memory_stats']['limit']
elifcollect_item == 'mem_percent':
mem_usage=new_result['memory_stats']['usage']
mem_limit=new_result['memory_stats']['limit']
result=round(float(mem_usage)/float(mem_limit)*100.0,2)
#network_rx_packets=new_result['network']['rx_packets']
#network_tx_packets=new_result['network']['tx_packets']
elifcollect_item == 'network_rx_bytes':
network_check_command="""docker exec %s ifconfigeth0|grep bytes|awk -F ':' '{print $2,$3}'|awk -F '(' '{print $1,$2}'|awk -F')' '{print $1}'|awk '{print "{\\"rx\\":"$1",\\"tx\\":"$2"}"}'"""%container_name
network_old_result=eval(((subprocess.Popen(network_check_command,shell=True,stdout=subprocess.PIPE)).stdout.readlines()[0]).strip('\n'))
time.sleep(1)
network_new_result=eval(((subprocess.Popen(network_check_command,shell=True,stdout=subprocess.PIPE)).stdout.readlines()[0]).strip('\n'))
#unitKB
result=int(network_new_result['rx']) - int(network_old_result['rx'])
elifcollect_item == 'network_tx_bytes':
network_check_command="""docker exec %s ifconfigeth0|grep bytes|awk -F ':' '{print $2,$3}'|awk -F '(' '{print $1,$2}'|awk -F')' '{print $1}'|awk '{print"{\\"rx\\":"$1",\\"tx\\":"$2"}"}'"""%container_name
network_old_result=eval(((subprocess.Popen(network_check_command,shell=True,stdout=subprocess.PIPE)).stdout.readlines()[0]).strip('\n'))
time.sleep(1)
network_new_result=eval(((subprocess.Popen(network_check_command,shell=True,stdout=subprocess.PIPE)).stdout.readlines()[0]).strip('\n'))
result=int(network_new_result['tx']) - int(network_old_result['tx'])
returnresult
if __name__ == "__main__":
null='null'
docker_client = Client(base_url='unix://var/run/docker.sock',version='1.17')
container_name=sys.argv[1]
collect_item=sys.argv[2]
printcheck_container_stats(container_name,collect_item)
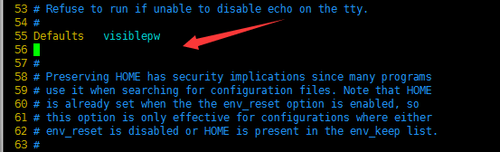
1.4修改配置文件
定義key
在/etc/zabbix/zabbix_agentd.conf
55行修改如下
Defaults visiblepw
最後添加
UserParameter=zabbix_low_discovery[*],/bin/bash/usr/local/zabbix/bin/zabbix_low_discovery.sh $1
UserParameter=docker_stats[*],sudo/usr/local/zabbix/bin/zabbix_monitor_docker.py $1 $2
重啓agent
/etc/init.d/zabbix-agentrestart
1.5 修改權限使zabbix用戶能無密碼訪問docker
echo "zabbix ALL=NOPASSWD:ALL">>/etc/sudoers
55行
Defaults visiblepw
1.6添加模板
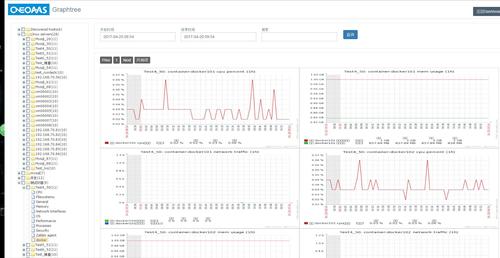
Docker監控到此結束 下面是效果圖
模板在附件中:自取!